LummaStealer infections surge after CastleLoader malware campaigns
Source: Bleeping Computer
# LummaStealer Resurgence & CastleLoader
A surge in **LummaStealer** infections has been observed, driven by social‑engineering campaigns that leverage the **ClickFix** technique to deliver the **CastleLoader** malware.
## Background
- **LummaStealer** (also known as **LummaC2**) is an infostealer‑as‑a‑service (MaaS) platform.
- In **May 2025** the operation was disrupted when tech firms and law‑enforcement seized **2,300 domains** and dismantled its central command structure.
- Source: [BleepingComputer – 2,300 domains seized](https://www.bleepingcomputer.com/news/security/lumma-infostealer-malware-operation-disrupted-2-300-domains-seized/)
Infostealing malware targets a wide range of sensitive data, including:
- Browser credentials & cookies
- Cryptocurrency wallet details
- Documents, session cookies, authentication tokens
- VPN configurations & account data
Although the crackdown severely impacted LummaStealer, the MaaS operation **resumed in July 2025**.
- Source: [BleepingComputer – Lumma returns](https://www.bleepingcomputer.com/news/security/lumma-infostealer-malware-returns-after-law-enforcement-disruption/)
## Recent Findings (Bitdefender)
A new Bitdefender report warns that LummaStealer activity **scaled dramatically between Dec 2025 and Jan 2026**, now being delivered through the **CastleLoader** malware and increasingly relying on ClickFix techniques.
> “At the core of many of these campaigns is CastleLoader, which plays a central role in helping LummaStealer spread through delivery chains. Its modular, in‑memory execution model, extensive obfuscation, and flexible command‑and‑control communication make it well‑suited to malware distribution of this scale.” – *Bitdefender researchers*
> [Read the full analysis](https://www.bitdefender.com/en-us/blog/labs/lummastealer-second-life-castleloader)
### CastleLoader Overview
- **First seen:** Early 2025
- **Delivery methods:** ClickFix, trojanized installers, fake media/game archives, pirated software sites, torrents
- **Payload families:** Stealc, RedLine, Rhadamanthys, MonsterV2, CastleRAT, SectopRAT, NetSupport RAT, WarmCookie
- **Implementation:** Heavily obfuscated AutoIT or Python script that decrypts, loads, and executes the LummaStealer payload **entirely in memory**
- **Obfuscation techniques:**
- Dictionary‑based renaming of variables/functions
- Runtime‑decoded strings
- Junk code & dead branches
- Trivial arithmetic/logic operations
#### Typical Infection Chain
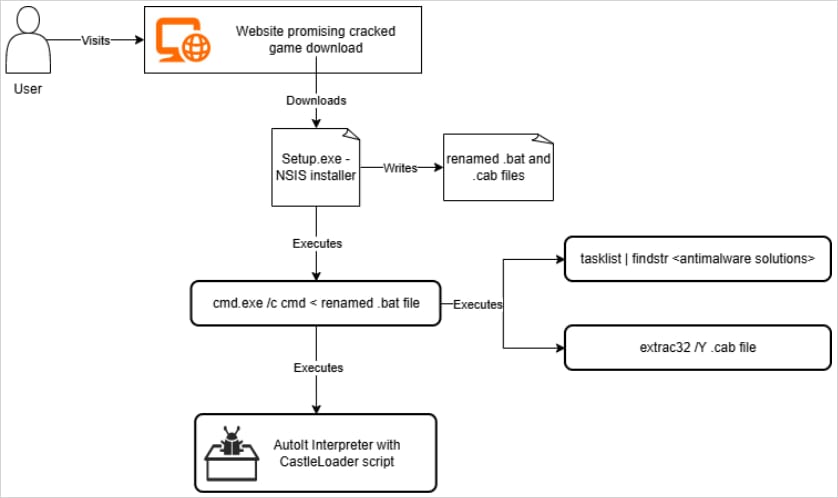
*Source: Bitdefender*
#### Persistence Mechanism
1. Copies the malicious AutoIT script to a persistence path.
2. Copies the interpreter to a separate location.
3. Creates an **Internet Shortcut** (`.url`) in the **Startup** folder that launches the interpreter with the script as an argument.
#### Network‑Based Indicator
CastleLoader deliberately initiates a **failed DNS lookup** for a non‑existent domain. The resulting DNS failure can be used as a detection indicator.
#### Early C2 Connection
Recorded Future’s Insikt Group noted that a domain in CastleLoader’s infrastructure acted as a **C2 server for LummaStealer**, confirming an early link between the two operations.
- Source: [Recorded Future – Graybravos & CastleLoader](https://www.recordedfuture.com/research/graybravos-castleloader-activity-clusters-target-multiple-industries)
### Geographic Reach
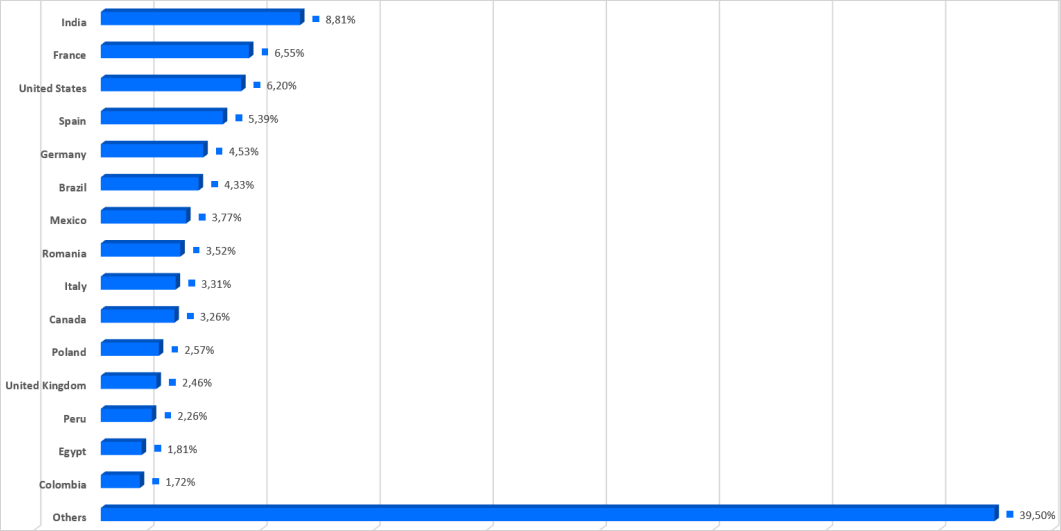
*Countries targeted in LummaStealer campaigns – Source: Bitdefender*
## ClickFix Vector
- Users encounter a **fake CAPTCHA/verification page** that instructs them to run a PowerShell command already copied to the clipboard.
- The command fetches a malicious script from the attacker’s server and executes it locally.
- In many cases the fetched script is **CastleLoader**, which subsequently loads **LummaStealer**.
## Mitigation Recommendations (Bitdefender)
| Recommendation | Details |
|----------------|---------|
| **Avoid untrusted downloads** | Do not download or run executables (`.exe`) from unofficial sources, especially pirated software, cracks, or “unlocked” tools. |
| **Beware of unexpected PowerShell commands** | Never execute PowerShell or command‑line snippets you do not fully understand, especially when prompted by a website verification page. |
| **Use ad‑blocking & safe‑search** | Hide promoted results on Google Search with an ad blocker to reduce exposure to malicious ads. |
| **Employ endpoint protection** | Ensure your security suite can detect in‑memory execution, DNS anomalies, and known CastleLoader indicators. |
| **Keep software patched** | Regularly update OS, browsers, and security tools to mitigate exploitation of known vulnerabilities. |
---
### Sponsored Content
[](https://www.wiz.io/lp/gitlab-security-best-practices-cheat-sheet?utm_source=bleepingcomputer&utm_medium=display&utm_campaign=FY26Q4_INB_FORM_GitLab-Security-Best-Practices-Cheat-Sheet&sfcid=701Vh00000Wn1rmIAB&utm_term=FY27-bleepingcomputer-article-970x250&utm_content=GitLab-Best-Practices)
---
The future of IT infrastructure is here
Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide you’ll learn how to:
- Reduce hidden manual delays
- Improve reliability through automated response
- Build and scale intelligent workflows on top of the tools you already use