ShinyHunters extortion gang claims Odido breach affecting millions
Source: Bleeping Computer

Odido breach claimed by ShinyHunters
The ShinyHunters extortion gang has claimed responsibility for breaching Dutch telecommunications provider Odido and stealing millions of user records from its compromised systems.
Odido is one of the largest telecommunications companies in the Netherlands, offering mobile, broadband, and television services to millions of customers nationwide.
Disclosure and timeline
- February 7: Attackers gained access to Odido’s customer contact system and began downloading personal data.
- February 12: Odido publicly disclosed the breach, stating that no Mijn Odido passwords, call details, location data, billing data, or scans of identity documents were exposed.
The company reported the incident to the Dutch Data Protection Authority, blocked the attackers’ access, and hired external cybersecurity experts for incident response and mitigation.
Exposed information
The data exposed varies per customer and may include a combination of:
- Full name
- Address and city of residence
- Mobile number
- Customer number
- Email address
- IBAN (bank account number)
- Date of birth
- Identification details (passport or driver’s license number and validity)
Scale of the breach
Local media reported that the breach affected 6.2 million customers. ShinyHunters later claimed to have stolen nearly 21 million records, adding Odido to its dark‑web leak site.
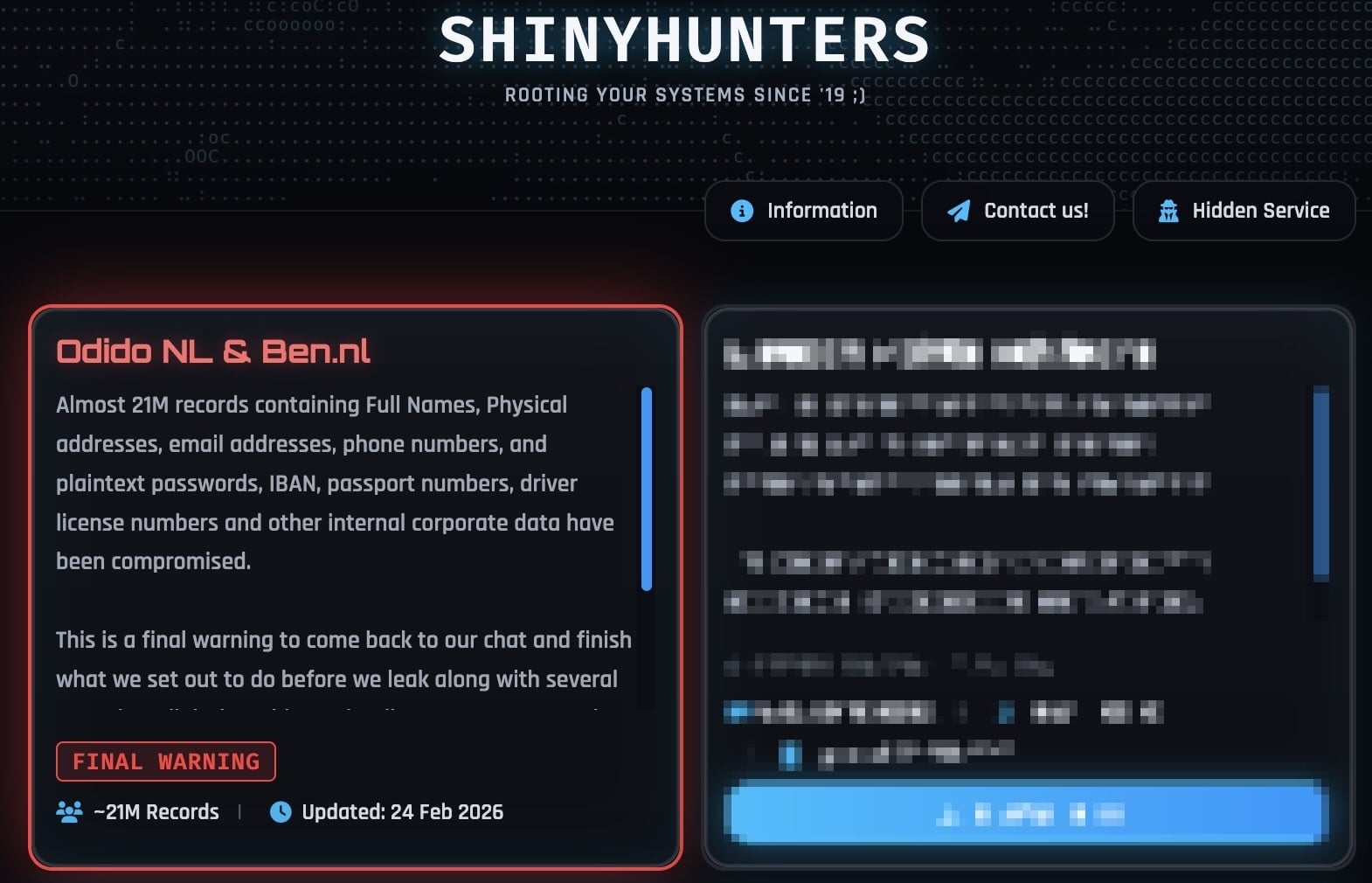
Odido on ShinyHunters leak site (BleepingComputer)
ShinyHunters’ statements and Odido’s response
ShinyHunters told BleepingComputer that the stolen data includes internal corporate data and plaintext passwords, quoting:
“This is a final warning to come back to our chat and finish what we set out to do before we leak along with several annoying (digital) problems that’ll come your way. Make the right decision, don’t be the next headline. You know where to find us.”
Odido’s spokesperson denied these claims, reiterating that no passwords, call details, social security numbers, or billing data are involved.
Recent ShinyHunters activity
In recent weeks, ShinyHunters has claimed responsibility for a series of other security breaches:
- Panera Bread
- Betterment
- SoundCloud
- Canada Goose
- PornHub
- Match Group (owner of Tinder, Hinge, Meetic, Match.com, and OkCupid)
Attack techniques
Some victims were compromised through voice‑phishing (vishing) attacks targeting single sign‑on (SSO) accounts at Google, Microsoft, and Okta. Threat actors impersonated IT support staff, prompting employees to enter credentials and multi‑factor authentication (MFA) codes on phishing sites that mimicked legitimate login portals.
BleepingComputer also reported that ShinyHunters has recently adopted device‑code vishing, abusing the OAuth 2.0 device authorization grant flow to obtain Microsoft Entra authentication tokens.
After stealing credentials and auth codes, the actors hijack the victims’ SSO accounts to breach connected enterprise services such as:
- Salesforce
- Microsoft 365
- Google Workspace
- SAP
- Slack
- Adobe
- Atlassian
- Zendesk
- Dropbox
and many others.