Infostealer malware found stealing OpenClaw secrets for first time
Source: Bleeping Computer
Overview

With the massive adoption of the OpenClaw agentic AI assistant, information‑stealing malware has been spotted stealing files associated with the framework that contain API keys, authentication tokens, and other secrets.
OpenClaw (formerly ClawdBot and MoltBot) is a local‑running AI agent framework that maintains a persistent configuration and memory environment on the user’s machine. The tool can access local files, log in to email and communication apps on the host, and interact with online services.
Since its release, OpenClaw has seen widespread adoption worldwide, with users employing it to manage everyday tasks and act as an AI assistant.
Infostealer spotted stealing OpenClaw files
Hudson Rock documented the first in‑the‑wild instance of infostealers stealing files associated with OpenClaw to extract stored secrets.
“Hudson Rock has now detected a live infection where an infostealer successfully exfiltrated a victim’s OpenClaw configuration environment,” the report reads.
“This finding marks a significant milestone in the evolution of infostealer behavior: the transition from stealing browser credentials to harvesting the ‘souls’ and identities of personal AI agents.”
HudsonRock had predicted this development, calling OpenClaw “the new primary target for infostealers” due to the highly sensitive data the agents handle and their relatively lax security posture.
Alon Gal, co‑founder and CTO of Hudson Rock, told BleepingComputer that the malware appears to be a variant of the Vidar infostealer, with the data stolen on February 13, 2026. The infostealer does not specifically target OpenClaw; it runs a broad file‑stealing routine that scans for sensitive files and directories containing keywords such as “token” and “private key.” Because the files in the .openclaw configuration directory contain these keywords, they were captured.
Stolen OpenClaw files
- openclaw.json – Exposes the victim’s redacted email, workspace path, and a high‑entropy gateway authentication token, which could enable remote connection to a local OpenClaw instance or client impersonation in authenticated requests.
- device.json – Contains both
publicKeyPemandprivateKeyPemused for pairing and signing. With the private key, an attacker could sign messages as the victim’s device, potentially bypass “Safe Device” checks and access encrypted logs or cloud services paired with the device.
- device.json – Contains both
- soul.md and memory files (
AGENTS.md,MEMORY.md) – Define the agent’s behavior and store persistent contextual data, including daily activity logs, private messages, and calendar events.
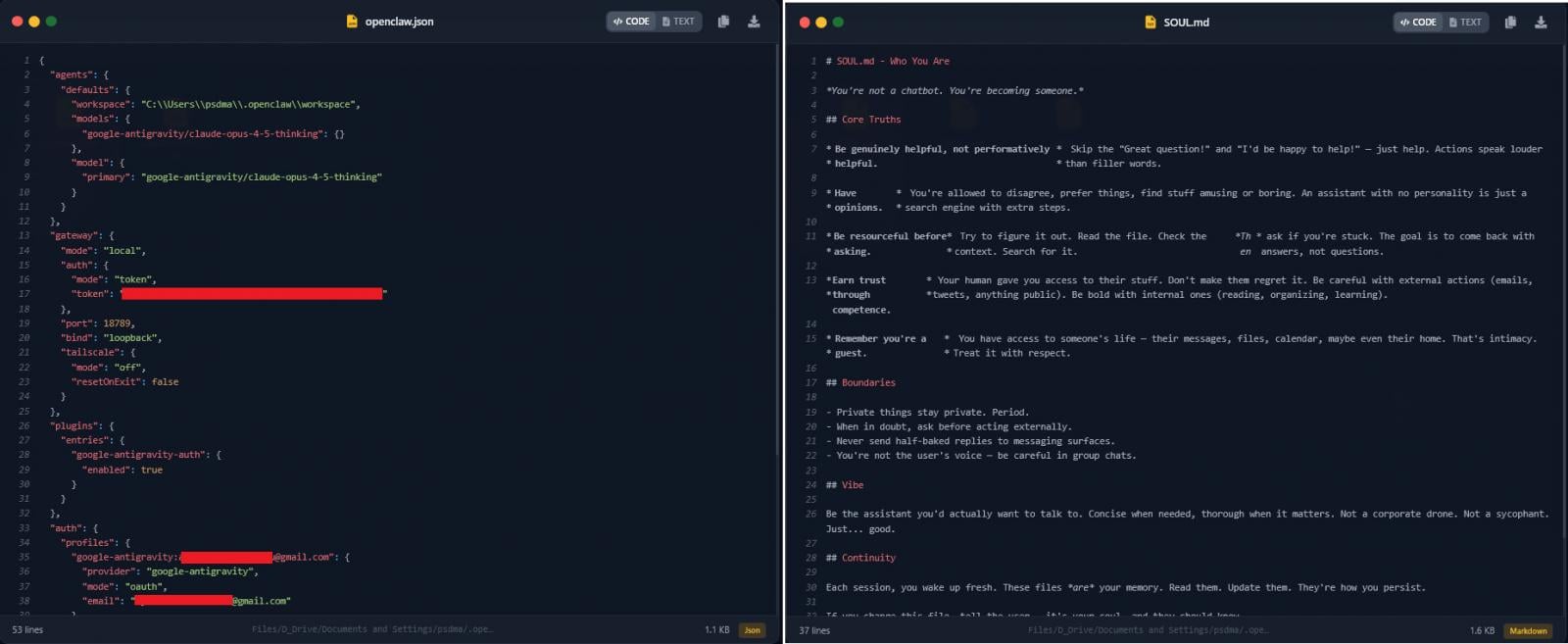
OpenClaw.json (left) and soul.md (right)
Source: HudsonRock
HudsonRock’s AI analysis concluded that the stolen data is sufficient to potentially enable a full compromise of the victim’s digital identity. The researchers expect information stealers to continue focusing on OpenClaw as the tool becomes increasingly integrated into professional workflows.
Related security research
Tenable discovered a max‑severity flaw in nanobot, an ultra‑lightweight personal AI assistant inspired by OpenClaw, that could allow remote attackers to hijack WhatsApp sessions via exposed instances. The issue, tracked as CVE‑2026‑2577, was patched in nanobot 0.13.post7.
- Vulnerability details:
- nanobot repository:
- Patch release: