How infostealers turn stolen credentials into real identities
Published: (February 19, 2026 at 10:05 AM EST)
5 min read
Source: Bleeping Computer
Source: Bleeping Computer

## The Expanding Threat of Modern Infostealers
Modern infostealers have moved far beyond stealing simple usernames and passwords. Over the past year, campaigns have accelerated, targeting **both corporate employees and individuals on personal devices** with little distinction.
### What attackers harvest
- **Credentials** (usernames, passwords, API keys)
- **Session data** (browser cookies, authentication tokens)
- **User activity** (browsing history, recent files)
- **System‑level files** stored locally on compromised machines
These data points are aggregated and sold by **initial‑access brokers**, then reused in subsequent attacks against both personal and enterprise environments.
### Scope of the research
- **90,000+ leaked infostealer dumps** examined
- **800 million rows** of data collected during active infections
- Data sources include credentials, cookies, browsing history, and local system files
> *“Infostealer dumps allow attackers to associate technical data with real users, organizations, and behavioral patterns, making a single infection valuable long after the initial compromise.”* – SpecOps researchers
### Why it matters
- Attackers can **link technical artifacts to real identities**, enabling targeted phishing, credential stuffing, and lateral movement.
- The combination of **technical data + behavioral patterns** creates a rich profile that can be weaponized across multiple campaigns.
### Further reading
- [SpecOps analysis of the most common passwords](https://specopssoft.com/our-resources/most-common-passwords/?utm_source=bleepingcomputer&utm_medium=referral&utm_campaign=bleepingcomputer_referral_na&utm_content=article)
- [Pattern‑based passwords are not secure – how to block them](https://specopssoft.com/blog/pattern-based-passwords-not-secure-can-block/?utm_source=bleepingcomputer&utm_medium=referral&utm_campaign=bleepingcomputer_referral_na&utm_content=article)
---
*Understanding the breadth and depth of infostealer data helps organizations prioritize defenses, improve credential hygiene, and implement stronger monitoring for compromised assets.*```
## When Stolen Credentials Become Identity Data
The biggest risk is how easily infostealer data ties multiple accounts and behaviors back to a single real person. These dumps routinely expose:
- Reused account names across services
- Windows usernames
- Files stored in user directories
- Active session data
- Detailed records of activity across environments
Combined, these signals let attackers move from a single **compromised credential** to identifying an individual, their employer, and potentially their role within an organization.
This convergence collapses the boundary between personal and professional identity that many security models still assume exists. What may start as a compromise on a personal device can quickly **escalate into enterprise‑level risk**.
### How Specops Helps
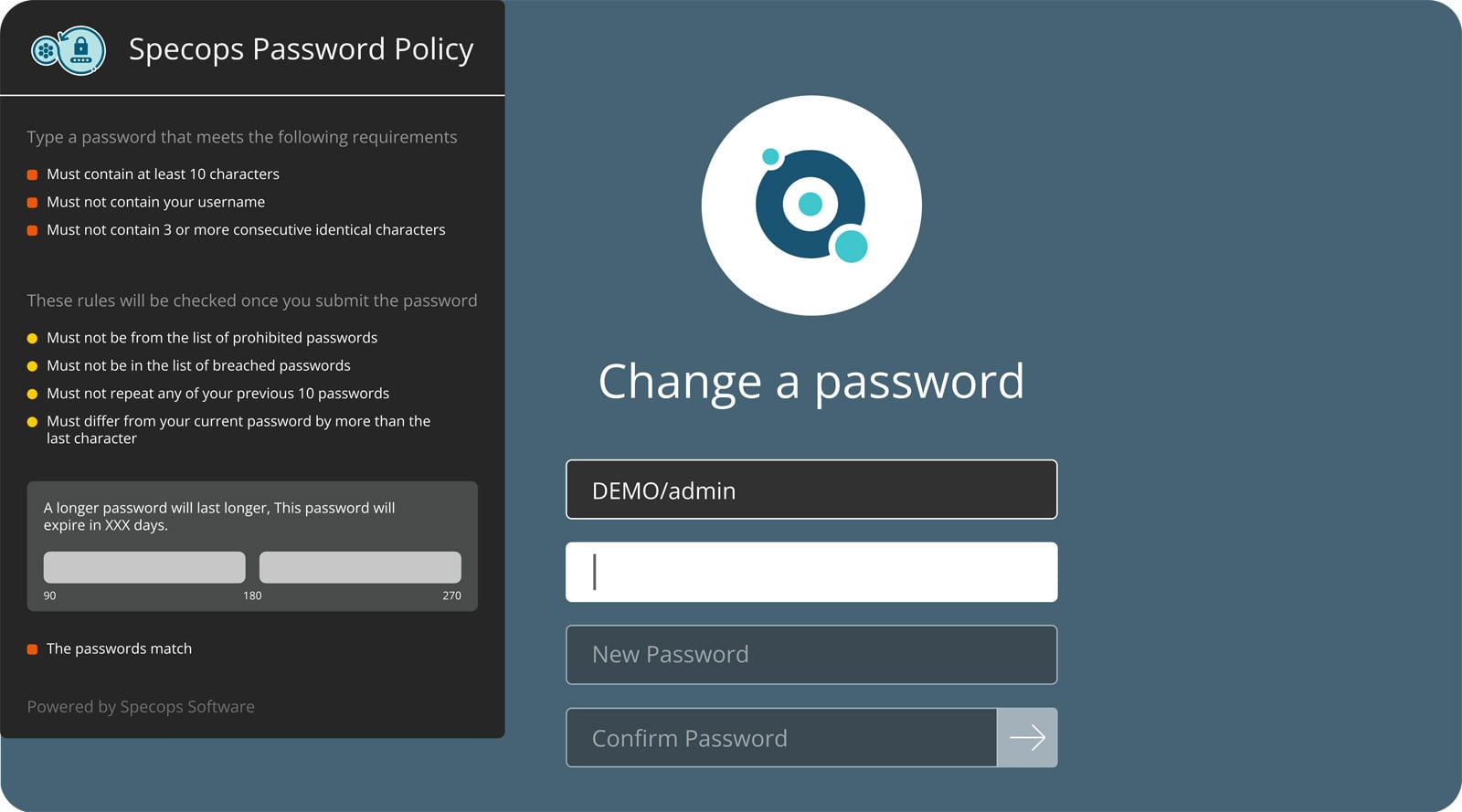
[Specops Password Policy](https://specopssoft.com/product/specops-password-policy/) continuously scans Active Directory against a database of more than **5.4 billion** known‑compromised credentials, rather than only checking passwords at creation or reset.
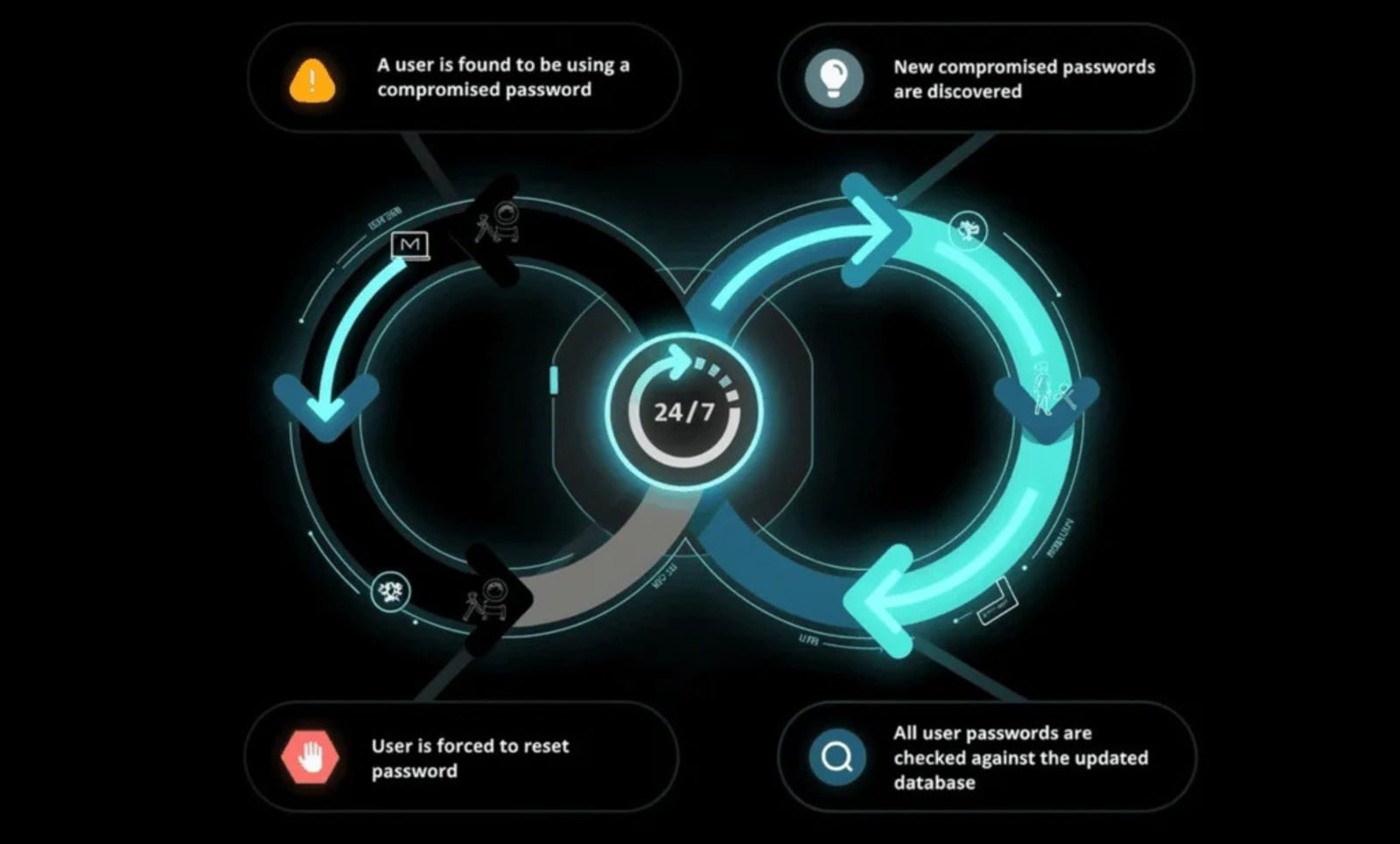
*Continuous scanning with Specops Password Policy*
Credentials that have already been exposed are blocked from being set or reused, even if they technically comply with policy, reducing the risk of compromised passwords being reused across personal and corporate accounts.
## Where Infostealers Get Your Data and How They Abuse It
The dataset contained credentials and session data for a wide **range of services** — illustrating how infostealer data exposes both identity and access.
### Professional and Enterprise‑Linked Services
- **LinkedIn, GitHub, Microsoft Teams, Outlook, and corporate domains** appeared frequently.
- LinkedIn alone accounted for nearly **900 000 records**, providing a direct path from stolen data to real names, job titles, and organizational affiliations.
- For threat actors, this information enables:
- Targeted phishing
- Social engineering ([see example](https://specopssoft.com/blog/whitepaper-secure-service-desk-social-engineering/?utm_source=bleepingcomputer&utm_medium=referral&utm_campaign=bleepingcomputer_referral_na&utm_content=article))
- Prioritization of access that may lead deeper into enterprise environments, especially where password reuse exists.
### Personal Identity and Social Platforms
- **YouTube, Facebook, and other social media platforms** made high‑volume appearances.
- These services often contain real names, photos, and social connections, making it easier to validate a compromised user’s identity and link them to other accounts.
- This correlation greatly simplifies targeted exploitation.
### Sensitive and High‑Risk Services
- Credentials and cookies for **government and tax‑related domains** (e.g., IRS, Canada Revenue Agency) and adult‑content platforms were also present.
- Access to these services introduces risks beyond traditional account takeover.
- Threat actors have historically used data from adult platforms for **extortion and blackmail**; when tied to a real identity and employer, the impact escalates quickly.
### Security‑Aware Yet Still Exposed
- Domains such as **Shodan** and even **mil.gov** appeared in the dataset, reinforcing an uncomfortable reality: technical awareness does **not** equal immunity.
- Secure practices followed in corporate environments ([Active Directory best practices](https://specopssoft.com/blog/active-directory-security-best-practices/?utm_source=bleepingcomputer&utm_medium=referral&utm_campaign=bleepingcomputer_referral_na&utm_content=article)) often do not extend to personal systems, yet exposure on those systems can still create enterprise risk.
## Why Infostealers Remain So Effective
Infostealer exposure isn’t driven by a single failure, but by a combination of **common behaviors repeated at scale**.
- Users install applications from illicit sources.
- Passwords are reused across personal and corporate accounts.
- Browser‑based credential storage is relied on for convenience.
> [Browser‑stored credentials and payment data are especially valuable to attackers.](https://specopssoft.com/blog/end-user-password-behavior-the-bane-of-it/?utm_source=bleepingcomputer&utm_medium=referral&utm_campaign=bleepingcomputer_referral_na&utm_content=article)
When an infostealer compromises a system, these stores give attackers immediate access to high‑value information, dramatically increasing the impact of a single infection.
## Reducing Impact After Credential Theft
Once infostealer data has been collected and circulated, prevention is no longer the only challenge. The real question is how quickly defenders can neutralize the threat before it’s reused for lateral movement, [account takeover](https://specopssoft.com/blog/corporate-account-takeover-attacks-and-prevention/), or ransomware deployment.
Because infostealer dumps often circulate for weeks or months before detection, effective mitigation must assume that some credentials are already exposed.
- **Password reuse** remains one of the most reliable ways attackers operationalize infostealer data. Credentials harvested from personal devices are routinely tested against corporate environments, cloud services, and remote‑access systems, often succeeding even when those passwords meet standard complexity requirements.
- **Disrupting reuse** directly reduces the operational value of infostealer datasets and shortens their window of exploitation.
Combined with stronger password policies that **support longer passphrases** and continuous enforcement, these controls shift password security from a static configuration exercise to an active containment measure.
Identity exposure increasingly begins outside the corporate perimeter, so reducing the reuse and downstream impact of stolen credentials remains one of the most effective ways to break infostealer‑driven attack chains.
**Specops Password Policy**
**To see how Specops Password Policy helps block compromised passwords and reduce credential reuse in Active Directory, [request a live demo from a Specops expert](https://specopssoft.com/contact-us/).**
*Sponsored and written by [Specops Software](https://specopssoft.com/contact-us/).*