My smart sleep mask broadcasts users' brainwaves to an open MQTT broker
Source: Hacker News
Bluetooth
The first thing Claude did was scan for BLE (Bluetooth Low Energy) devices nearby. It found mine among 35 devices in range, connected, and mapped the interface – two data channels: one for sending commands, one for streaming data.
Then it tried talking to it, sending maybe a hundred different command patterns (Modbus frames, JSON, raw bytes, common headers). Unfortunately, the device said nothing back; the protocol was not a standard one.
The app
Claude turned to the Android APK, decompiled it with jadx. The app is built with Flutter, which compiles Dart source code into native ARM64 machine code, so the original source isn’t directly readable. The business logic lives in a 9 MB binary blob.
Even compiled binaries contain strings. Claude ran strings on the binary and found:
- Hard‑coded credentials for the company’s message broker (shared by every copy of the app)
- Cloud API endpoints
- All fifteen command‑builder function names (e.g., to set vibration, heating, electric stimulation, etc.)
- Protocol debug messages that revealed the packet structure – header, direction byte, command type, payload, footer
With the shape of the protocol known, Claude used blutter, a tool for decompiling Flutter’s compiled Dart snapshots. It reconstructed the functions with readable annotations, allowing Claude to determine the exact command bytes for all fifteen commands.
It works
Claude sent a six‑byte query packet. The device responded with 153 bytes containing model number, firmware version, serial number, and all eight sensor channel configurations (EEG at 250 Hz, respiration, 3‑axis accelerometer, 3‑axis gyroscope). Battery level was 83 %.
- Vibration control worked.
- Heating worked.
- EMS (electrical muscle stimulation) worked.
- Music playback worked.
Claude built a simple web dashboard with sliders for each feature, and everything functioned as expected.
The server
Remember the hard‑coded credentials? Claude used them to connect to the company’s MQTT broker. MQTT is a pub/sub messaging system standard in IoT, where devices publish sensor readings and subscribe to commands. The connection succeeded, and data started flowing—not just from my mask but from all devices using the same credentials. About 25 devices were active, including:
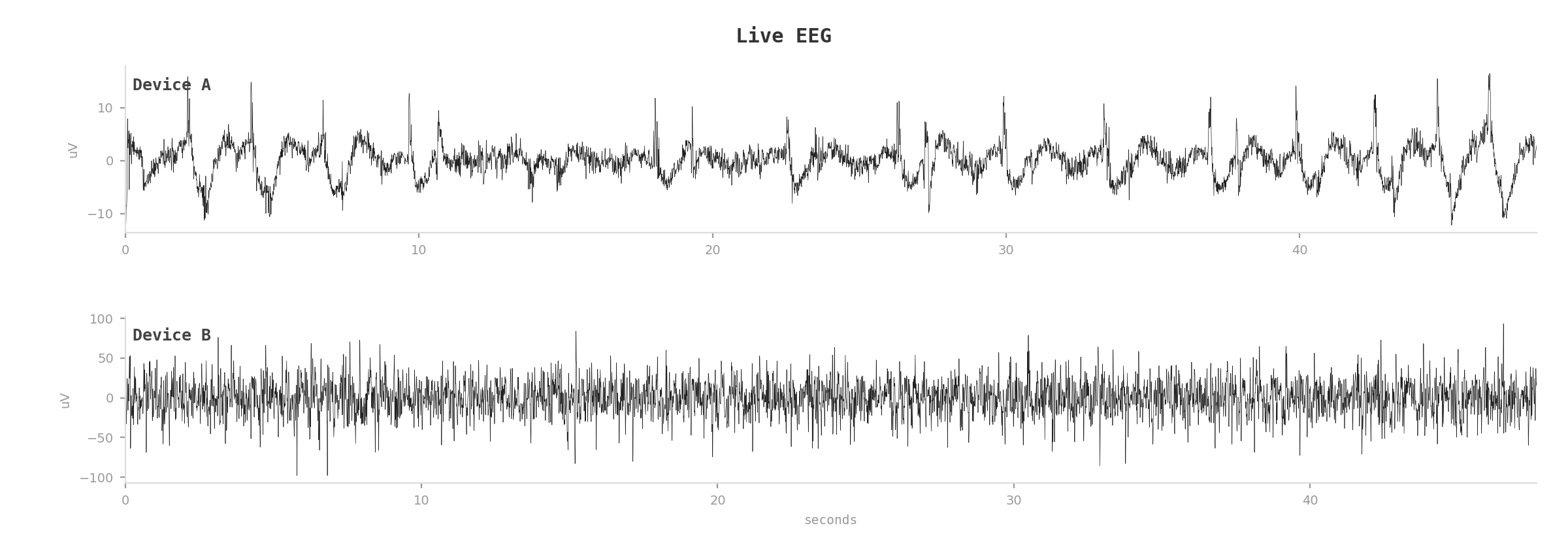
- Sleep masks publishing live EEG brainwave data
- Air‑quality monitors reporting temperature, humidity, CO₂
- Presence sensors detecting room occupancy
Claude captured a couple of minutes of EEG from two active sleep masks. One user appeared to be in REM sleep (mixed‑frequency activity); the other was in deep slow‑wave sleep (strong delta power below 4 Hz). Real brainwaves from real people, somewhere in the world.
EMS
The mask also supports EMS – electrical muscle stimulation around the eyes. Controlling it is just another command: mode, frequency, intensity, duration. Because every device shares the same credentials and broker, anyone who can read a user’s brainwaves could also send them electric impulses.
Disclosure
For obvious reasons, I am not naming the product or company, but I have reached out to inform them about the issue.
This whole episode reminded me of Karpathy’s Digital Hygiene post, which you might want to read.
The reverse engineering – Bluetooth scanning, APK decompilation, Dart binary analysis, MQTT discovery – was largely completed by Claude (Opus 4.6) in a 30‑minute autonomous session.