Police arrest seller of JokerOTP MFA passcode capturing tool
Source: Bleeping Computer

The Netherlands Police have arrested a 21‑year‑old man from Dordrecht, suspected of selling access to the JokerOTP phishing automation tool that can intercept one‑time passwords (OTP) for hijacking accounts. He is the third suspect arrested after a three‑year investigation that dismantled the JokerOTP phishing‑as‑a‑service (PhaaS) operation in April 2025. Earlier arrests included the platform’s developer and a co‑developer who used the aliases spit and defone123.
JokerOTP Phishing‑as‑a‑Service Operation
In two years, the JokerOTP service allegedly caused at least $10 million in financial losses across more than 28,000 attacks targeting users in 13 countries.
The seller, whose name has not been disclosed, advertised access via a Telegram account, offering license keys to cybercriminals. Subscribers could configure the tool to automate calls to victims and capture temporary codes or other sensitive data (PIN codes, card data, social security numbers).
The JokerOTP bot could target users of:
- PayPal
- Venmo
- Coinbase
- Amazon
- Apple
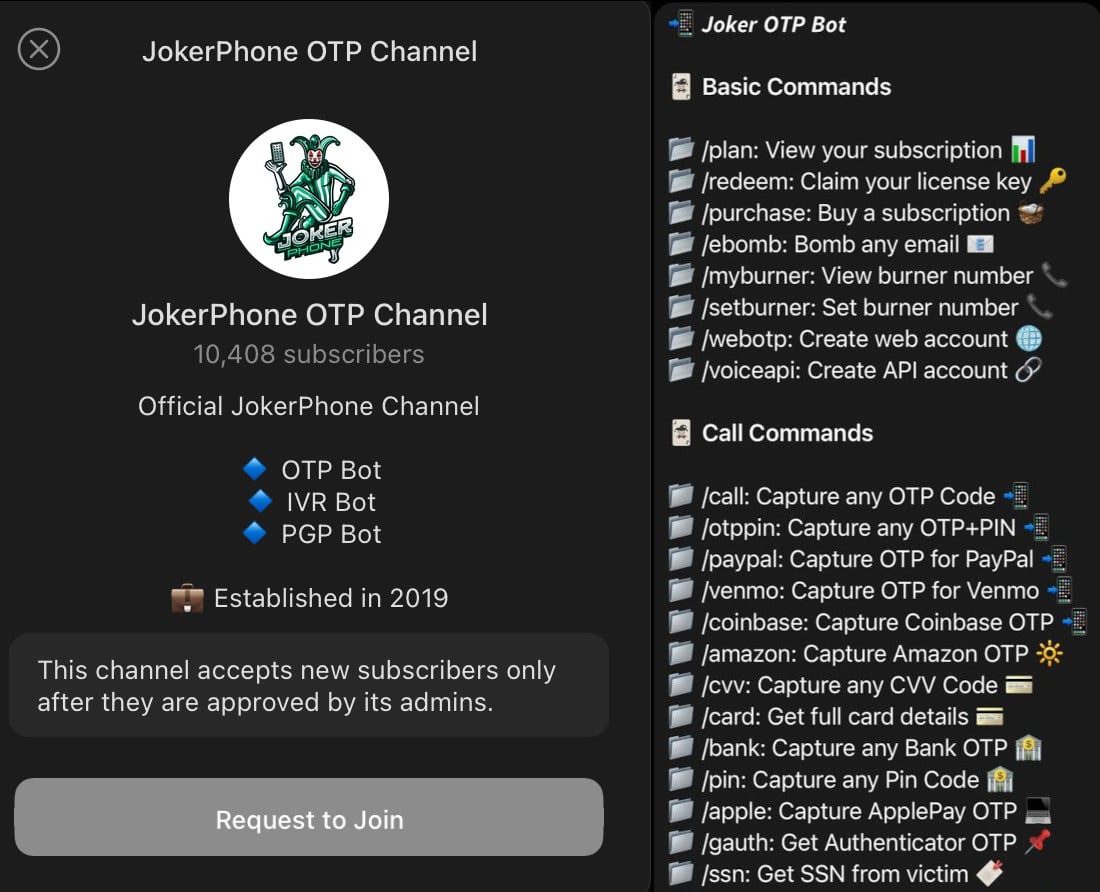
Commands for the JokerOTP Bot
source: vxdb
- (List of commands was not provided in the source; include any known commands here if available.)
How the Attack Works
OTPs are temporary codes that add an extra security layer during account authentication. They are sent via SMS, email, or generated by an app, and have short expiration times. Typically, attackers use stolen credentials—obtained from malware infections or dark‑web purchases—to attempt a login. The legitimate user receives the OTP needed to complete the login.
JokerOTP automates a phone call to the victim, posing as a representative of the targeted service and requesting the OTP. Because the call coincides with the delivery of the authentication code, many users fail to recognize the scam.
“Victims were automatically called by the bot and informed that criminals were attempting to gain access to their account,” explained Anouk Bonekamp, team leader of Cybercrime Oost‑Brabant.
“The bot then asked them to enter the one‑time password. Victims, therefore, believe they are protecting themselves by cooperating and providing information.”
— Politie.nl
Depending on the compromised account, threat actors may make unauthorized purchases, transfer funds, or hijack the account entirely.
Police Investigation and Recommendations
The investigation remains ongoing. Dozens of JokerOTP bot buyers in the Netherlands have been identified and will be prosecuted in due time. Police emphasize that victims should not feel ashamed for falling for such sophisticated traps and should stay alert for signs of fraud, such as urgency and requests for sensitive information (PINs, passwords).
Recommendations for users:
- Check for data breaches affecting you on Have I Been Pwned.
- Use the Netherlands Police’s CheckJack service to monitor compromised credentials.
- Be skeptical of unsolicited phone calls asking for OTPs, even if they appear to come from a trusted service.
- Enable authentication methods that do not rely solely on SMS or email OTPs, such as hardware security keys or authenticator apps.