One threat actor responsible for 83% of recent Ivanti RCE attacks
Source: Bleeping Computer

Overview
Threat intelligence observations show that a single threat actor is responsible for most of the active exploitation of two critical vulnerabilities in Ivanti Endpoint Manager Mobile (EPMM), tracked as CVE‑2026‑21962 and CVE‑2026‑24061.
Both flaws have been flagged as actively exploited in zero‑day attacks in Ivanti’s security advisory, where the company also announced hotfixes. The vulnerabilities received a critical severity rating and allow an attacker to inject code without authentication, leading to remote code execution (RCE) on vulnerable systems.
Threat Actor Activity
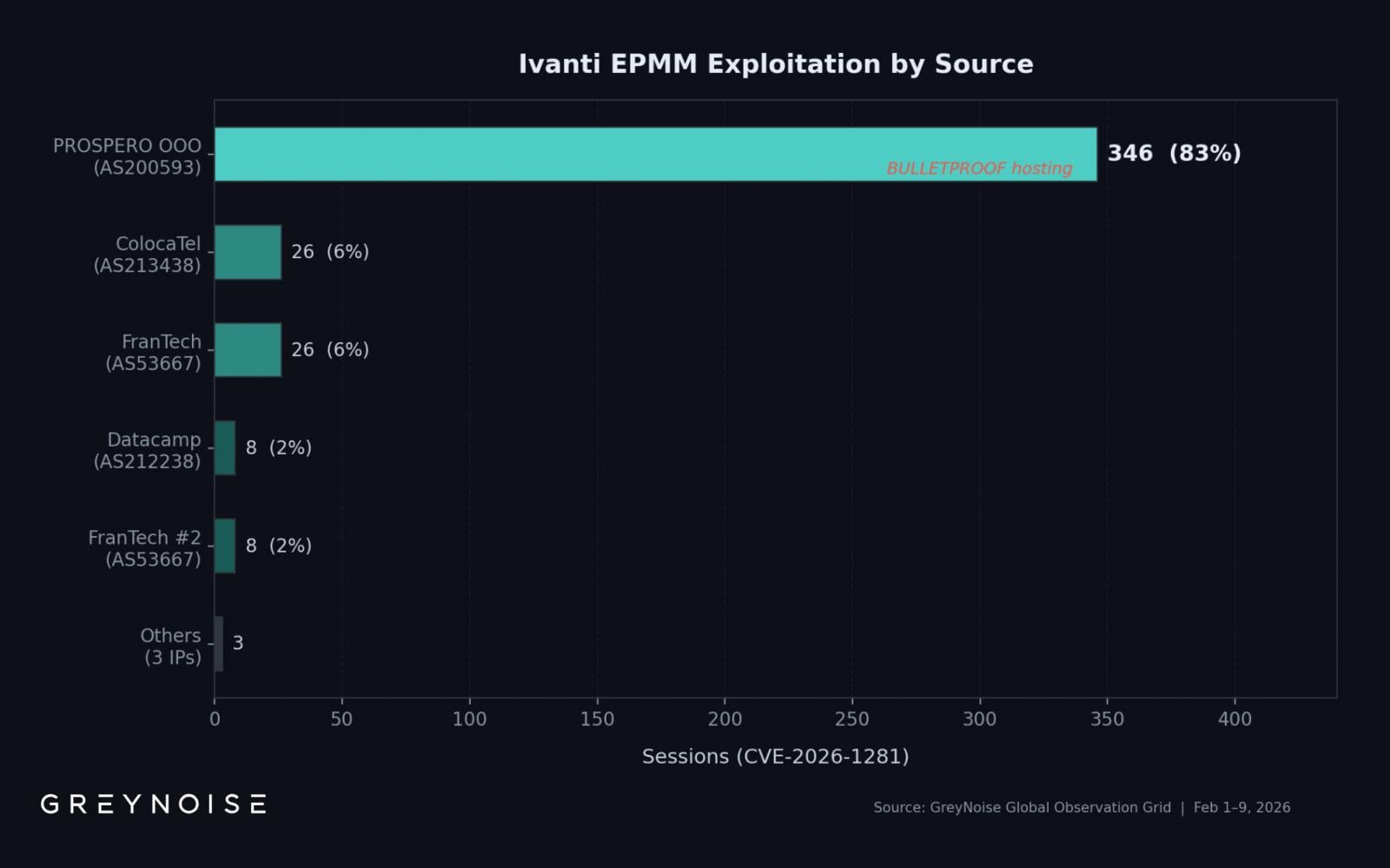
- GreyNoise identified a single IP address hosted on bullet‑proof infrastructure that accounts for over 83 % of exploitation activity related to the two vulnerabilities.
- Between February 1–9, GreyNoise observed 417 exploitation sessions from 8 unique source IPs, centered on CVE‑2026‑21962 and CVE‑2026‑24061.
- The highest‑volume source, 193.24.123.42, is hosted by PROSPERO OOO (AS200593), a bullet‑proof autonomous system used to target various software products.
- A sharp spike occurred on February 8, with 269 recorded sessions in a single day—almost 13 × the daily average of 22 sessions.
- Of the 417 sessions, 354 (85 %) used OAST‑style DNS callbacks to verify command‑execution capability, indicating initial‑access broker activity.
Additional Indicators
- Several published IoCs include IP addresses for Windscribe VPN (185.212.171.0/24), seen in GreyNoise telemetry scanning Oracle WebLogic instances, but not associated with Ivanti exploitation.
- Researchers note that the PROSPERO OOO IP “is not on widely published IOC lists, meaning defenders blocking only published indicators are likely missing the dominant exploitation source.”
Exploitation Scope
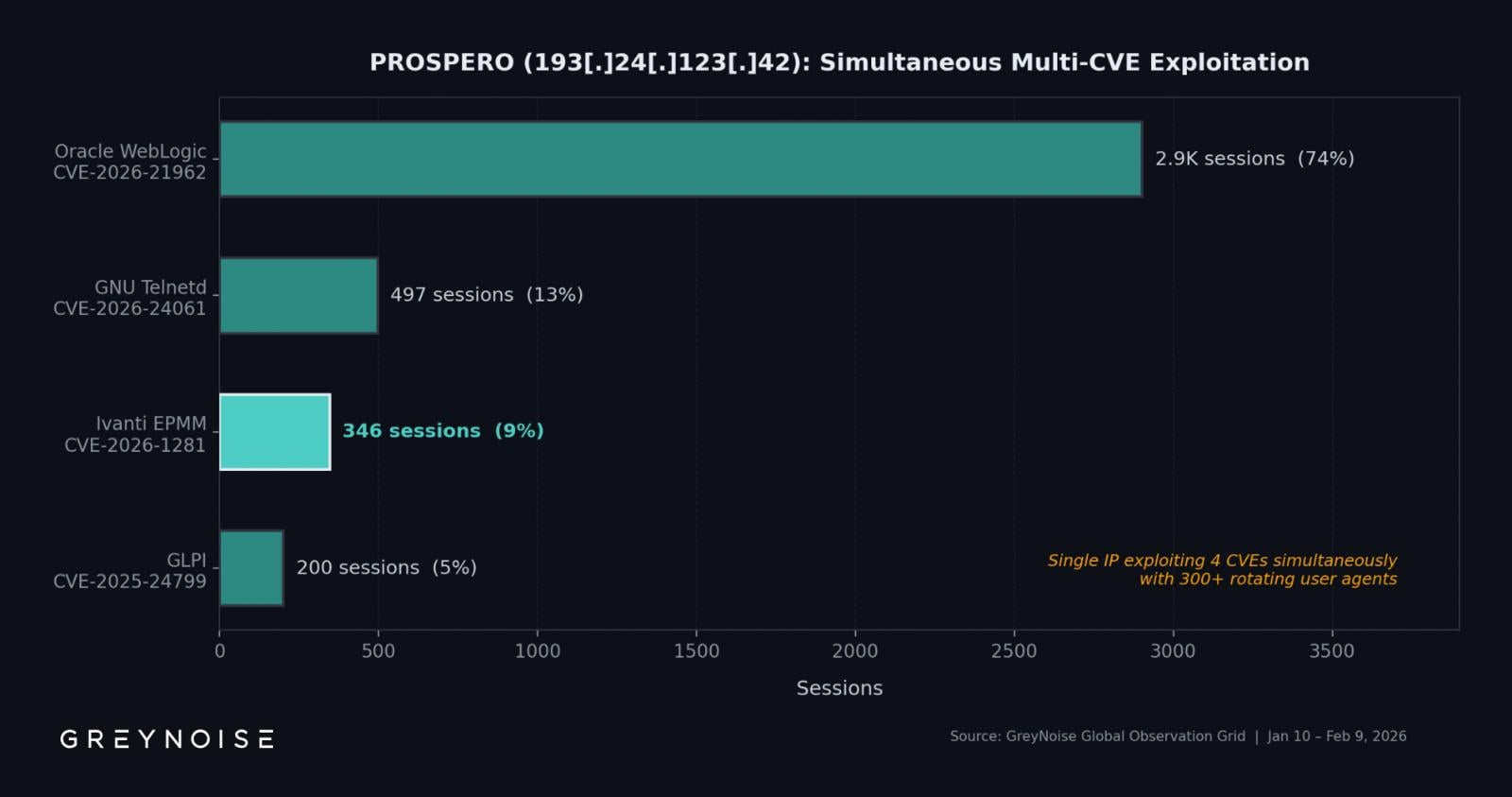
The same IP address simultaneously exploited three additional vulnerabilities:
| Vulnerability | Product | Sessions |
|---|---|---|
| CVE‑2026‑21962 | Oracle WebLogic | 2,902 |
| CVE‑2026‑24061 | GNU Inetutils Telnetd | 497 |
| CVE‑2025‑24799 | GLPI | (not specified) |
Exploitation activity appears fully automated, rotating between 300 user agents.
Mitigation Recommendations
-
Ivanti’s interim fixes for CVE‑2026‑1281 and CVE‑2026‑1340 are not permanent. The company plans to release complete patches in the first quarter of this year with EPMM version 12.8.0.0.
-
Until the full patch is available, it is recommended to use the following RPM packages:
- RPM 12.x.0.x for EPMM versions 12.5.0.x, 12.6.0.x, and 12.7.0.x
- RPM 12.x.1.x for EPMM versions 12.5.1.0 and 12.6.1.0
(See Ivanti’s security advisory for details.)
-
The vendor suggests the most conservative approach: build a replacement EPMM instance and migrate all data. Instructions are available here.