Germany warns of Signal account hijacking targeting senior figures
Source: Bleeping Computer
Overview
Germany’s domestic intelligence agency is warning of suspected state‑sponsored threat actors targeting high‑ranking individuals in phishing attacks via messaging apps like Signal. The attacks combine social engineering with legitimate features to steal data from politicians, military officers, diplomats, and investigative journalists in Germany and across Europe.
The security advisory is based on intelligence collected by the Federal Office for the Protection of the Constitution (BfV) and the Federal Office for Information Security (BSI).
“A defining characteristic of this attack campaign is that no malware is used, nor are technical vulnerabilities in the messaging services exploited,” the two agencies inform.
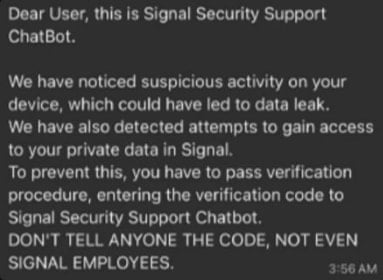
According to the advisory, the attackers contact the target directly, pretending to be from the support team of the messaging service or the support chatbot. The goal is to covertly gain access to one‑to‑one and group chats as well as contact lists of the affected individuals.
Attack Methodology
Full account takeover
In this variant, attackers impersonate Signal’s support service and send a fake security warning to create a sense of urgency. The target is then tricked into sharing their Signal PIN or an SMS verification code, which allows the attackers to register the account on a device they control. They then hijack the account and lock out the victim.
Source: BSI
Device‑pairing abuse
The second variant uses a plausible ruse to convince the target to scan a QR code. This abuses Signal’s legitimate linked‑device feature that allows adding the account to multiple devices (computer, tablet, phone). The victim’s account is paired with a device controlled by the attacker, who gains access to chats and contacts without raising any flags.

Source: BSI
Although the attacks were observed on Signal, the bulletin warns that WhatsApp also supports similar functionality and could be abused in the same way.
Related Threats
- Last year, Google threat researchers reported that the QR‑code pairing technique was employed by Russian state‑aligned threat groups such as Sandworm.
- Ukraine’s Computer Emergency Response Team (CERT‑UA) also attributed similar attacks to Russian hackers, targeting WhatsApp accounts.
- Multiple threat actors, including cybercriminals, have since adopted the technique in campaigns like GhostPairing (BleedingComputer article) to hijack accounts for scams and fraud.
Mitigation Recommendations
- Do not reply to unsolicited Signal messages claiming to be from support; Signal never contacts users directly.
- Block and report any suspicious accounts that claim to be support.
- Enable the Registration Lock option under Settings > Account. When active, Signal will require a PIN you set whenever someone tries to register your phone number with the app. Without the PIN, registration on another device fails.
- Regularly review the list of devices with access to your Signal account under Settings > Linked devices and remove any unrecognized devices.
Note: Losing your registration PIN can result in loss of access to your Signal account.