State actor targets 155 countries in 'Shadow Campaigns' espionage op
Source: Bleeping Computer

Overview
A state‑sponsored threat group has compromised dozens of networks of government and critical‑infrastructure entities in 37 countries in global‑scale operations dubbed “Shadow Campaigns.” Between November and December last year, the actor also engaged in reconnaissance activity targeting government entities connected to 155 countries.
According to Palo Alto Networks’ Unit 42 division, the group has been active since at least January 2024, and there is high confidence that it operates from Asia. Until definitive attribution is possible, researchers track the actor as TGR‑STA‑1030 / UNC6619.
Targeted Sectors
“Shadow Campaigns” activity focuses primarily on:
- Government ministries
- Law enforcement
- Border control
- Finance
- Trade
- Energy
- Mining
- Immigration
- Diplomatic agencies
Unit 42 researchers confirmed that the attacks successfully compromised at least 70 government and critical‑infrastructure organizations across 37 countries. This includes entities involved in trade policy, geopolitical issues, and elections in the Americas; ministries and parliaments across multiple European states; the Treasury Department in Australia; and government and critical‑infrastructure in Taiwan.

Targeted countries (top) and confirmed compromises (bottom) – Source: Unit 42
The list of countries with targeted or compromised organizations is extensive and appears to be driven by specific regional events.
- During the U.S. government shutdown in October 2025, the threat actor showed increased interest in scanning entities across North, Central, and South America (Brazil, Canada, Dominican Republic, Guatemala, Honduras, Jamaica, Mexico, Panama, and Trinidad and Tobago).
- Significant reconnaissance activity was discovered against at least 200 IP addresses hosting Government of Honduras infrastructure 30 days before the national election, as both candidates indicated willingness to restore diplomatic ties with Taiwan.
Compromised Entities (as assessed by Unit 42)
- Brazil – Ministry of Mines and Energy
- Bolivia – Network of a mining‑related entity
- Mexico – Two ministries
- Panama – Government infrastructure
- Venezuela – An IP address geolocating to a Venezolana de Industria Tecnológica facility
- Cyprus, Czechia, Germany, Greece, Italy, Poland, Portugal, Serbia – Various government entities
- Indonesia – An airline
- Malaysia – Multiple government departments and ministries
- Mongolia – A law‑enforcement entity
- Taiwan – A major supplier in the power‑equipment industry
- Thailand – A government department (likely for economic and international‑trade information)
- Democratic Republic of the Congo, Djibouti, Ethiopia, Namibia, Niger, Nigeria, Zambia – Critical‑infrastructure entities
Unit 42 also believes that TGR‑STA‑1030/UNC6619 attempted SSH connections to infrastructure associated with:
- Australia’s Treasury Department
- Afghanistan’s Ministry of Finance
- Nepal’s Office of the Prime Minister and Council of Ministers
Additional Reconnaissance & Breach Attempts
- Scanning of infrastructure connected to the Czech government (army, police, parliament, ministries of interior, finance, foreign affairs, and the president’s website).
- Targeting of more than 600 IP addresses hosting .europa.eu domains.
- In July 2025, the group focused on Germany, initiating connections to over 490 IP addresses that hosted government systems.
Shadow Campaigns Attack Chain
Early operations relied on highly tailored phishing emails sent to government officials, often referencing internal ministry reorganization efforts. The emails embedded links to malicious archives with localized naming hosted on the Mega.nz storage service. The compressed files contained:
- A malware loader called Diaoyu
- A zero‑byte PNG file named pic1.png
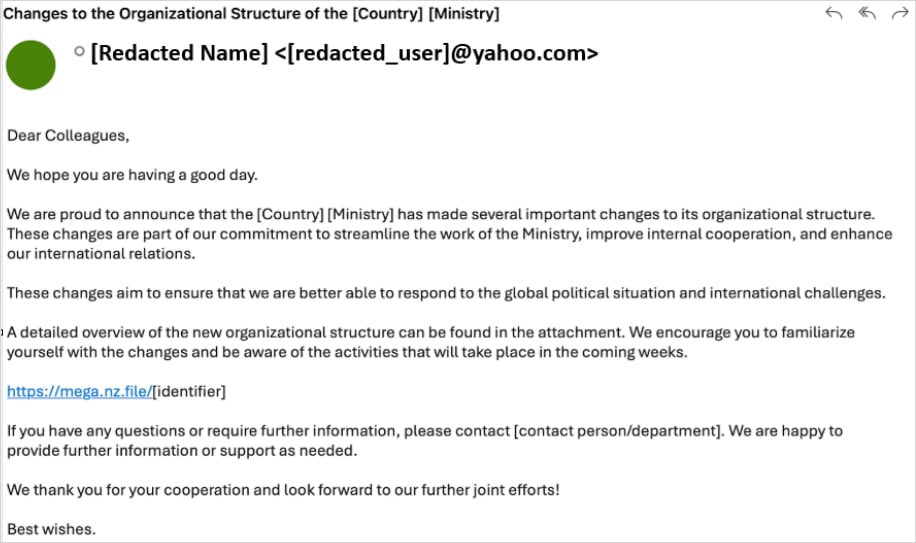
Sample of the phishing email used in Shadow Campaigns operations – Source: Unit 42
Unit 42 researchers found that the Diaoyu loader would fetch Cobalt Strike payloads and the VShell framework for command‑and‑control (C2) under certain conditions that act as analysis‑evasion checks.
“Beyond the hardware requirement of a horizontal screen resolution ≥ 1440, the sample performs an environmental dependency check for a specific file (pic1.png) in its execution directory,” the researchers say.
Read the full analysis.
The zero‑byte image acts as a file‑based integrity check; in its absence, the malware terminates before inspecting the compromised host.
To evade detection, the loader looks for running processes from the following security products:
- Kaspersky
- Avira
- Bitdefender
- Sentinel One
- Norton (Symantec)
Exploited Vulnerabilities
Apart from phishing, TGR‑STA‑1030/UNC6619 also leveraged at least 15 known vulnerabilities to achieve initial access, including issues in:
- SAP Solution Manager
- Microsoft Exchange Server
- D‑Link devices
- Microsoft Windows
New Linux Rootkit
TGR‑STA‑1030/UNC6619’s toolkit used [incomplete content – original text ends abruptly].
All information above is sourced from Palo Alto Networks’ Unit 42 research.
Shadow Campaigns activity is extensive and includes webshells such as Behinder, Godzilla, and Neo‑reGeorg, as well as network‑tunneling tools such as GO Simple Tunnel (GOST), Fast Reverse Proxy Server (FRPS), and IOX.
Custom Linux Kernel eBPF Rootkit – ShadowGuard
Researchers also discovered a custom Linux kernel eBPF rootkit called “ShadowGuard” that appears to be unique to the TGR‑STA‑1030 / UNC6619 threat actor.
“eBPF backdoors are notoriously difficult to detect because they operate entirely within the highly trusted kernel space,” the researchers explain.
Unit 42 – Shadow Campaigns: Uncovering Global Espionage
“This allows them to manipulate core system functions and audit logs before security tools or system monitoring applications can see the true data.”
Key Capabilities of ShadowGuard
- Conceals malicious process information at the kernel level.
- Hides up to 32 PIDs from standard Linux monitoring tools via syscall interception.
- Can hide files and directories named
*swsecret*. - Provides a mechanism for the operator to define processes that should remain visible.
Infrastructure
The infrastructure used in Shadow Campaigns relies on:
- Victim‑facing servers hosted with legitimate VPS providers in the U.S., Singapore, and the U.K.
- Relay servers for traffic obfuscation.
- Residential proxies or Tor for proxying.
Researchers observed the use of C2 domains that appear familiar to the target, such as:
- The
.gouvtop‑level domain for French‑speaking countries. - The
dog3rj[.]techdomain in attacks against the European space.
“It’s possible that the domain name could be a reference to ‘DOGE Jr,’ which has several meanings in a Western context, such as the U.S. Department of Government Efficiency or the name of a cryptocurrency,” the researchers explain.
Threat Actor Profile
According to Unit 42, TGR‑STA‑1030 / UNC6619 represents an operationally mature espionage actor that:
- Prioritizes strategic, economic, and political intelligence.
- Has already impacted dozens of governments worldwide.
Unit 42’s report includes Indicators of Compromise (IoCs) at the bottom to help defenders detect and block these attacks.

The Future of IT Infrastructure
The future of IT infrastructure is here
Modern IT infrastructure moves faster than manual workflows can handle. In this new Tines guide, learn how your team can:
- Reduce hidden manual delays
- Improve reliability through automated response
- Build and scale intelligent workflows on top of tools you already use
