CTM360: Lumma Stealer and Ninja Browser malware campaign abusing Google Groups
Source: Bleeping Computer
# CTM360 Threat Report
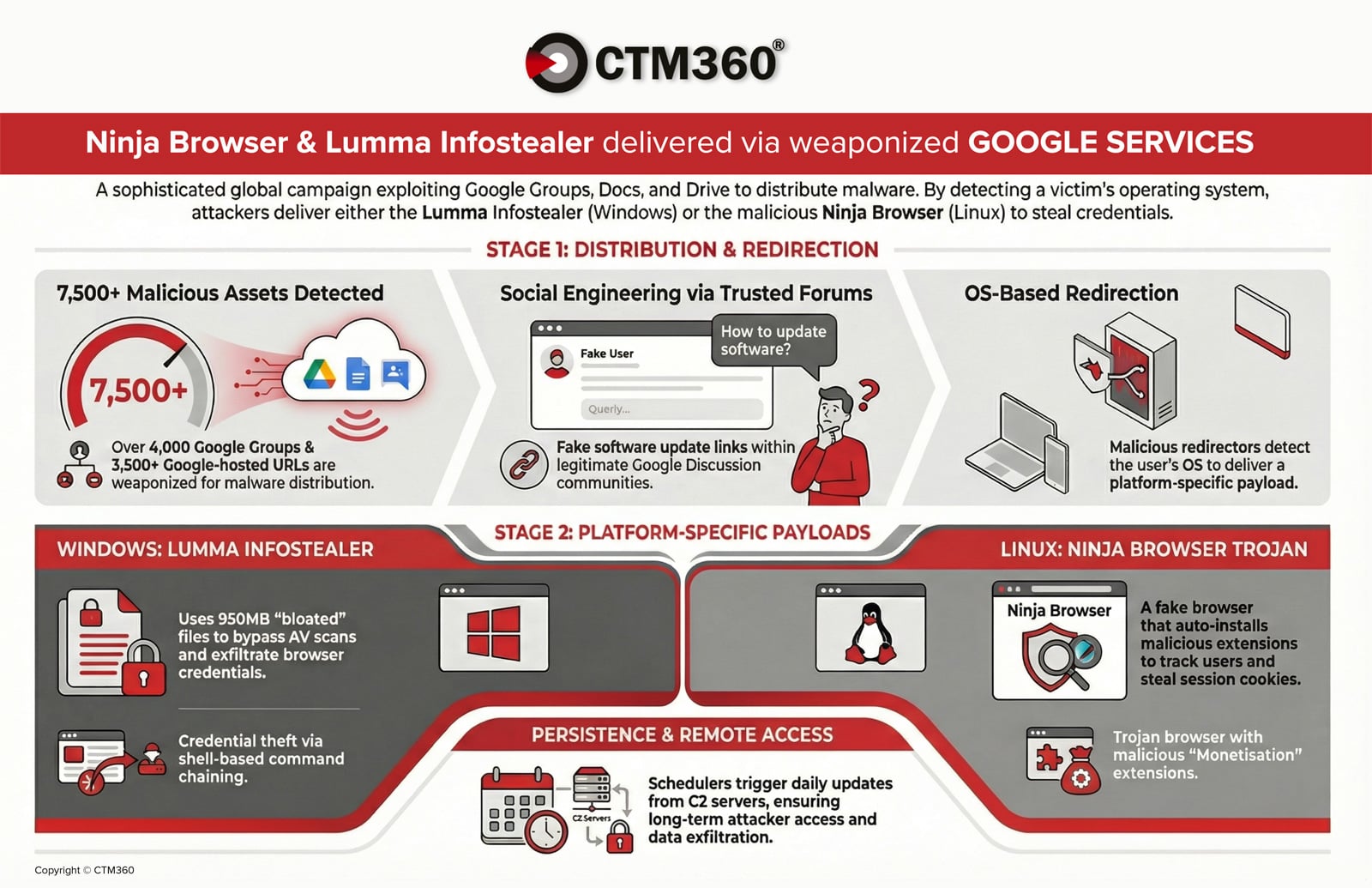
**Key Findings**
- **4,000+ malicious Google Groups** are being leveraged in an active malware campaign.
- **3,500+ Google‑hosted URLs** are used to deliver credential‑stealing payloads.
- Attackers exploit Google’s trusted ecosystem to **distribute malware** and **maintain persistent access** on compromised devices.
- The campaign is **global**; threat actors embed specific organization names and industry‑relevant keywords in posts to increase credibility and drive downloads.
**Impact**
- Organizations worldwide are at risk of credential theft and long‑term compromise.
- The use of legitimate Google services helps the malware evade traditional security controls.
**Read the full report**
[CTM360 – Ninja Browser / Lumma Infostealer Report](https://www.ctm360.com/reports/ninja-browser-lumma-infostealer)How the Campaign Works
The attack chain starts with social engineering inside Google Groups. Threat actors infiltrate industry‑related forums and post technical discussions that appear legitimate, covering topics such as:
- Network issues
- Authentication errors
- Software configurations
Within these threads, attackers embed download links disguised as:
Download {Organization_Name} for Windows 10Delivery Mechanism
- URL shorteners or Google‑hosted redirectors (Docs/Drive) are used to hide the final destination.
- The redirector detects the victim’s operating system and serves different payloads for Windows or Linux machines.
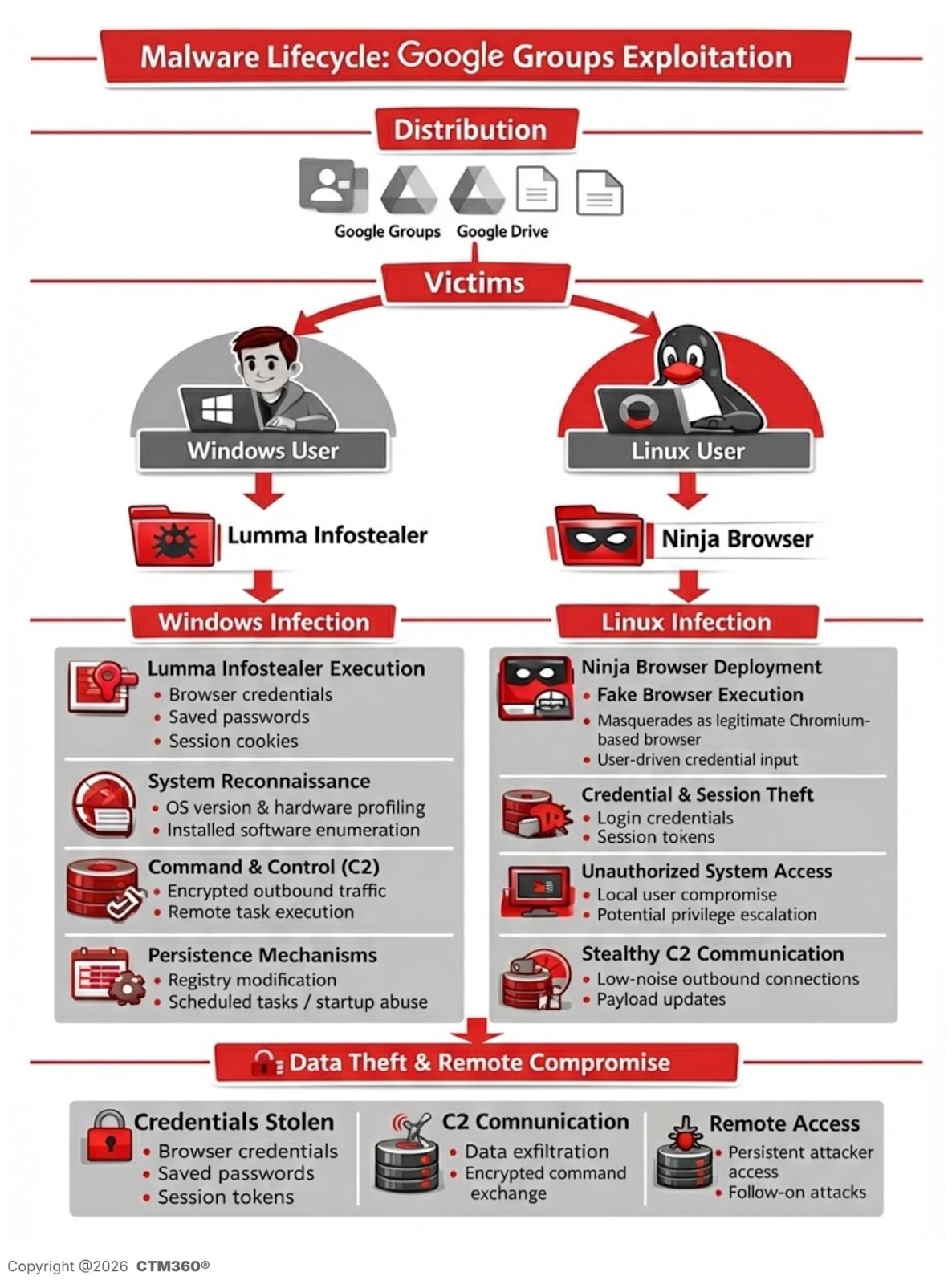
Figure: Malware lifecycle for the Lummastealer/NinjaBrowser campaign
Windows Infection Flow: Lumma Info‑Stealer
For Windows users, the campaign delivers a password‑protected compressed archive hosted on a malicious file‑sharing infrastructure.
Oversized archive to evade detection
The archive decompresses to ≈ 950 MB, while the actual malicious payload is only ≈ 33 MB.
CTM360 researchers discovered that the executable is padded with null bytes—a technique used to:
- Exceed antivirus file‑size scanning thresholds.
- Disrupt static‑analysis engines.
AutoIt‑based reconstruction
When the archive is executed, the malware:
- Reassembles segmented binary files.
- Launches an AutoIt‑compiled executable.
- Decrypts and runs a memory‑resident payload.
The observed behavior matches Lumma Stealer, a commercially sold infostealer frequently used in credential‑harvesting campaigns.
Observed behavior
- Browser credential exfiltration.
- Session‑cookie harvesting.
- Shell‑based command execution.
- HTTP POST requests to C2 infrastructure (e.g.,
healgeni[.]live). - Use of multipart/form‑data POST requests to mask exfiltrated content.
CTM360 identified multiple associated IP addresses and SHA‑256 hashes linked to the Lumma‑stealer payload.
Linux Infection Flow: Trojanized “Ninja Browser”
Linux users are redirected to download a trojanized Chromium‑based browser branded “Ninja Browser.”
The software advertises itself as a privacy‑focused browser with built‑in anonymity features, but CTM360’s analysis shows that it:
- Silently installs malicious extensions without user consent.
- Implements hidden persistence mechanisms that enable future compromise by the threat actor.
Malicious extension behavior
A built‑in extension named “NinjaBrowserMonetisation” was observed to:
- Track users via unique identifiers.
- Inject scripts into web sessions.
- Load remote content.
- Manipulate browser tabs and cookies.
- Store data externally.
The extension contains heavily obfuscated JavaScript that uses XOR and a Base56‑like encoding. While not all embedded domains are currently active, the infrastructure suggests future payload‑deployment capability.
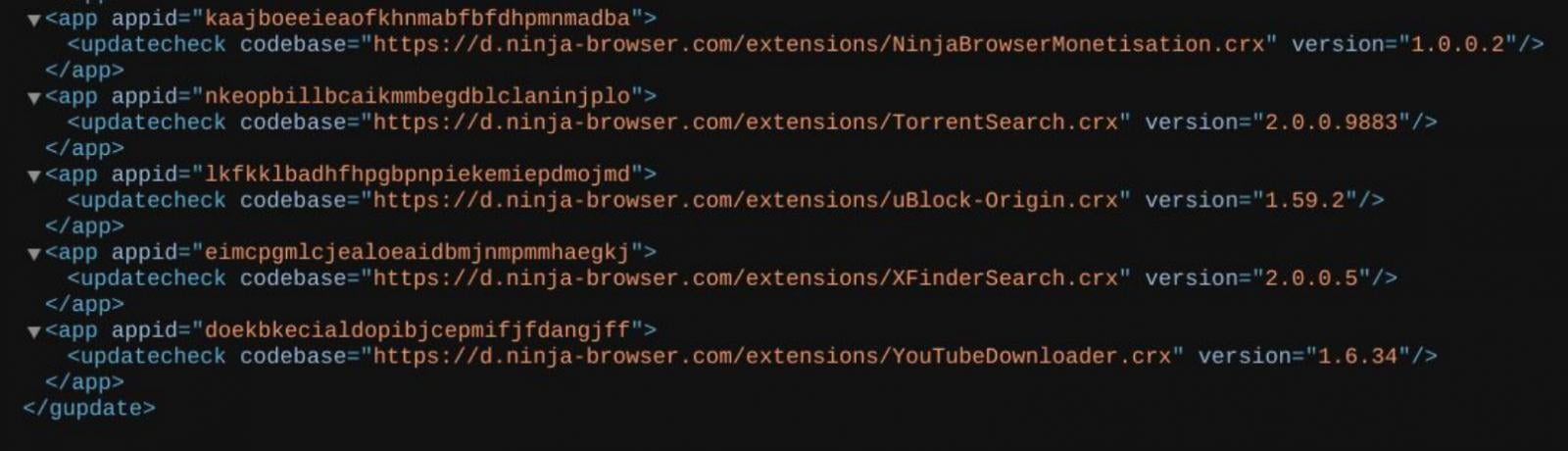
The installed extensions by the threat actor to the browser (server‑side view).
Source: CTM360
Silent persistence mechanism
CTM360 also identified scheduled tasks configured to:
- Poll attacker‑controlled servers daily.
- Silently install updates without user interaction.
- Maintain long‑term persistence.
Researchers also noted that the browser defaults to a Russian‑based search engine named “X‑Finder” and redirects to another suspicious AI‑themed search page.
Associated infrastructure
The campaign appears tied to the following domains:
ninja-browser[.]comnb-download[.]comnbdownload[.]space
Campaign Infrastructure & Indicators of Compromise
CTM360 linked the activity to the following infrastructure:
IP Addresses
152.42.139[.]1889.111.170[.]100
C2 Domain
healgeni[.]live
Note: Multiple SHA‑256 hashes and additional domains associated with credential‑harvesting and info‑stealer distribution are detailed in the full report.
Risks to organizations
Lumma Stealer risks
- Credential and session token theft
- Account takeover
- Financial fraud
- Lateral movement in enterprise environments
Ninja Browser risks
- Silent credential harvesting
- Remote command execution
- Backdoor‑like persistence
- Automatic malicious updates without user consent
Note: Because the campaign abuses Google‑hosted services, the attack bypasses traditional trust‑based filtering mechanisms and increases user confidence in malicious content.
Defensive recommendations
- Inspect shortened URLs and Google Docs/Drive redirect chains.
- Block the IoCs at firewall and EDR levels.
- Educate users against downloading software from public forums/sources without verification.
- Monitor scheduled task creation on endpoints.
- Audit browser extension installations.
The campaign highlights a broader trend: attackers are increasingly weaponizing trusted SaaS platforms as delivery infrastructure to evade detection.
About the Research
The findings were published in CTM360’s February 2026 threat‑intelligence report, “Ninja Browser & Lumma Infostealer Delivered via Weaponized Google Services.”
CTM360 continues to monitor this activity and track related infrastructure.
Read the full report:
CTM360 – Ninja Browser & Lumma Infostealer Report
Detect Cyber Threats 24/7 with CTM360
Monitor, analyze, and promptly mitigate risks across your external digital landscape with CTM360.
Sponsored and written by CTM360.