Hackers abuse .arpa DNS and ipv6 to evade phishing defenses
Source: Bleeping Computer
What is “.arpa”?
- “.arpa” is a reserved top‑level domain (TLD) used exclusively for Internet infrastructure, not for public‑facing websites.
- It hosts the namespaces required for reverse DNS (rDNS) lookups, which map an IP address back to a hostname.
| Address family | Reverse‑lookup zone |
|---|---|
| IPv4 | in-addr.arpa |
| IPv6 | ip6.arpa |
During a reverse lookup, the IP address is written in reverse order, each octet (or nibble for IPv6) is separated by a dot, and the appropriate .arpa suffix is appended.
Example: IPv4 Reverse Lookup
Google’s IPv4 address 192.178.50.36 resolves to an in-addr.arpa name:
; > DiG 9.18.39-0ubuntu0.24.04.2-Ubuntu -x 192.178.50.36
;; global options: +cmd
;; Got answer:
;; ->>HEADER<-“We found over 100 instances where the threat actor used hijacked CNAMEs of well‑known government agencies, universities, telecommunication companies, media organizations, and retailers,” – Infoblox.
Visual Overview
| Description | Image |
|---|---|
Attack chain – How the .arpa TLD is abused in phishing emails | 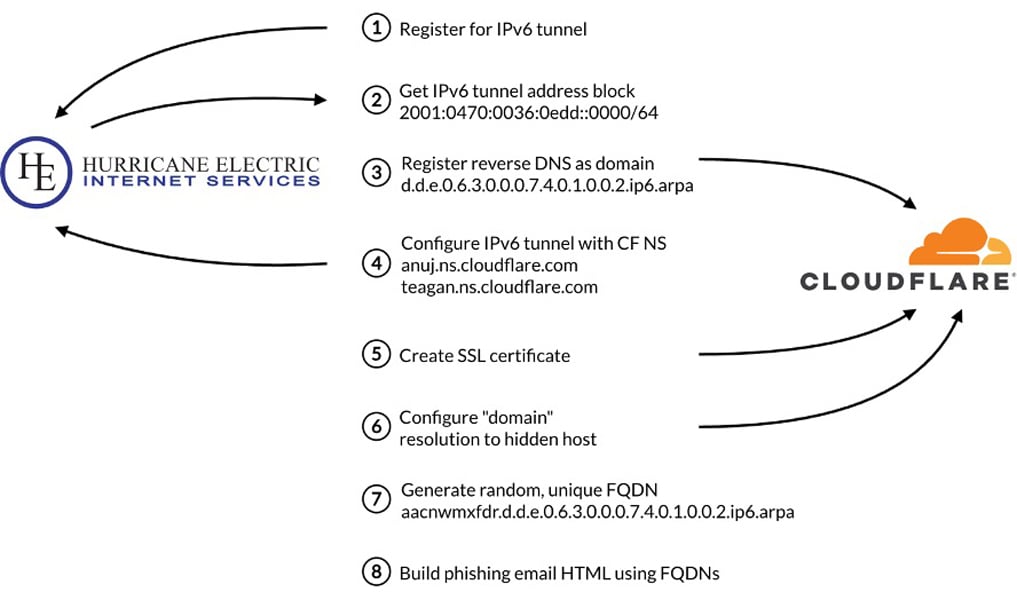 |
| Phishing email lures – Images linked to reverse IPv6 DNS records | 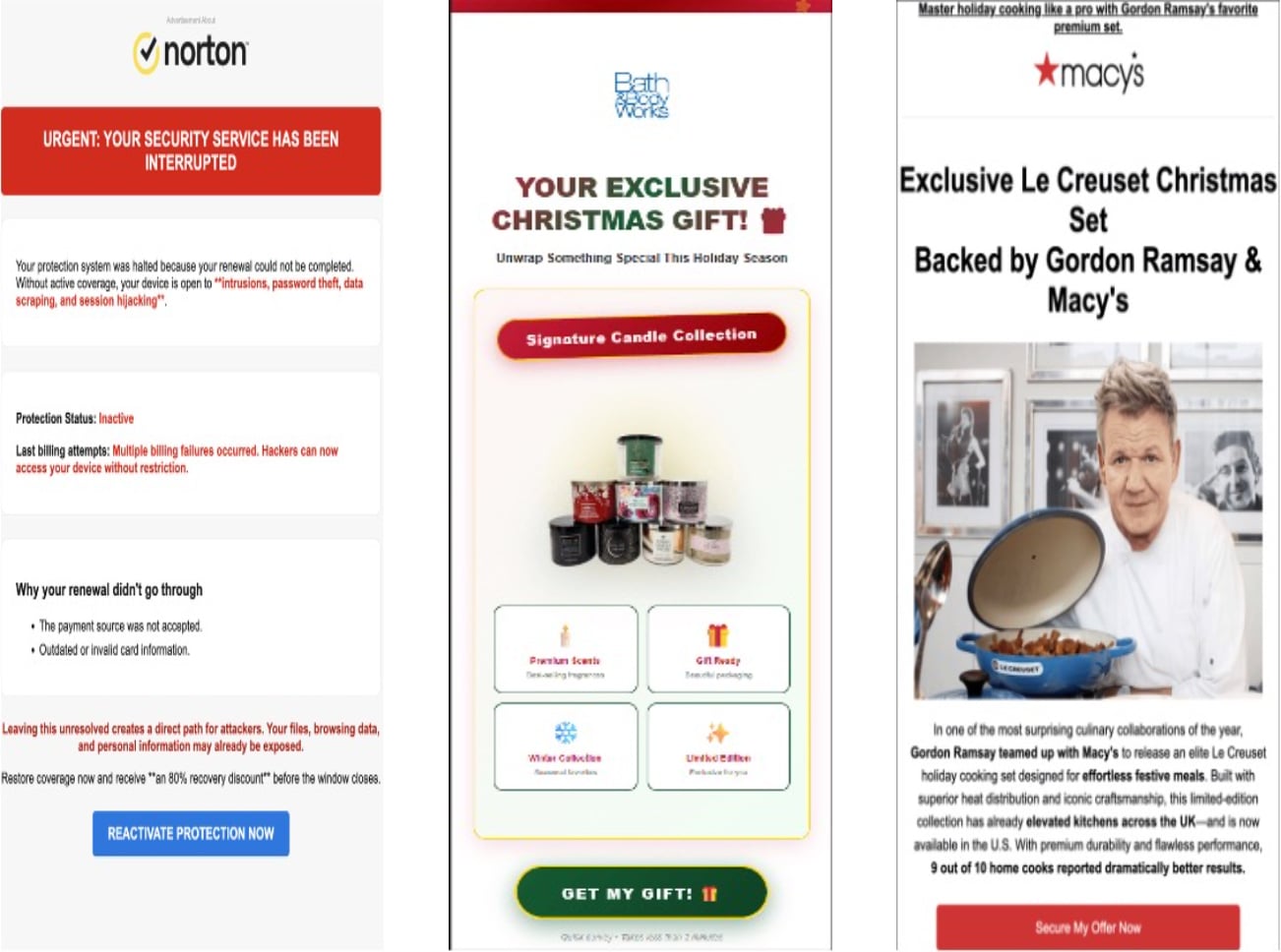 |
HTML snippet – Image and link using .arpa hostnames | 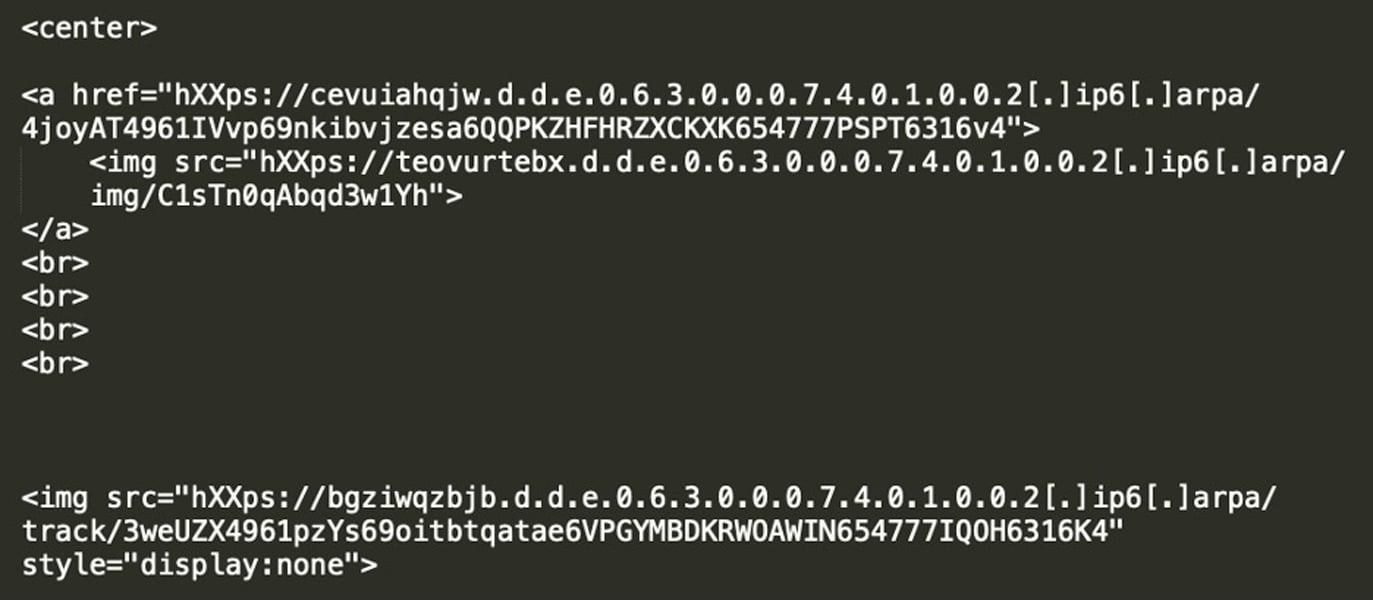 |
Sources: Infoblox
Mitigation Recommendations
- User awareness: Do not click unexpected links or images in emails; navigate to services directly via known, official URLs.
- Email security: Deploy advanced phishing‑detection solutions that inspect image links and resolve DNS records, not just domain names.
- DNS hygiene: DNS providers should restrict record types allowed in reverse‑DNS zones to PTR only, or enforce stricter validation.

Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use mathematics to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to discover:
- The top 10 techniques used by modern ransomware
- How these tactics bypass current defenses
- Recommendations to strengthen your security stack