CarGurus data breach exposes information of 12.4 million accounts
Source: Bleeping Computer

The ShinyHunters extortion group has published personal information in more than 12 million records allegedly stolen from CarGurus, a U.S.-based digital auto platform. CarGurus is a publicly traded automotive research and shopping company that operates in the U.S., Canada, and the U.K., attracting an estimated 40 million monthly visitors.
Leak Details
On February 21, the threat group released a 6.1 GB archive containing 12.4 million records, claiming the data originated from CarGurus. The following day, the HaveIBeenPwned (HIBP) data‑breach monitoring platform added the dataset to its database.
Compromised Data Types
- Email addresses
- IP addresses
- Full names
- Phone numbers
- Physical addresses
- User account IDs
- Finance pre‑qualification application data
- Finance application outcomes
- Dealer account details
- Subscription information
Response and Impact
CarGurus has not issued an official statement about the breach and did not respond to requests for comment. HIBP notes that it attempts to verify the authenticity of leaked records before publishing them.
According to HIBP, 70 % of the leaked data was already present in its database from previous incidents, meaning roughly 3.7 million records are newly exposed. Because the information is freely downloadable, cybercriminals could exploit it for phishing and other malicious activities.
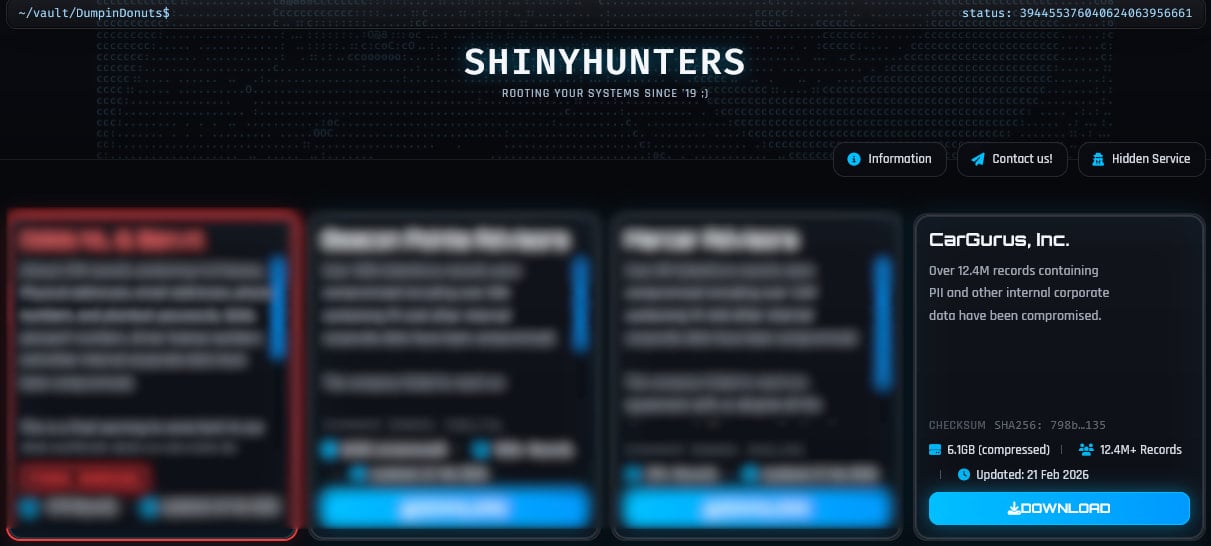 ShinyHunters lists CarGurus as their victim
ShinyHunters lists CarGurus as their victim
Source: BleepingComputer
Advice for CarGurus Users
- Remain vigilant for suspicious communications and phishing attempts that reference the leaked information.
- Avoid clicking links or downloading attachments from unknown senders.
- Consider enabling multi‑factor authentication on any CarGurus‑related accounts, if available.
ShinyHunters Activity
The ShinyHunters extortion group has been active recently, claiming multiple attacks on large organizations and leaking data when negotiations stall. Recent alleged victims include:
- Dutch telecommunications provider Odido
- Ad‑tech firm Optimizely
- Fintech firm Figure
- Outerwear brand Canada Goose
- Restaurant chain Panera Bread
- Online dating company Match Group
- Music streaming platform SoundCloud
Typical Tactics of ShinyHunters
- Social engineering: Primarily voice phishing (vishing) to trick employees into revealing credentials.
- Credential‑harvesting pages: Victims are directed to malicious login portals that capture credentials for SaaS platforms such as Salesforce, Okta, and Microsoft 365.
- Malicious OAuth applications: In previous campaigns, employees were persuaded to install OAuth apps that granted the attackers API‑level read access to customer data tables within Salesforce instances.