Microsoft Teams phishing targets employees with backdoors
Source: Bleeping Computer

Campaign Overview
Hackers targeted employees at financial and healthcare organizations via Microsoft Teams, tricking them into granting remote access through Quick Assist. The attackers then deployed a new malware family called A0Backdoor.
Infection Vector
- Social engineering – The threat actor flooded the victim’s inbox with spam, then contacted them on Teams, posing as IT staff and offering help with the unwanted messages.
- Quick Assist abuse – Victims were instructed to start a Quick Assist remote session, which the attacker used to deliver malicious tools.
- Malicious MSI installers – Digitally signed MSI files, hosted in a personal Microsoft cloud storage account, masqueraded as legitimate Microsoft Teams components and the CrossDeviceService (a legitimate Windows tool used by the Phone Link app).
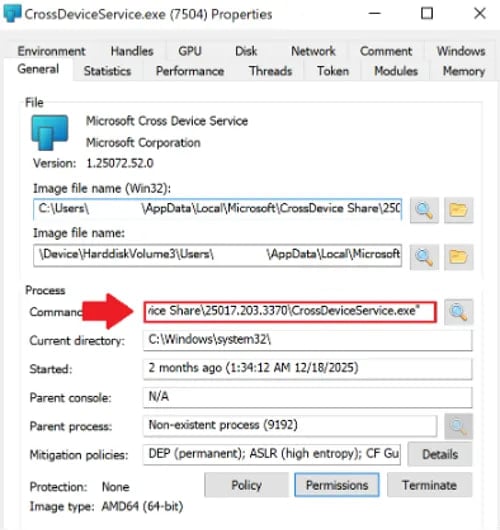 Command line argument to install the malicious CrossDeviceService.exe
Command line argument to install the malicious CrossDeviceService.exe
Source: BlueVoyant
Malware Components
DLL sideloading
The attacker used legitimate Microsoft binaries to sideload a malicious library hostfxr.dll. This library contains compressed or encrypted data that, once loaded in memory, is decrypted into shellcode and executed.
Anti‑analysis techniques
- The malicious library creates additional threads via the
CreateThreadfunction to hinder debugging. - Excessive thread creation may cause a debugger to crash, though it has little impact on normal execution.
Encrypted payload
The shellcode performs sandbox detection, generates a SHA‑256‑derived key, and decrypts the A0Backdoor payload, which is encrypted with AES.
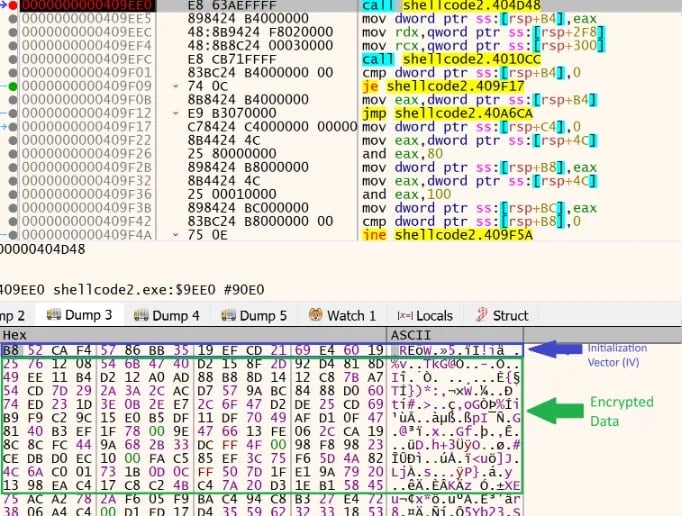 Encrypted payload in the shellcode
Encrypted payload in the shellcode
Source: BlueVoyant
Post‑decryption behavior
- Relocates itself to a new memory region and decrypts core routines.
- Calls Windows APIs such as
DeviceIoControl,GetUserNameExW, andGetComputerNameWto gather host information and create a fingerprint.
Command and Control
Communication is hidden within DNS traffic. The malware sends DNS MX queries containing high‑entropy subdomains that encode metadata to public recursive resolvers. The resolvers reply with MX records that embed encoded command data.
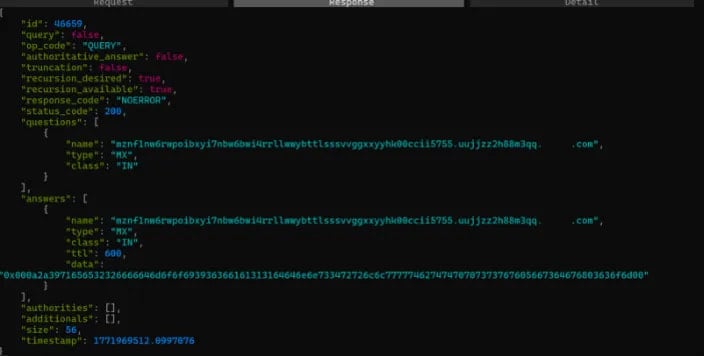 Captured DNS communication
Captured DNS communication
Source: BlueVoyant
“The malware extracts and decodes the leftmost label to recover command/configuration data, then proceeds accordingly,” explains BlueVoyant.
“Using DNS MX records helps the traffic blend in and can evade controls tuned to detect TXT‑based DNS tunneling, which may be more commonly monitored.”
Attribution
BlueVoyant identified two confirmed victims:
- A financial institution in Canada.
- A global healthcare organization.
The researchers assess with moderate‑to‑high confidence that the campaign evolves from tactics, techniques, and procedures associated with the BlackBasta ransomware gang, which has dissolved after internal chat logs were leaked. While many overlaps exist, the use of signed MSIs, malicious DLLs, the A0Backdoor payload, and DNS MX‑based C2 are new elements.