Over 10,000 Zimbra servers vulnerable to ongoing XSS attacks
Source: Bleeping Computer

Scope of the Vulnerability
Over 10,000 Zimbra Collaboration Suite (ZCS) instances exposed online are vulnerable to a cross‑site scripting (XSS) flaw tracked as CVE‑2025‑48700. The vulnerability affects ZCS versions 8.8.15, 9.0, 10.0, and 10.1 and can allow unauthenticated attackers to execute arbitrary JavaScript within a user’s session, potentially exposing sensitive information.
Patch Release
Synacor released security patches for CVE‑2025‑48700 in June 2025. The advisory notes that exploitation requires no user interaction and can be triggered when a user views a maliciously crafted email in the Zimbra Classic UI.
- Patch details:
Government Response
- CISA added CVE‑2025‑48700 to its Known Exploited Vulnerabilities (KEV) Catalog on 20 April 2026, citing evidence of active exploitation.
- KEV entry:
- CISA ordered Federal Civilian Executive Branch (FCEB) agencies to remediate vulnerable Zimbra servers within three days (by 23 April 2026).
Current Exposure
Shadowserver reported that over 10,500 Zimbra servers remain unpatched and exposed online, with the majority located in Asia (3,794) and Europe (3,793).
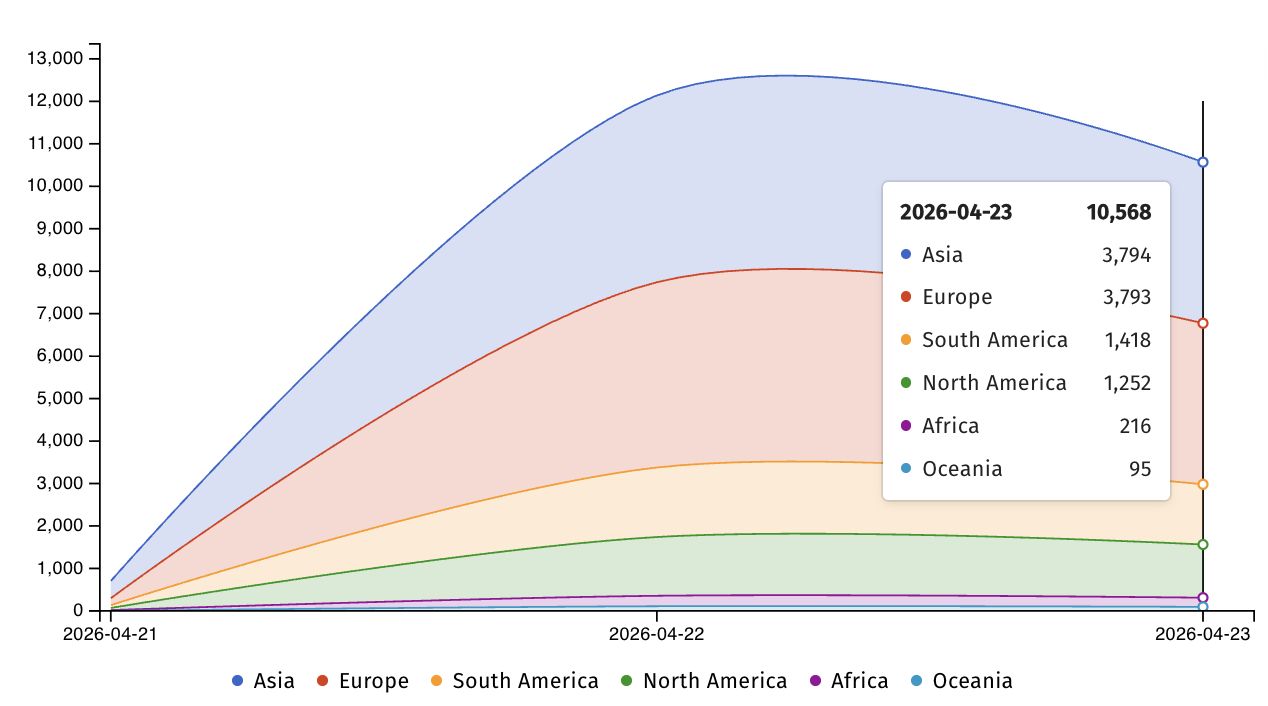
Unpatched Zimbra servers exposed online (Shadowserver)
Related Exploits and Campaigns
CVE‑2025‑66376
Another XSS flaw, CVE‑2025‑66376, was patched in early November 2025. It was exploited by the state‑backed group APT28 (Fancy Bear, Strontium) in phishing attacks targeting Ukrainian government entities starting in January 2026.
- Vulnerability details:
- Patch announcement:
- Attack coverage:
The campaign, dubbed Operation GhostMail by Seqrite Labs, delivered an obfuscated JavaScript payload via malicious emails. Recipients received no attachments, links, or macros; the entire attack chain resided within the HTML body of a single email.
“The phishing email has no malicious attachments, no suspicious links, no macros. The entire attack chain lives inside the HTML body of a single email, there are no malicious attachments.” – Seqrite Labs
Historical Context
- Winter Vivern (February 2023) leveraged a reflected XSS exploit to breach Zimbra webmail portals and steal emails from NATO‑aligned organizations.
- APT29 (Cozy Bear, Midnight Blizzard) targeted vulnerable Zimbra servers at scale in October 2024, exploiting a previously abused issue to steal email account credentials.
Summary
- CVE‑2025‑48700 remains actively exploited, with thousands of servers still exposed.
- Patches are available; organizations should apply them immediately.
- Government agencies have been directed to remediate within a short timeframe.
- The Zimbra platform continues to be a frequent target for state‑backed threat actors leveraging XSS vulnerabilities.