Proactive strategies for cyber resilience with Wazuh
Source: Bleeping Computer
Why Traditional Reactive Security No Longer Suffices
- Evolving threat landscape – New attack vectors appear faster than defenses can be updated.
- Increased attack frequency – Organizations face more frequent and sophisticated incidents.
- Higher business impact – Downtime and data loss directly affect revenue and reputation.
These trends demonstrate that a purely reactive approach cannot protect against today’s threats.
Proactive Cyber‑Resilience Strategy
To stay ahead, organizations should adopt a proactive stance that focuses on:
- Early detection – Identify malicious activity before it escalates.
- Rapid response – Automate containment and remediation actions.
- Continuous adaptation – Evolve defenses as threats change.
How Wazuh Enables Proactive Resilience
Wazuh is an open‑source security platform that combines SIEM (Security Information and Event Management) and XDR (Extended Detection and Response) capabilities:
| Capability | What It Provides | Benefit |
|---|---|---|
| Log collection & analysis | Centralized ingestion of logs from endpoints, cloud, containers, and network devices. | Full visibility across the environment. |
| Threat detection | Real‑time rule‑based alerts, anomaly detection, and integration with threat intelligence feeds. | Early identification of attacks. |
| Incident response | Automated playbooks, remote command execution, and integration with orchestration tools. | Faster containment and remediation. |
| Compliance & reporting | Pre‑built templates for PCI‑DSS, GDPR, HIPAA, and more. | Simplifies audit preparation. |
| Scalability | Distributed architecture with agents on any OS and a central manager. | Supports growth from small teams to large enterprises. |
By leveraging these features, Wazuh helps organizations:
- Detect threats earlier and with higher fidelity.
- Respond to incidents more efficiently through automation.
- Continuously adapt security controls as the threat landscape evolves.
Takeaway: Transitioning from reactive security to a proactive, resilience‑focused approach is essential in today’s threat environment. Wazuh provides the open‑source tools needed to build that resilience—detecting threats early, responding swiftly, and evolving defenses over time.
Cyber Resilience Beyond Prevention
A resilient organization is not defined solely by its ability to prevent attacks, but by how quickly it can identify, contain, and recover from them while maintaining operations. Achieving this level of preparedness requires security platforms that provide continuous security data, real‑time detection, and rapid incident‑response capabilities.
In practical terms, cyber resilience depends on a set of core, proactive strategies that guide security operations:
- Visibility across your environment – Comprehensive visibility across endpoints, servers, applications, networks, and cloud workloads is essential for operational readiness. It enables security teams to understand normal behavior, confirm monitoring coverage, and ensure response readiness before incidents occur.
- Early threat detection – Anticipating malicious activity at an early stage helps prevent attackers from establishing persistence and reduces the overall impact of an incident. By continuously correlating security data and system events, security teams can identify threats before they develop into full‑scale compromises.
- Rapid incident response – Coordinated and automated incident‑response capabilities enable organizations to contain threats swiftly, limit operational disruption, and maintain critical business functions during active cyber incidents.
- Recovery and continuous improvement – Cyber resilience depends on the ability to recover quickly from incidents while continuously strengthening security controls and processes. Insights gained from incidents, detections, and assessments help organizations fortify defenses and reduce future risk.
Achieving Cyber Resilience with Wazuh
Wazuh helps organizations put cyber resilience into practice by delivering centralized visibility, real‑time threat detection, automated response, IT hygiene, and continuous assessment of security posture across IT environments. This section explores how security teams can operationalize cyber‑resilience strategies using Wazuh.
Comprehensive Visibility
The Wazuh SIEM and XDR provide centralized visibility into workloads across virtualized, on‑premises, cloud‑based, and containerized environments by continuously collecting and analyzing security data. The Wazuh agent can be deployed on Linux, Windows, macOS, and other supported operating systems to collect security data, which is forwarded to the Wazuh server. Wazuh also supports syslog and agentless monitoring for network devices and systems where agents cannot be installed, ensuring monitoring coverage and operational readiness.
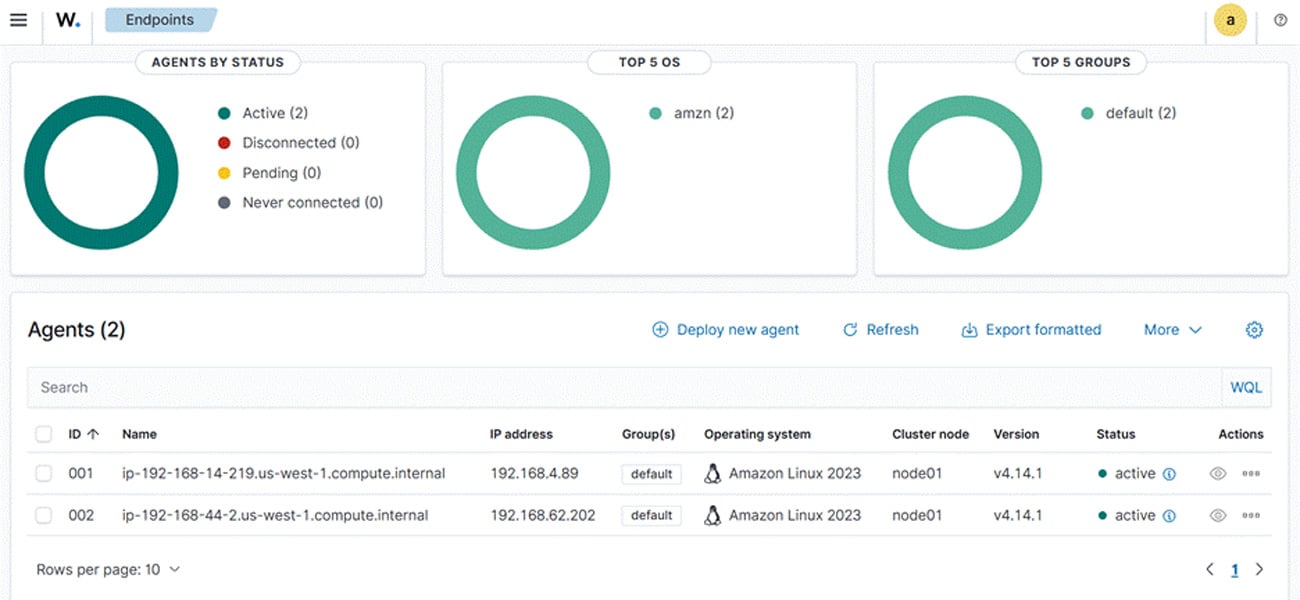
Wazuh Endpoints dashboard
Detection of Suspicious Activity
Wazuh enables early detection by correlating security data from multiple sources, allowing security teams to identify malicious behavior in its early stages. It analyzes logs collected from various endpoints, extracts relevant information, and applies detection rules to match specific patterns. By leveraging capabilities such as log‑data analysis, malware detection, and File Integrity Monitoring (FIM), Wazuh can detect anomalies, file changes, and indicators of compromise across endpoints. Security analysts can also conduct threat hunting by proactively analyzing logs, endpoint telemetry, and system behavior to uncover hidden or emerging threats.
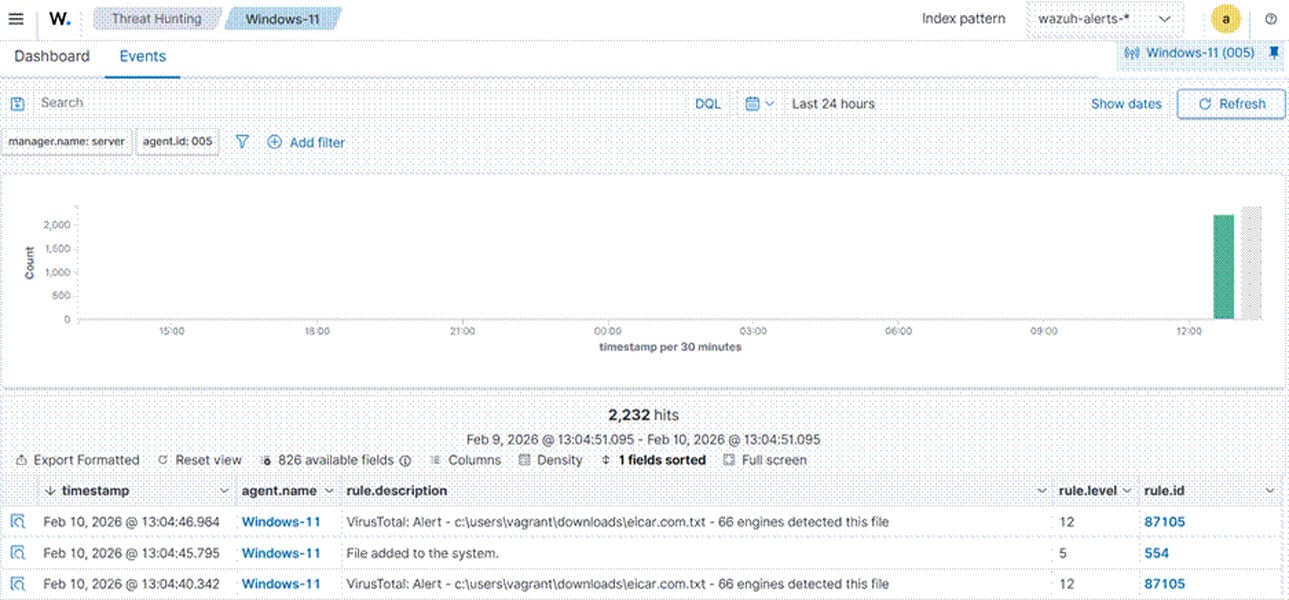
Wazuh Threat Hunting dashboard
Automated Incident Response
Wazuh provides an incident‑response capability that automatically responds to detected threats. Security teams can configure custom response actions—such as blocking malicious IP addresses, terminating suspicious processes, or disabling compromised user accounts. Automating response actions ensures that high‑priority incidents are addressed and remediated in a timely and consistent manner.
In the example below, Wazuh is used to detect and automatically remove the Cephalus ransomware executable from a monitored endpoint.
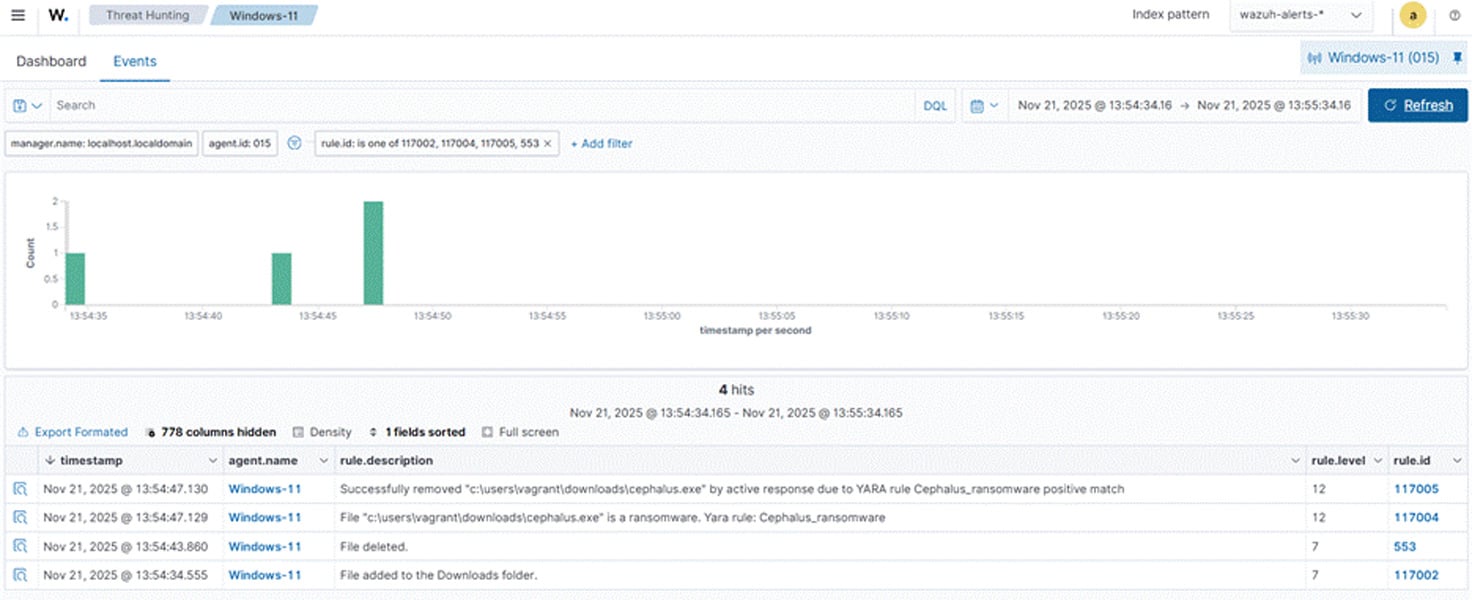
Detecting and responding to Cephalus ransomware with Wazuh
Artificial Intelligence (AI)
Wazuh offers a Wazuh AI Analyst service for Wazuh Cloud users, providing AI‑assisted analysis and insights. This service combines Wazuh Cloud with advanced machine‑learning models to process security data at scale and generate actionable insights that strengthen an organization’s overall security posture.
Wazuh also showcased integration of the Claude LLM into the dashboard in the blog post “Leveraging Claude Haiku in the Wazuh dashboard for LLM‑Powered insights.” The integration adds a chat‑assistant feature that delivers contextual, summarized insights and expert‑level analysis to aid incident investigation.
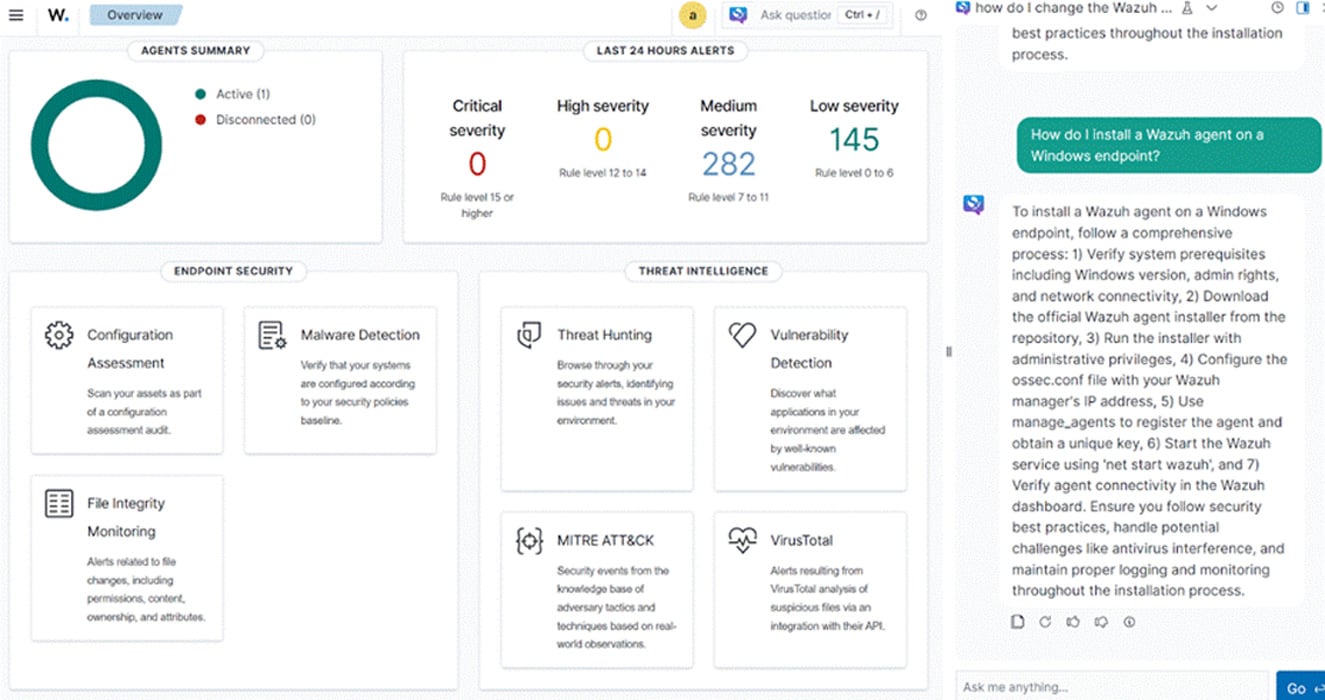
Wazuh dashboard with LLM‑powered insights
Improved IT Hygiene and Security Posture
Cyber resilience requires good IT hygiene and a hardened security baseline. Addressing issues such as poor patching practices and insecure configurations proactively reduces the attack surface, limiting opportunities for attackers. Wazuh improves IT hygiene through continuous asset visibility, vulnerability detection, and configuration assessment.
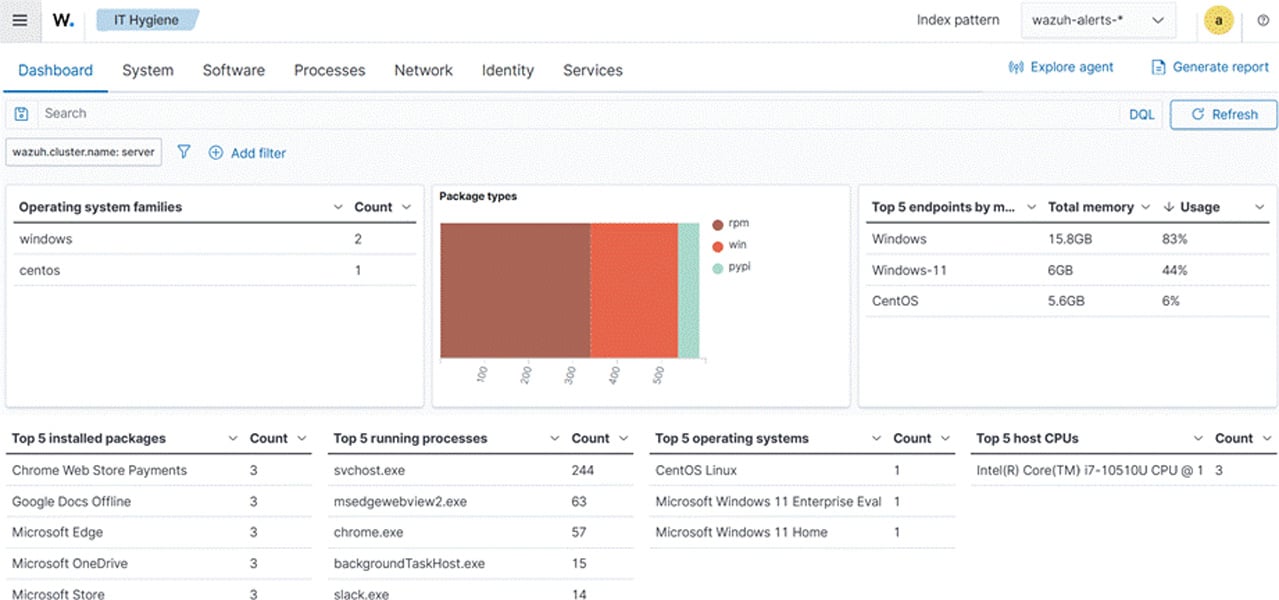
Wazuh IT Hygiene dashboard
The Wazuh SIEM and XDR offer vulnerability detection and security‑configuration assessment capabilities. The vulnerability detection engine identifies known CVEs across operating systems and installed software by using threat‑intelligence data from the Wazuh CTI platform.
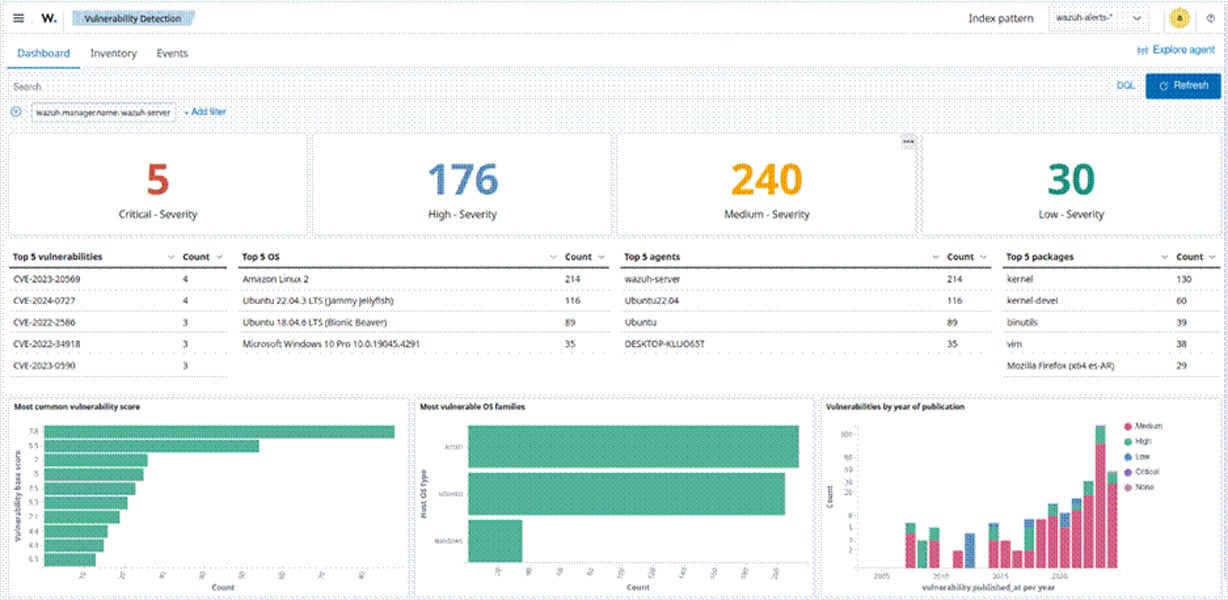
Wazuh Vulnerability Detection dashboard
The platform aggregates vulnerability data from various sources, including OS vendors and public vulnerability databases.
Wazuh also provides a Security Configuration Assessment (SCA) capability that evaluates systems against security standards and best practices—such as the Center for Internet Security (CIS) benchmarks—to identify misconfigurations and flaws.
Wazuh CTI Platform
Wazuh provides out‑of‑the‑box rulesets mapped to regulatory standards, enabling organizations to identify gaps in compliance against frameworks such as PCI DSS, GDPR, HIPAA, and NIST 800‑53.
By combining vulnerability detection, configuration assessment, and regulatory compliance in a single platform, Wazuh supports continuous security‑posture improvement and long‑term cyber resilience.
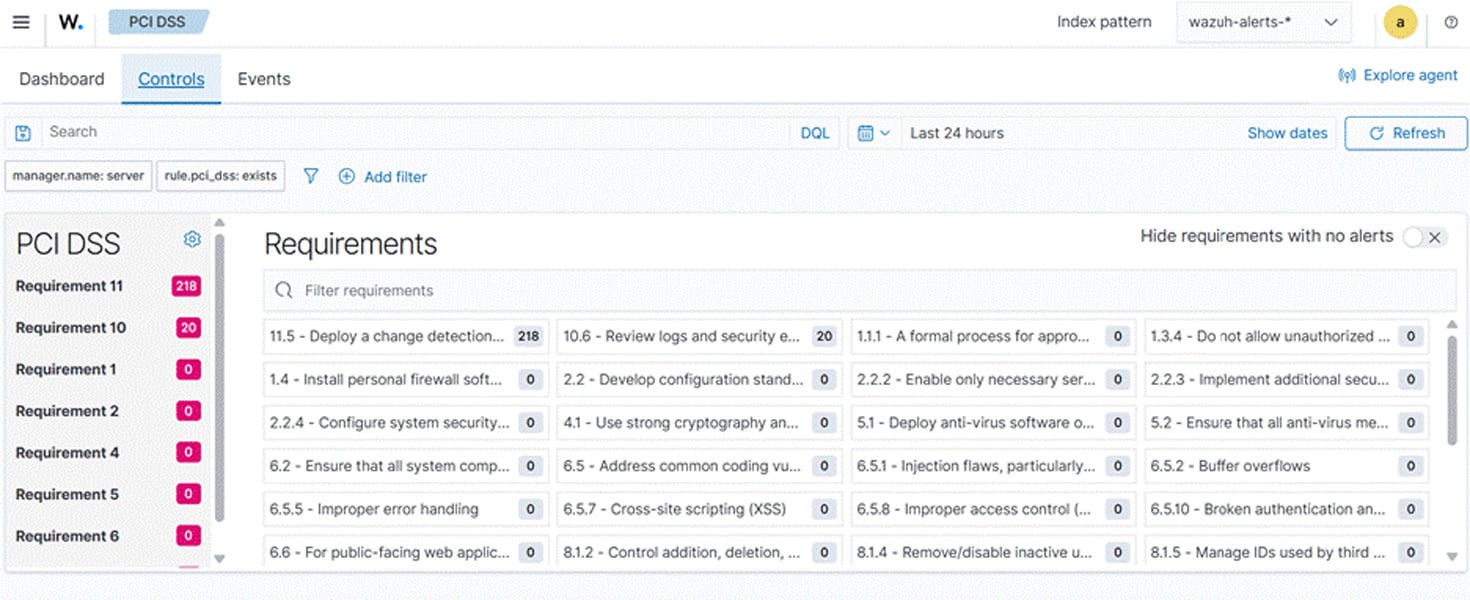
Wazuh PCI DSS dashboard
Continuous improvement and adaptability:
Wazuh supports continuous improvement by providing rich security data, dashboards, and reporting that allow security teams to analyze trends and identify recurring weaknesses across their environment. The platform also enables organizations to develop custom decoders and rules tailored to their unique log sources, applications, and environments, thereby improving detection accuracy and reducing false positives. This ensures that alerts and correlations remain relevant as infrastructure and attack patterns evolve.
As an open‑source platform, Wazuh provides the flexibility to adapt the solution to specific needs rather than conforming to a fixed security model. Continuous enhancements driven by an active community and ongoing development enable organizations to evolve their security capabilities and maintain long‑term cyber resilience.
Conclusion
Cyber resilience goes beyond merely preventing cyber‑attacks or relying on isolated security controls and reactive incident handling. It requires:
- Continuous visibility
- Timely threat detection
- Coordinated incident response
- The ability to recover and adapt as threats, environments, and attack techniques evolve
Wazuh unifies threat detection, automated response, and compliance within a single, extensible platform. This shifts organizations from a reactive defense posture to sustained cyber resilience.
Discover more about Wazuh by exploring their documentation and joining their growing community of professionals.
Sponsored and written by Wazuh.