New 'Massiv' Android banking malware poses as an IPTV app
Source: Bleeping Computer
Overview

A new Android banking malware, which researchers named Massiv, is posing as an IPTV app to steal digital identities and access online banking accounts. The malware relies on screen overlays and keylogging to obtain sensitive data and can take remote control of a compromised device.
In a campaign observed by researchers at fraud‑detection and mobile‑threat‑intelligence company ThreatFabric, Massiv targeted a Portuguese government app that connects with Chave Móvel Digital – Portugal’s digital authentication and signature system.
.jpg)
Overlays used by Massiv – Source: ThreatFabric
“MTI research identified cases where new accounts were opened in the name of the victim (user of the infected device) in new banks and services (not used by the victim),” – ThreatFabric report.
“Since those accounts are fully under fraudster control, they can further use them as a part of money‑laundering schemes as well as getting loans and cashing out the money, leaving unsuspecting victims in debt for accounts they never opened themselves.”
Remote‑control modes
Massiv provides two remote‑control modes for its operators:
- Screen live‑streaming mode – leverages Android’s MediaProjection API to stream the device’s screen.
- UI‑tree mode – extracts structured data from the Accessibility Service, including visible text, interface element names, screen coordinates, and interaction attributes. This allows attackers to click buttons, edit text fields, and more, bypassing screen‑capture protections commonly used in banking, communication, and other sensitive apps.
IPTV Lures on the Rise
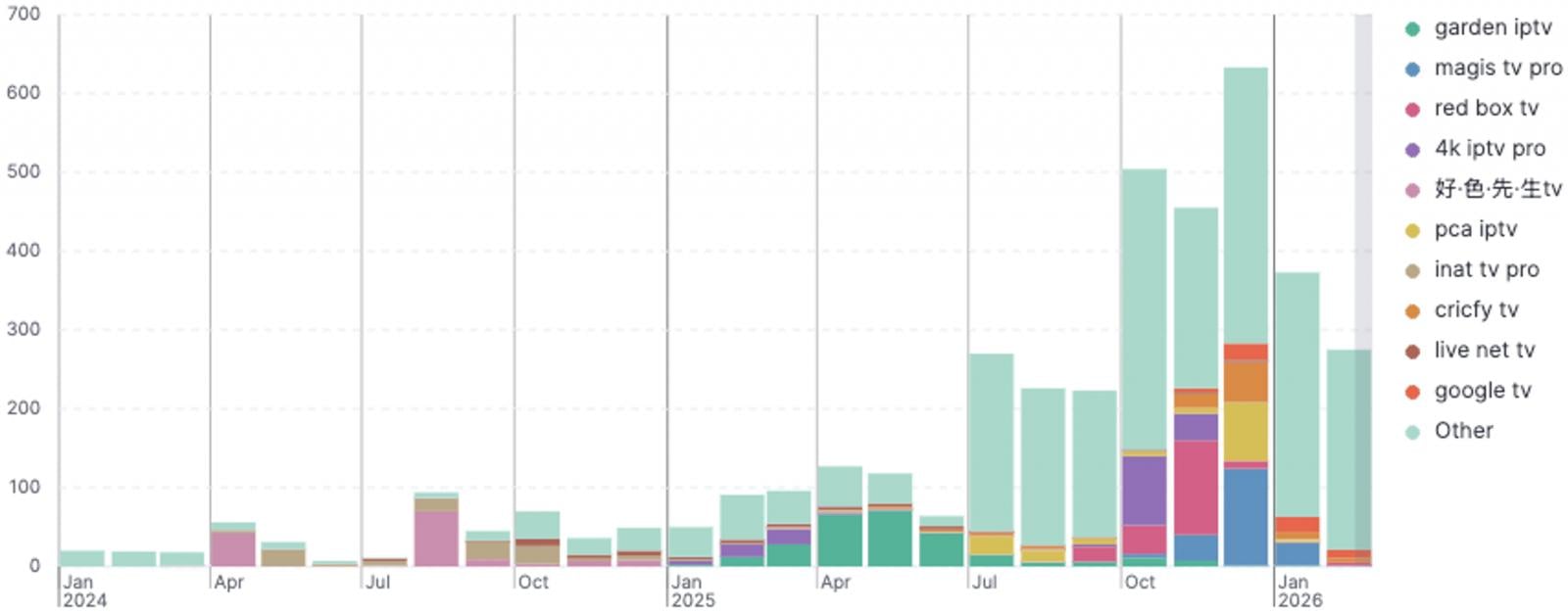
Number of IPTV‑themed malware‑loading APKs – Source: ThreatFabric
These apps typically play a key role in copyright infringement, so they cannot be found on Google Play due to policy violations. Users often source them as APKs from unofficial channels and sideload them.
In most cases, the IPTV app is fake, does not offer access to pirated broadcasts, and the APK is a dropper that installs the malware payload. In some cases, the app displays a legitimate IPTV website in a WebView to maintain the illusion.
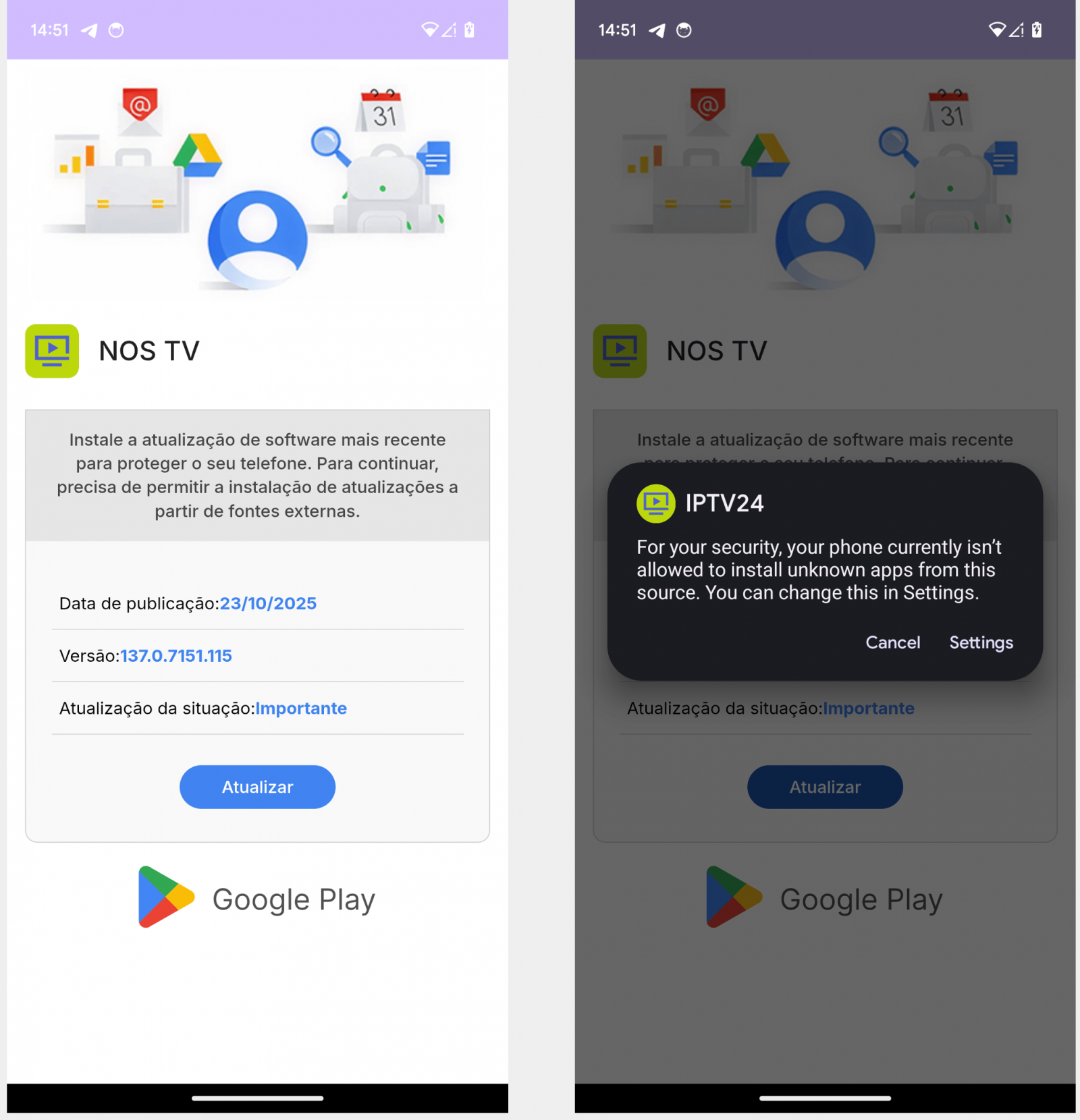
Fake IPTV app dropping Massiv – Source: ThreatFabric
The researchers report that fake IPTV‑masking malware droppers have primarily targeted users in Spain, Portugal, France, and Turkey.
Recommendation: Android users should only download vetted apps from reputable publishers available on official channels (Google Play), keep Play Protect active, and use it to regularly scan the device.