DKnife Linux toolkit hijacks router traffic to spy, deliver malware
Source: Bleeping Computer
Overview
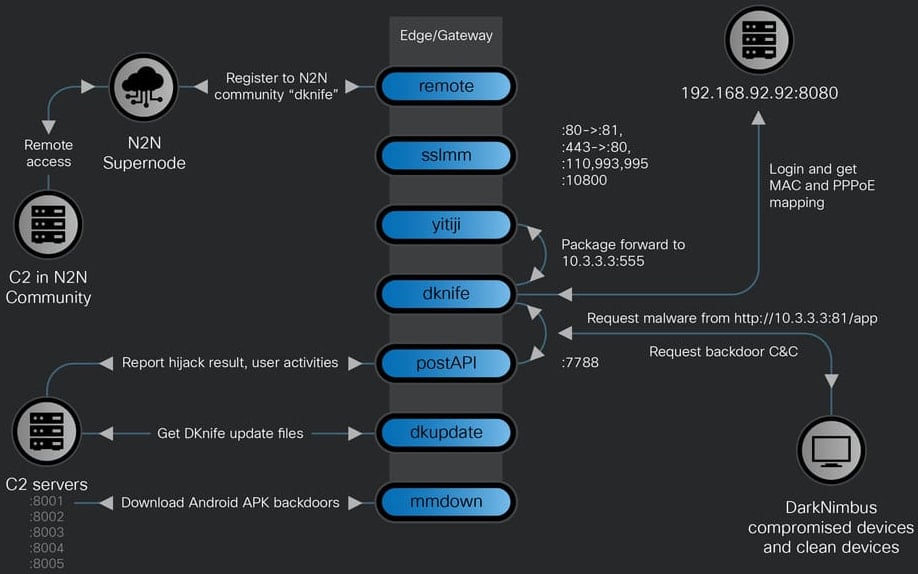
- Purpose – Post‑compromise framework for traffic monitoring and adversary‑in‑the‑middle (AitM) activities.
- Target – Intercepts and manipulates traffic destined for computers, mobile devices, and IoT endpoints on a network.
- Architecture – An ELF framework consisting of seven Linux‑based components that perform deep‑packet inspection (DPI), traffic manipulation, credential harvesting, and malware delivery.
Researchers at Cisco Talos assess with high confidence that the operator of DKnife is a China‑nexus threat actor.
The malware contains Simplified Chinese language artifacts in component names and code comments and explicitly targets Chinese services (email providers, mobile apps, media domains, and WeChat users).
Components
| Component | Description |
|---|---|
| dknife.bin | Core packet‑inspection engine; logs attacks, reports user activity, and forwards collected data. |
| postapi.bin | Relay between dknife.bin and the C2 servers. |
| sslmm.bin | Custom reverse‑proxy derived from HAProxy. |
| yitiji.bin | Creates a virtual Ethernet (TAP) interface on the router and bridges it into the LAN (default IP 10.3.3.3). |
| remote.bin | Peer‑to‑peer VPN client built on the n2n VPN software. |
| mmdown.bin | Downloader/updater for Android APK files. |
| dkupdate.bin | Handles DKnife download, deployment, and updates. |
Source: Cisco Talos
Key Capabilities
- C2 Management – Serves update C2 for backdoors, delivers ShadowPad and DarkNimbus payloads.
- DNS Hijacking – Alters DNS responses to redirect victims.
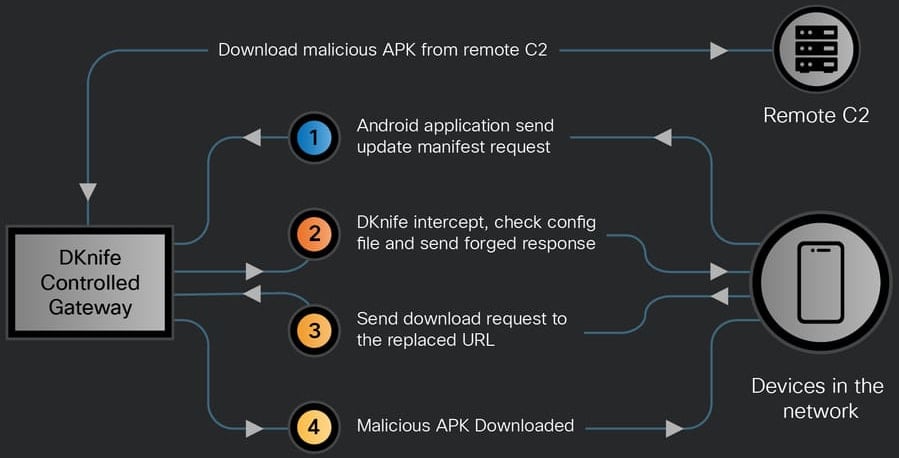
- Update Hijacking – Intercepts Android app updates and Windows binary downloads, injecting malicious payloads.
- Credential Harvesting – Decrypts POP3/IMAP traffic to steal credentials.
- Phishing Page Hosting – Serves malicious pages to lure users.
- AV Traffic Disruption – Blocks or manipulates security‑product communications.
- User‑Activity Monitoring – Tracks messaging (WeChat, Signal), maps, news, calls, ride‑hailing, and shopping activity; exfiltrates data via HTTP POST to C2 endpoints.
“Its key capabilities include serving update C2 for the backdoors, DNS hijacking, hijacking Android application updates and binary downloads, delivering ShadowPad and DarkNimbus backdoors, selectively disrupting security‑product traffic and exfiltrating user activity to remote C2 servers,” – Cisco Talos report.
Payload Delivery
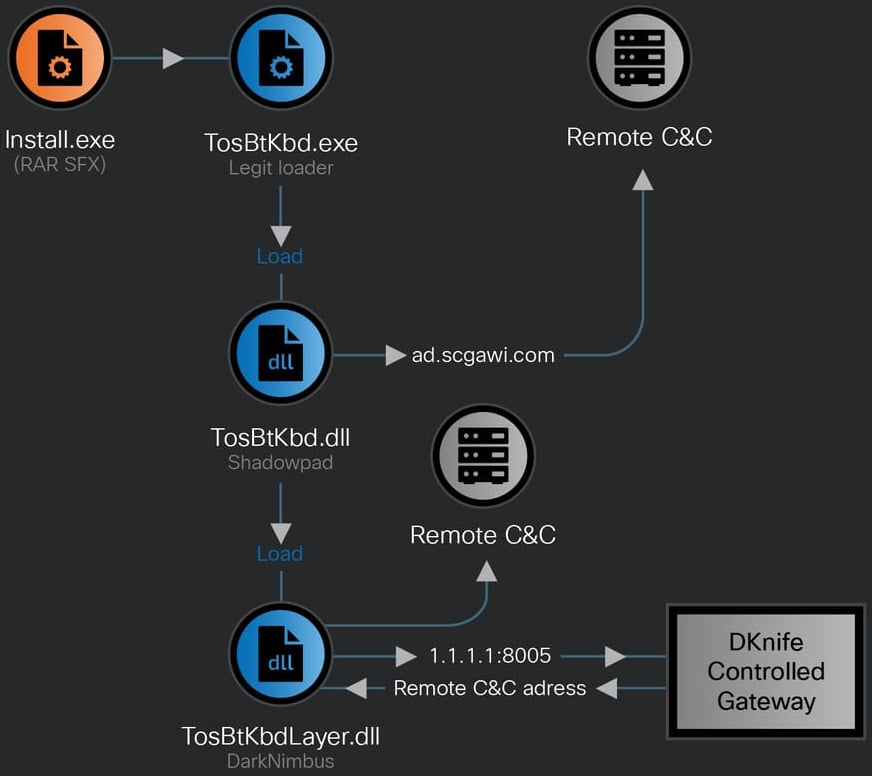
- ShadowPad – Dropped on Windows devices, signed with a Chinese firm’s certificate.
- DarkNimbus – Deployed after ShadowPad; also delivered directly to Android devices.
Source: Cisco Talos
The same infrastructure also hosts the WizardNet backdoor (previously linked to the Spellbinder AitM framework by ESET).
Android Update Hijacking
Source: Cisco Talos
Indicators of Compromise (IoCs)
Cisco Talos published a full set of IoCs on 7 February 2026.
- IOC list: (link to Talos IoC list)
As of January 2026, the DKnife C2 servers remain active.
References
- Talos Report: “Knife Cutting the Edge” –
- DarkNimbus Backdoor: –
- WizardNet Backdoor: –
- Wiz Promotion (advertisement): –