AMOS infostealer targets macOS through a popular AI app
Source: Bleeping Computer

# Infostealers & the Cybercrime Economy
Infostealers such as **Atomic MacOS Stealer (AMOS)** are far more than standalone malware.
They act as foundational components of a mature cyber‑crime ecosystem that harvests, trades, and operationalises stolen digital identities.
## Why Modern Stealers Matter
- **Data‑collection engines** – They continuously gather credentials, session tokens, and financial data at scale.
- **Underground marketplaces** – The harvested data is bought and sold to fuel account takeovers, fraud, and follow‑on intrusions.
- **Adaptive social engineering** – Attackers exploit current technology trends, trusted platforms, popular software, search engines, and emerging AI ecosystems to trick users into executing the malware themselves.
This blend of industrialised data monetisation and flexible social engineering makes infostealers one of the most reliable and scalable entry points in today’s cyber‑crime landscape.
## Recent Findings
The **2026 Enterprise Infostealer Identity Exposure** report from Flare highlights:
- The growing dominance of infostealers within the cyber‑crime economy.
- The expanding impact of identity exposure on organisations of all sizes.
[Read the full report here](https://flare.io/learn/resources/2026-enterprise-infostealer-identity-exposure/).
## What We’ll Cover
In this article we use the **AMOS** infostealer as a case study to explore:
1. **Evolution** – How the malware has changed over time.
2. **Operational model** – The infrastructure and tactics behind its data‑collection engine.
3. **Real‑world activity** – Notable campaigns and incidents across its active years.
Stay tuned for an in‑depth analysis of AMOS and its role in the modern cyber‑crime economy.How Do Infostealers Work?
Infostealers are a pivotal component of the modern cyber‑crime kill chain. By turning a single infection into a massive breach of credentials, sessions, and identities, they enable attackers to scale their operations quickly.
Typical Workflow
-
Execution on the victim’s machine
The payload runs silently after the initial infection (e.g., via phishing, malicious download, or exploit). -
System reconnaissance
- Enumerates installed browsers (Chrome, Edge, Firefox, etc.)
- Scans for password managers, crypto‑wallet files, and messaging applications
- Locates credential stores (Windows Credential Manager, macOS Keychain, Linux
gnome-keyring, etc.)
-
Data extraction
- Harvests saved passwords, API keys, and authentication tokens
- Retrieves session cookies and authentication headers
- Copies sensitive documents, spreadsheets, and configuration files
-
Data packaging & encryption
- Bundles the collected items into an archive (often ZIP or custom format)
- Encrypts or encodes the payload to evade detection during transit
-
Exfiltration
- Sends the data to attacker‑controlled infrastructure (HTTP/HTTPS, FTP, DNS tunneling, or cloud storage)
- May use multiple fallback channels to ensure successful delivery
-
Cleanup (optional)
- Deletes traces of the theft routine
- May install additional payloads for persistence or further exploitation
Key Takeaways
- Speed: Infostealers act quickly to minimize the window for detection.
- Breadth: They target a wide range of data sources, from browsers to crypto wallets.
- Stealth: Encryption and multi‑channel exfiltration help evade security tools.
Understanding this workflow is essential for building effective detection and response strategies.
ClawHavoc – The Most Recent Campaign
Source: Recent research by Koi Security
Overview
Koi Security uncovered a large‑scale supply‑chain attack named ClawHavoc that targets the OpenClaw and ClawHub ecosystem (a popular personal AI assistant). The attackers poison the skill marketplace to distribute the AMOS infostealer.
Threat Summary
| Aspect | Details |
|---|---|
| Target | OpenClaw/ClawHub skill marketplace (add‑ons for the AI assistant) |
| Malware | AMOS infostealer – designed to locate weaknesses across many technology stacks and exfiltrate credentials |
| Delivery Model | Attackers upload malicious skills that appear legitimate (e.g., crypto tools, productivity utilities, YouTube helpers, finance or Google Workspace integrations). |
| Capabilities | • Steal credentials (web, SSH, API keys) |
| • Extract crypto‑wallet data | |
| • Hijack browser sessions | |
| • Capture other sensitive PII | |
| Impact | Demonstrates how AI‑agent extension ecosystems can become high‑impact distribution channels when marketplace vetting is weak. |
Attack Flow
- Skill Publication – Malicious actors publish seemingly benign OpenClaw add‑ons.
- User Installation – Users (individuals or organizations) install the skill for its advertised functionality.
- Malware Execution – The embedded AMOS payload runs silently in the background.
- Data Harvesting – Credentials, wallet information, SSH keys, and other sensitive data are collected.
- Exfiltration – Harvested data is sent to attacker‑controlled servers.
Why It Matters
- AI hype drives rapid adoption of OpenClaw, creating a large attack surface.
- Supply‑chain trust is easily broken when marketplace vetting is insufficient.
- Credential theft at this scale can compromise personal accounts, corporate environments, and cryptocurrency assets.
Takeaways
- Verify the provenance of any OpenClaw skill before installation.
- Implement strict marketplace review processes and sandbox testing for new add‑ons.
- Monitor for anomalous credential usage and unusual network traffic from AI assistants.
- Educate users about the risks of installing third‑party extensions, especially those promising “quick wins” in finance or productivity.
This campaign underscores the need for robust security controls around AI‑driven ecosystems and their extension marketplaces.
Monitor Stealer Logs Before Attackers Strike
Flare tracks over 1 million new stealer logs each week from dark‑web markets and Telegram channels.
- Detect compromised credentials
- Detect active session cookies
- Detect corporate access before threat actors weaponize them in account‑takeover attacks
AMOS the Malware – First Sighting of AMOS
Date first observed: May 2023 (Telegram channel)
Initial Advertisement

The advertisement listed the following capabilities:
- Export passwords from the macOS Keychain
- File grabber
- System‑information collection
- macOS password exfiltration
- Browser‑session theft
- Crypto‑wallet data theft
- Full infostealer‑management suite (web panel, tests, Telegram logs, etc.)
Pricing: $1 000 / month, payable in USDT (TRC‑20), ETH, or BTC.
Evolution in the Underground
Since the first sighting, AMOS has become a commodity in the underground ecosystem. Threat actors now purchase logs harvested by AMOS (or similar infostealers) to obtain initial access for their own malicious campaigns.
Example: Dark‑Web Request for AMOS Logs
Source: Flare forum post – sign up for a free trial to view.
AMOS Modus‑Operandi
AMOS is distributed using the same vectors as many modern infostealers—phishing links, malicious email attachments, trojanized installers, and click‑bait content. In recent years, however, the campaign has evolved to exploit more sophisticated, large‑scale channels.
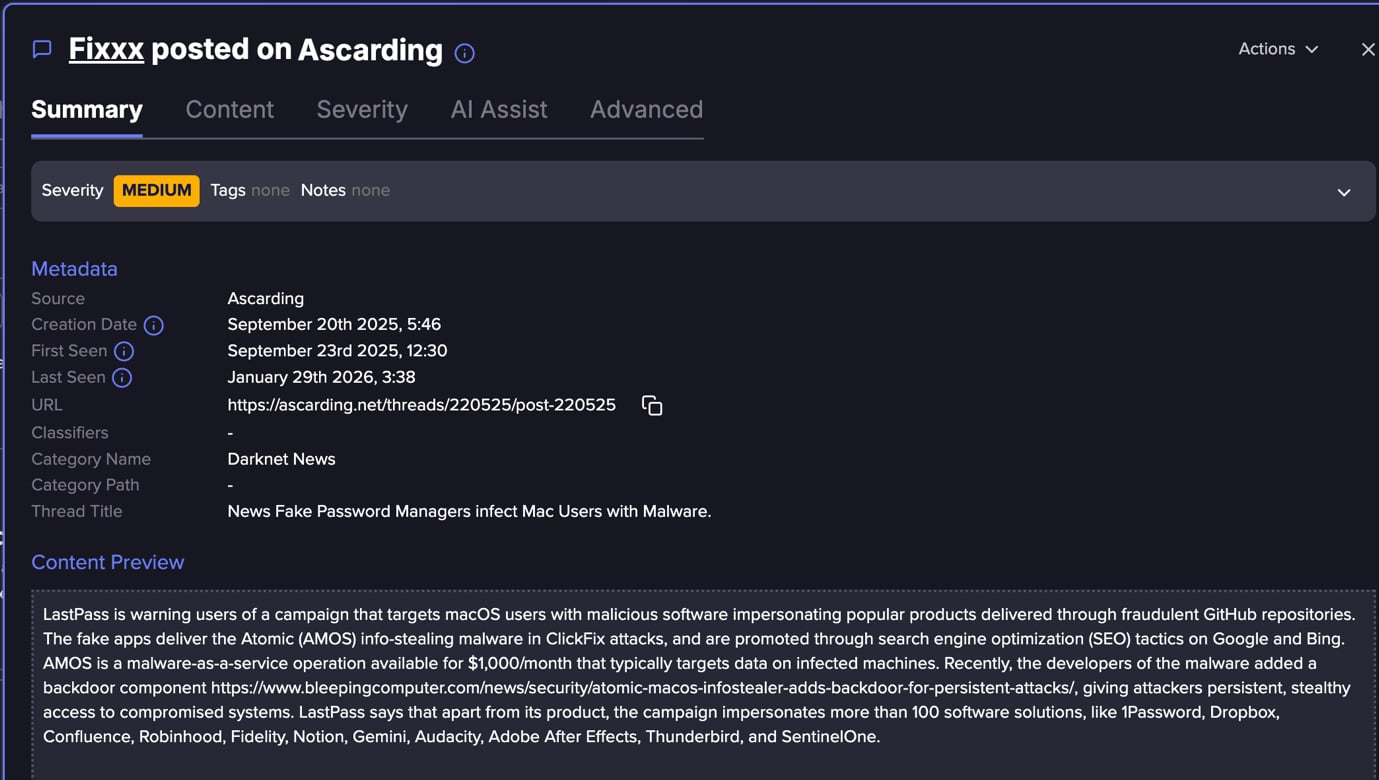
1. Targeting LastPass Users
- Underground warning: A post on a private forum flagged an active AMOS campaign aimed at LastPass users.
- Delivery method:
- Fake macOS applications are hosted in fraudulent GitHub repositories.
- Attackers impersonate >100 well‑known software brands to increase perceived legitimacy.
- Search‑engine abuse: SEO poisoning on Google and Bing pushes these malicious repos to the top of search results.
- ClickFix‑style pages: Victims are redirected to pages that socially engineer them into pasting Terminal commands, which download and execute the AMOS payload.
- Resilience: Automated account creation continuously spawns new GitHub repositories, turning trusted developer platforms and search engines into scalable malware‑distribution infrastructure.
2. AI‑Driven Dissemination Channels
ClawHavoc & ChatGPT Campaign (Dec 2025)
- Source: Huntress reported the operation — “AMOS stealer, ChatGPT, Grok, AI trust”.
- Vector: Threat actors leveraged the ChatGPT shared‑chat feature to host malicious “installation guides” on the trusted domain
chatgpt.com. - Promotion: Paid search ads (SEO poisoning/malvertising) advertised a fake “ChatGPT Atlas browser for macOS.”
- Execution: Victims were instructed to run a single Terminal command, turning the user into the execution mechanism.
- Takeaway: AI hype is weaponized to increase credibility and lure victims into executing malware.
3. Traditional Dissemination Channels
Social‑Engineering‑First Approach
| Technique | Description |
|---|---|
| Fake installers | Actors create realistic‑looking DMG images for popular software (e.g., Tor Browser, Photoshop, Microsoft Office) that bundle the AMOS stealer. |
| Malvertising | Paid ads on platforms like Google Ads redirect users to spoofed download sites that mimic legitimate vendors. |
| ClickFix / instruction‑based execution | Victims are guided to run commands themselves (e.g., dragging files into Terminal or pasting a one‑liner), avoiding the need for exploitable vulnerabilities. |
Key Points
- Brand impersonation is central—attackers copy the look‑and‑feel of trusted applications to bypass user skepticism.
- Legitimate distribution channels (GitHub, search engines, ad networks) are abused to increase reach and reduce detection.
- The shift from technical exploits to trust abuse reflects a broader trend in macOS infostealer campaigns, emphasizing social engineering over vulnerability chaining.
Bottom line: AMOS combines classic phishing tactics with modern, AI‑enhanced lures and large‑scale abuse of trusted platforms, making it a versatile and persistent threat to macOS users.
The Underground Economy Model
The AMOS ecosystem operates as a structured Malware‑as‑a‑Service (MaaS) supply chain.
- Developers (often identified on underground forums as AMOS sellers or affiliates) provide the stealer platform, updates, infrastructure components, and sometimes management panels.
- They charge a subscription—historically advertised around $1,000 / month, typically paid in cryptocurrency.
How the Chain Works
- Downstream threat actors purchase access to the stealer kit and customize lures or distribution channels (e.g., malvertising, fake installers, phishing, SEO poisoning, supply‑chain abuse, or social‑engineering campaigns).
- Their primary goal is to maximize infection volume.
- The malware’s output is a list of stolen credentials, PII, and session logs—commonly referred to as stealer logs.
- These logs become a tradable commodity on underground markets.
“Stealer logs are purchased by secondary actors such as access brokers, account‑takeover specialists, and crypto cash‑out operators, who use them for follow‑on operations—including SaaS account compromise, financial fraud, ransomware initial access, or cryptocurrency theft.”
Monetization Stages
| Stage | Actor | Primary Activity |
|---|---|---|
| Development | Malware developers | Build/maintain the stealer, add features, improve evasion |
| Distribution | Distributors | Choose targets, craft lures, run campaigns, refine social‑engineering tactics |
| Monetization | Access brokers & cash‑out operators | Buy stealer logs, sell or use them for account takeover, fraud, ransomware, etc. |
- Developers tend to stay consistent, making only incremental improvements.
- Distributors drive the visible evolution of campaigns (e.g., “AMOS is now targeting AI apps” or “AMOS campaigns are hitting LastPass users”).
- Log consumers apply established, repeatable monetization techniques.
Why Infostealers Differ from Traditional Malware
- Speed & coverage – they aim to harvest as much data as possible, as quickly as possible.
- Stealth – they focus on remaining undetected rather than on persistence, lateral movement, or destructive capabilities.
Consequently, stealer logs act as a foundational data‑supply layer for the broader cybercrime economy, enabling downstream actors to launch a variety of follow‑on attacks.
Learn more by signing up for our free trial → Flare trial page
Sponsored and written by Flare.