Zyxel warns of critical RCE flaw affecting over a dozen routers
Source: Bleeping Computer

Taiwan networking provider Zyxel has released security updates to address a critical vulnerability affecting over a dozen router models. The flaw allows unauthenticated attackers to gain remote command execution on unpatched devices.
Vulnerability Overview (CVE‑2025‑13942)
- Type: Command injection in the UPnP function
- Affected products:
- 4G LTE / 5G NR CPE
- DSL / Ethernet CPE
- Fiber ONTs
- Wireless extenders
- Impact: Unauthenticated remote attackers can execute operating‑system commands by sending maliciously crafted UPnP SOAP requests.
“It is important to note that WAN access is disabled by default on these devices, and the attack can be carried out remotely only if both WAN access and the vulnerable UPnP function have been enabled,” – Zyxel security advisory.
Exploitation Conditions
- WAN access must be enabled (disabled by default).
- UPnP must be enabled on the device.
Additional Patches
On the same day Zyxel also patched two high‑severity, post‑authentication command‑injection vulnerabilities:
- CVE‑2025‑13943 – CVE record
- CVE‑2026‑1459 – CVE record
Both allow threat actors with compromised credentials to execute OS commands.
Exposure Statistics
Shadowserver tracks nearly 120,000 Internet‑exposed Zyxel devices, including over 76,000 routers.
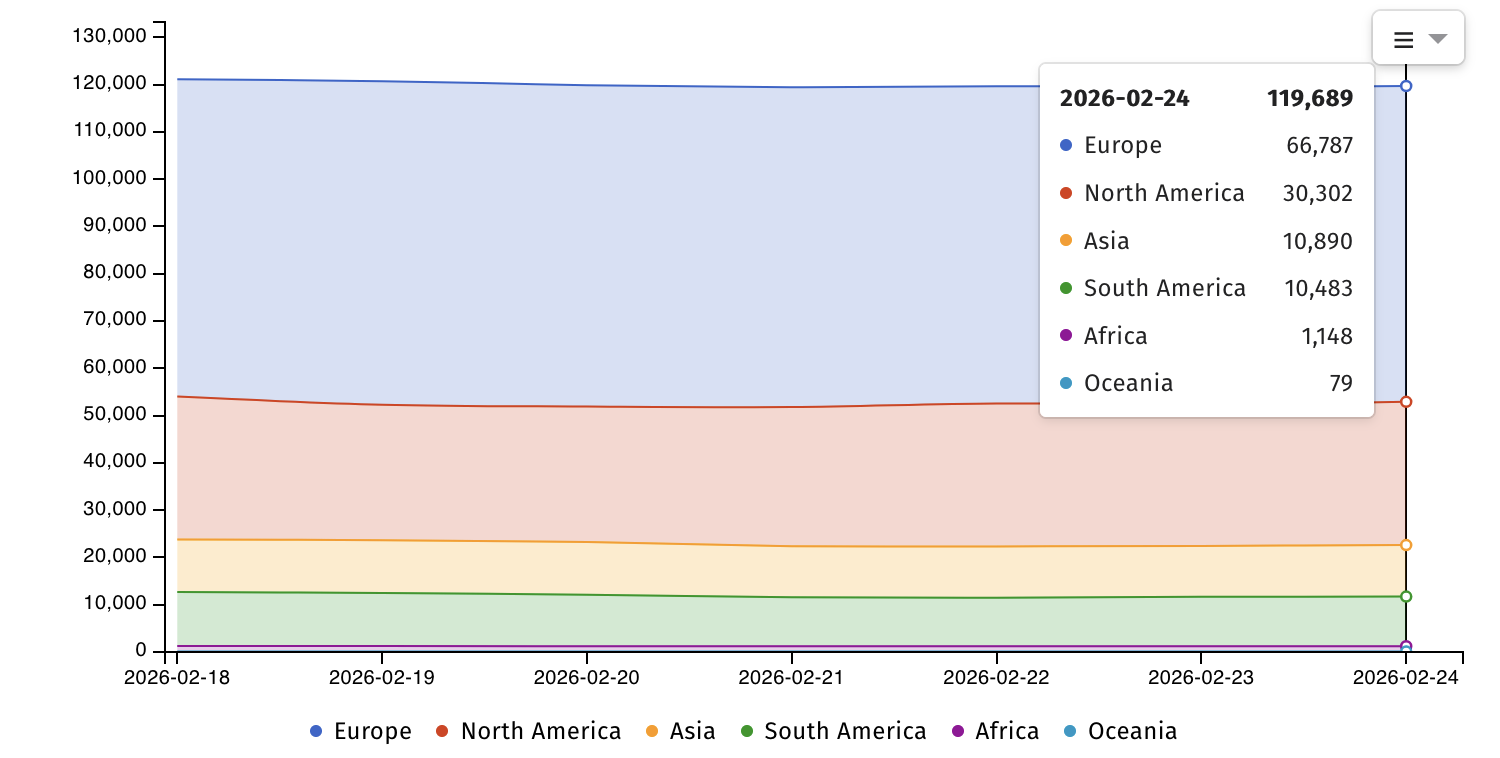
Internet‑exposed Zyxel devices (Shadowserver)
Government Tracking
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) is currently tracking 12 Zyxel vulnerabilities affecting routers, firewalls, and NAS devices that have been or are still actively exploited in the wild.
View CISA catalog
Legacy Devices and End‑of‑Life (EOL) Issues
Earlier this month Zyxel announced that it will not patch two zero‑day vulnerabilities (CVE‑2024‑40891, CVE‑2024‑40892) that are actively exploited in attacks targeting end‑of‑life routers still sold online. The company advises customers to replace the affected devices with newer, supported models.
Affected legacy models:
VMG1312‑B10A, VMG1312‑B10B, VMG1312‑B10E, VMG3312‑B10A, VMG3313‑B10A, VMG3926‑B10B, VMG4325‑B10A, VMG4380‑B10A, VMG8324‑B10A, VMG8924‑B10A, SBG3300, SBG3500.
Company Reach
Zyxel claims that more than 1 million businesses use its networking products across 150 markets worldwide.