New GopherWhisper APT group abuses Outlook, Slack, Discord for comms
Source: Bleeping Computer

Overview
A previously undocumented state‑backed threat actor named GopherWhisper is using a Go‑based custom toolkit and legitimate services such as Microsoft 365 Outlook, Slack, and Discord in attacks against government entities. Active since at least 2023, the group has been linked to China and is estimated to have compromised dozens of victims.
Campaign Details
In a campaign identified by cybersecurity company ESET, the threat actor targeted a government entity in Mongolia and deployed a malware set with multiple backdoors that used Slack, Discord, and the Microsoft Graph API for command‑and‑control (C2) communication.
GopherWhisper also employed a custom exfiltration tool to compress stolen data and upload it to the File.io file‑sharing service.
First Detected Backdoor
In January 2025, ESET detected the first GopherWhisper backdoor written in Go, named LaxGopher. The malware can:
- Retrieve commands from a private Slack server
- Execute commands using the Command Prompt
- Download new payloads
Additional Malicious Tools
Most of the additional tools are Go‑based:
- RatGopher – Backdoor that uses a private Discord server for C2, executing commands and posting results to a configured channel.
- BoxOfFriends – Backdoor that leverages the Microsoft 365 Outlook (Microsoft Graph API) to create and modify draft emails for C2 communication.
- SSLORDoor – C++ backdoor using OpenSSL BIO over raw sockets (port 443), capable of executing commands, performing file operations (read, write, delete, upload), and drive enumeration.
- JabGopher – Injector that launches
svchost.exeand injects the LaxGopher backdoor (disguised aswhisper.dll) into its memory. - FriendDelivery – Malicious DLL acting as a loader and injector that executes the BoxOfFriends backdoor.
- CompactGopher – File‑collection tool that compresses data from the command line and exfiltrates it to File.io.
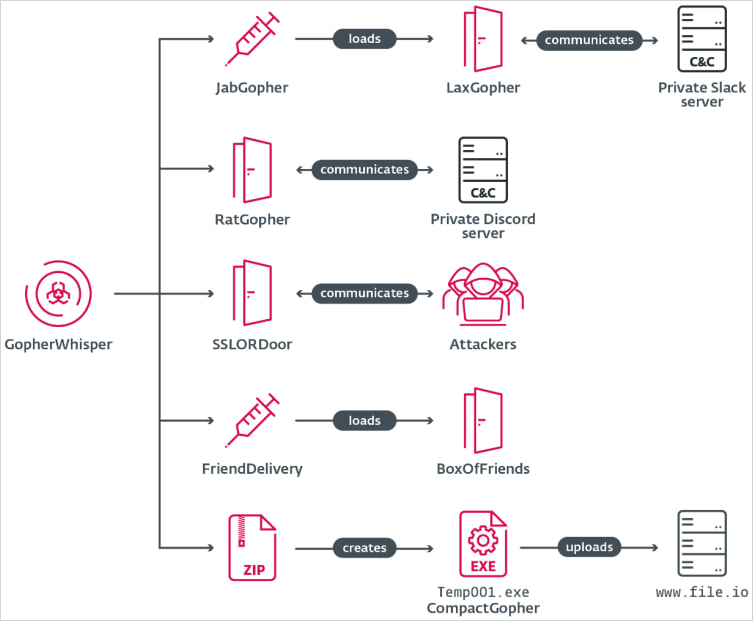
The GopherWhisper toolset
Source: ESET
C2 Communication Insights
Using credentials hardcoded in the Go‑based backdoors, researchers accessed the attackers’ accounts on Slack, Discord, and Microsoft Outlook, recovering C2 communication that included commands, uploaded files, and experimental activity.
- Slack: 6,044 messages dating back to 21 August 2024.
- Discord: 3,005 messages with the earliest from 16 November 2023.
Timestamp analysis showed commands were issued between 00:00 – 12:00 UTC on Slack and 00:00 – 14:00 UTC on Discord. Adjusting to UTC+8 (matching the “locale zh‑CN” metadata) revealed most activity occurred between 08:00 – 17:00 local time, supporting attribution to China.
ESET telemetry indicates GopherWhisper compromised 12 systems in a Mongolian government institution, while Discord and Slack C2 traffic suggests “dozens of other victims,” though their geography and sectors remain unknown.
Indicators of Compromise
ESET provides a set of GopherWhisper indicators of compromise (IoCs) to help defenders detect and block attacks from this threat cluster:
- GitHub repository:
References
- ESET technical report:
- Initial detection article: