ShinyHunters claims ongoing Salesforce Aura data theft attacks
Source: Bleeping Computer

What’s happening?
- Attackers target the
/s/sfsites/auraAPI endpoint on Experience Cloud sites that expose a guest‑user profile with excessive permissions. - They use a modified version of AuraInspector, an open‑source auditing tool originally developed by Mandiant, to locate and exploit these misconfigurations.
- The issue is not a platform vulnerability; it stems from customer‑configured guest‑user settings.
“It is important to note that Salesforce remains secure, and this issue is not due to any vulnerability inherent to our platform. Our investigation to date confirms that this activity relates to a customer‑configured guest user setting, not a platform security flaw.” – Salesforce advisory
Why it matters
A publicly exposed Experience site can allow anonymous visitors to:
- Query Salesforce CRM objects directly without authentication.
- Enumerate internal users if Portal User Visibility or Site User Visibility is enabled.
- Potentially create portal accounts using exposed data, expanding the attack surface.
Immediate actions for administrators
-
Audit guest‑user permissions
- Reduce the profile to the minimum required privileges.
- Set org‑wide defaults to Private for external access.
-
Restrict visibility settings
- Turn off Portal User Visibility and Site User Visibility.
-
Disable unnecessary features
- Turn off self‑registration unless absolutely required.
-
Hardening the API
- Disable guest access to public APIs.
- Remove the API Enabled permission from the guest profile.
-
Monitor for suspicious activity
- Review Aura Event Monitoring logs for unusual queries, unfamiliar IP addresses, or access to objects that should remain private.
- Designate a Security Contact in Salesforce so the vendor can notify the appropriate person promptly.
Helpful references
- AuraInspector – open‑source auditing tool (Mandiant)
- Salesforce advisory: Protecting your data – essential actions to secure Experience Cloud guest‑user access
- Principle of Least Privilege (Salesforce blog)
ShinyHunters Takes Responsibility
In a post on their data‑leak site, the ShinyHunters threat actor claimed responsibility for the Salesforce Aura/Experience Cloud data‑theft attacks.
- Scope: ShinyHunters says they compromised ≈ 100 high‑profile companies, many in the cybersecurity sector.
- Overall impact: The total number of breached organizations is estimated at 300–400, according to the hackers’ statements to BleepingComputer.
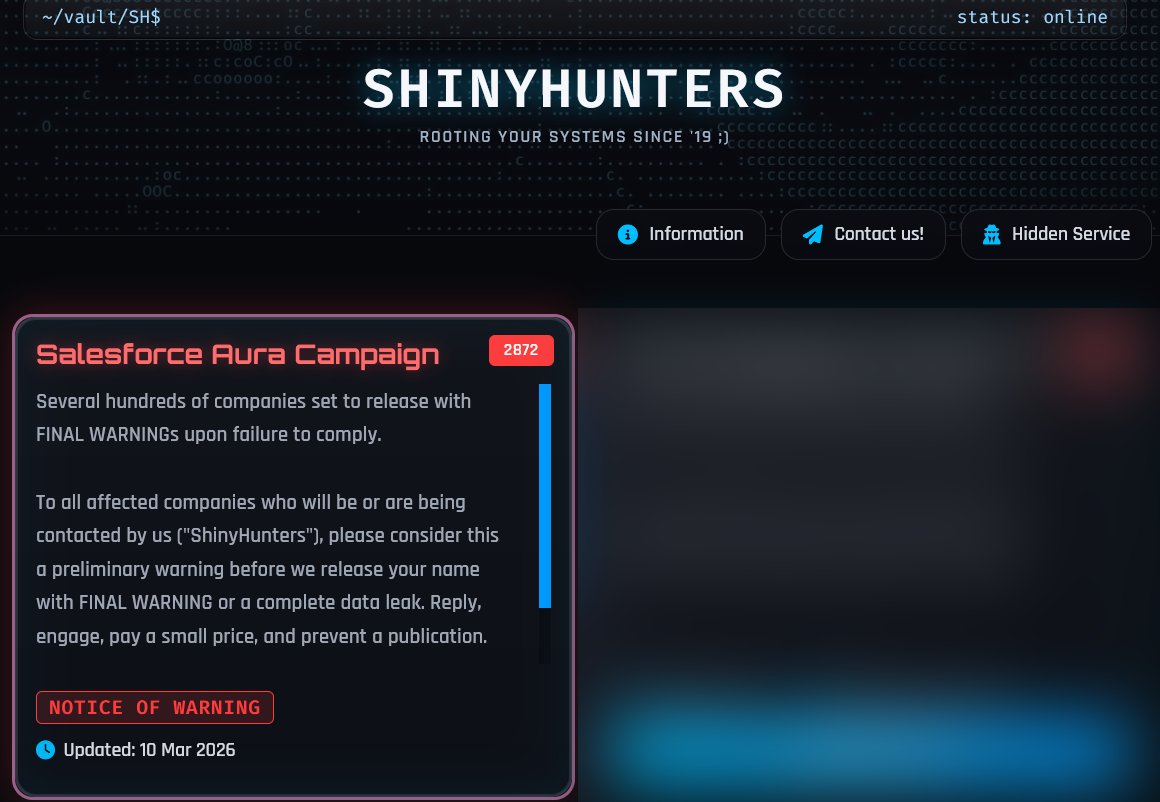
Source: BleepingComputer
Attack Timeline & Methodology
-
September 2025 – Initial compromise
- Targeted companies with insecure Experience Cloud access‑control settings for guest users.
- Identified Aura instances by scanning the internet for the
/s/sfsites/endpoint.
-
GraphQL query limitation
- Salesforce’s GraphQL API allows only 2,000 records per query, which slowed data exfiltration.
- ShinyHunters discovered that the
sortByparameter could bypass this restriction.
-
Response to AuraInspector
- After the release of AuraInspector (January 2025) – a tool to locate misconfigured instances – the group modified its code for additional reconnaissance.
- Salesforce’s advisory confirms that a variant of Mandiant’s tool was used “to perform mass scanning of public‑facing Experience Cloud sites.”
-
Custom data‑theft tool – user‑agent string
Anthropic/RapeForceV2.01.39 (AGENTIC)The name resembles the “RapeFlake” tool used in the SnowFlake data‑theft attacks.
-
Bypassing the 2,000‑record limit (post‑fix)
- After Salesforce patched the
sortBytrick, ShinyHunters claimed to have found a new method to bypass the limit and has been exploiting it “discreetly.” - The group also alleges a new vulnerability that allows data theft from Aura instances even when they are properly configured.
BleepingComputer has not independently verified this claim, and Salesforce maintains that no such vulnerability exists.
- After Salesforce patched the
Mitigation Advice (as reported by the threat actor)
- Disable “Public Access” for the affected Experience Cloud site.
- This would block the described attacks but also disable guest access, turning the site into a private portal.
The threat actor also shared a more innocuous‑looking user‑agent that they claim is being used in the new attacks:
Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 Chrome/120.0.0.0 Safari/537.36Note: Disabling public access is a trade‑off; organizations must weigh the loss of guest functionality against the potential risk of data exfiltration.

Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 shows how new threats:
- Use mathematical techniques to detect sandbox environments
- Hide in plain sight to evade traditional defenses
Download the analysis of 1.1 million malicious samples to discover the top 10 techniques and assess whether your security stack can see them.