Dutch govt warns of Signal, WhatsApp account hijacking attacks
Source: Bleeping Computer
Russian‑state‑sponsored Phishing Campaign Against Signal & WhatsApp
[Image: Signal & WhatsApp phishing campaign])
Summary
- Actors: Russian state‑sponsored hackers.
- Targets: Government officials, military personnel, journalists, and Dutch civil servants.
- Platforms: Signal and WhatsApp.
- Goal: Hijack accounts to read sensitive messages and monitor communications.
Sources
- Netherlands Defence Intelligence and Security Service (MIVD)
- Netherlands General Intelligence and Security Service (AIVD)
Both agencies confirmed that Dutch government employees have been specifically targeted.
Attack Methodology
| Technique | Description |
|---|---|
| Phishing & Social Engineering | Malicious messages lure victims into revealing authentication data (SMS verification codes and/or Signal PIN). |
| Abuse of Legitimate Authentication Features | Attackers exploit the normal account‑recovery flow to take over accounts without breaking Signal’s encryption. |
| Covert Message Monitoring | Once the account is compromised, attackers can read new inbound messages in real time. |
Official Statements
Signal (BlueSky post) – “We are aware of recent reports regarding targeted phishing attacks that have resulted in account takeovers of some Signal users, including government officials and journalists.”
“We take this very seriously. To be clear: Signal’s encryption and infrastructure have not been compromised and remain robust. These attacks were executed via sophisticated phishing campaigns, designed to trick users into sharing information – SMS codes and/or Signal PIN – to gain access to users’ accounts.”
— Signal on BlueSky
Signal also reminds users that SMS verification codes and PINs must never be shared with anyone, including Signal staff or third‑party services.
Recommendations for Users
- Never share SMS verification codes or your Signal PIN with anyone, even if the request appears to come from Signal.
- Verify the sender of any request for authentication data through a separate, trusted channel.
- Enable additional security measures where available (e.g., device‑level PIN, biometric lock).
- Stay vigilant for unsolicited messages that ask for login credentials or verification codes.
- Report suspicious activity to Signal’s support team and, if you are a government employee, to your organization’s security office.
Prepared based on publicly available intelligence from the MIVD, AIVD, and statements from Signal.
Phishing Messages Impersonate Signal Support
One of the primary attack methods involves a fake “Signal Security Support Chatbot” that warns the user of suspicious activity on their account and asks them to complete a “verification procedure” by sharing a verification code sent to their phone.
“We have noticed suspicious activity on your device, which could have led to a data leak. We have also detected attempts to gain access to your private data in Signal,” reads the phishing message.
“To prevent this, you have to pass the verification procedure, entering the verification code to Signal Security Support Chatbot.”
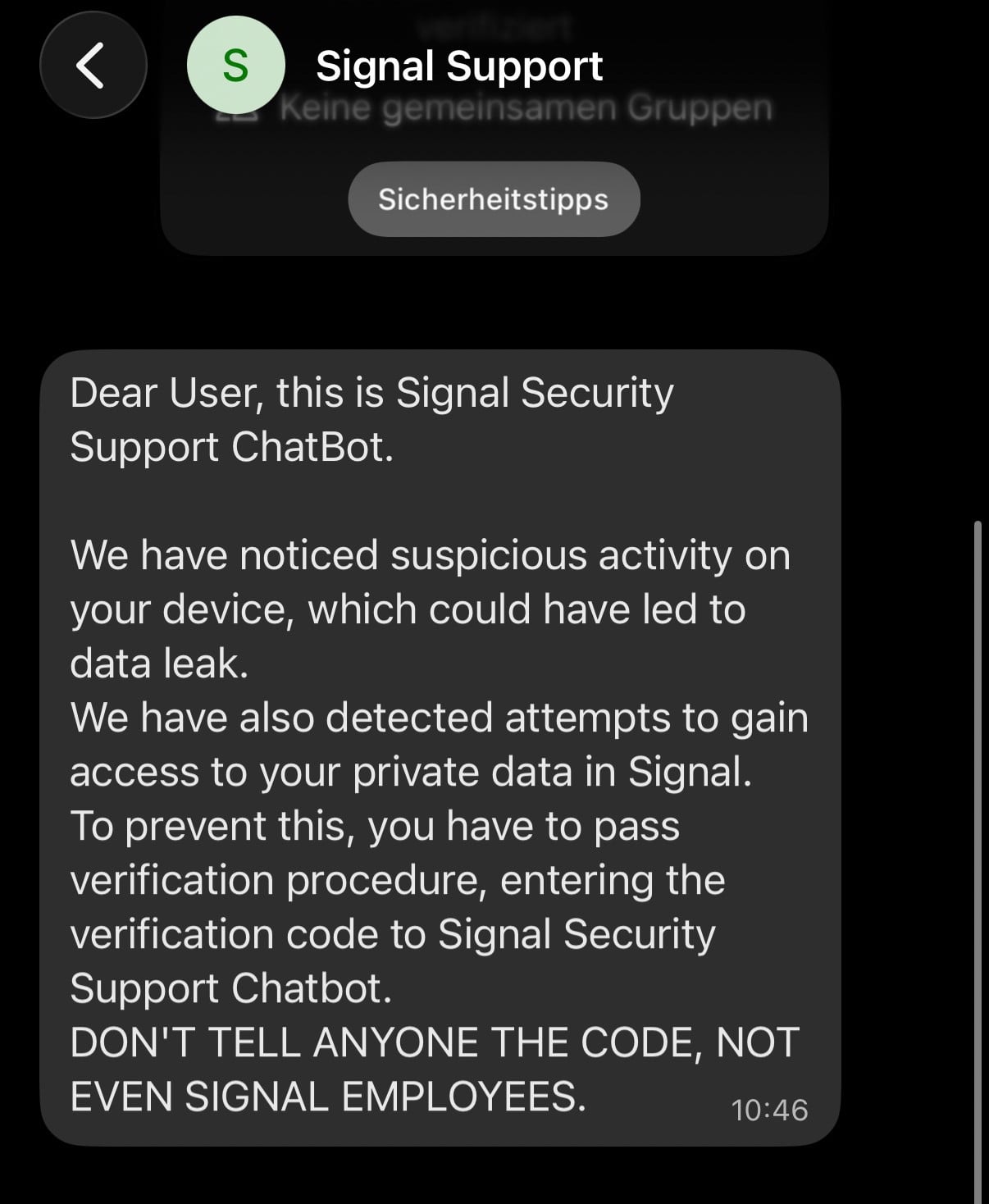
Example of a Signal phishing campaign – Source: Signal
After the victim provides the SMS verification code and their Signal PIN, attackers can take full control of the account by registering it on their own device.
What the attackers can do
- Change the phone number linked to the account to one they control, giving them access to the victim’s contact list and incoming messages (including group chats).
- Impersonate the victim by sending messages from the compromised account.
- Regain the victim’s chat history because Signal stores messages locally; when the victim re‑registers, they may think nothing is wrong.
“The victim is unable to access their account, although they can create a new Signal account using their existing telephone number, as the actor has already linked the compromised account to a new telephone number,” warns the Dutch intelligence agencies.
“Because Signal stores the chat history locally on the phone, a victim can regain access to that history after re‑registering. As a result, the victim may assume that nothing is wrong. The Dutch services want to stress that this assumption could be incorrect.”
Second observed method: abusing device‑linking functionality
Attackers send victims a malicious QR code or link that appears to be an invitation to join a chat group or connect with another user. When the victim scans the code or opens the link, the attacker’s device becomes linked to the victim’s account.
- Signal – Linked Devices
- WhatsApp – Linked Devices
Both services allow users to connect secondary devices (computers, tablets) by scanning a QR code generated on the primary mobile device. Once linked, the attacker can:
- Read chat history and monitor conversations in real time.
- Send messages as the victim.
Unlike a full account takeover, the victim usually retains access to their account, making the breach harder to detect.
Recommendations from Dutch intelligence agencies
- Do not share sensitive or classified information via messaging apps unless explicitly approved.
- Regularly review the list of linked devices in Signal and WhatsApp and remove any unknown entries.
- Treat unsolicited invitations, links, or QR codes with suspicion; verify their legitimacy through an independent, trusted channel before interacting.
These precautions mirror those used against email phishing attacks.
Historical context
- 2023: Google reported that Russian threat actors targeted Signal users by abusing device‑linking features to access victims’ communications.
- December 2023: GenDigital detected a WhatsApp device‑linking QR‑code phishing campaign targeting users in Czechia (no specific threat actor attributed).

Image credit: Red Report
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter.
The Red Report 2026 reveals how new threats use mathematical techniques to detect sandboxes and hide in plain sight.
What’s inside
- 1.1 million malicious samples analyzed
- The top 10 techniques ransomware actors are using today
- An assessment of whether your security stack can still see them
Download the full analysis to see if your defenses are being blinded.