ZeroDayRAT malware grants full access to Android, iOS devices
Source: Bleeping Computer

A new commercial mobile spyware platform dubbed ZeroDayRAT is being advertised to cyber‑criminals on Telegram as a tool that provides full remote control over compromised Android and iOS devices. The malware provides buyers with a full‑featured panel for managing infected devices, reportedly supporting Android 5 through 16 and iOS up to version 26 (latest).
Researchers at mobile‑threat‑hunting company iVerify say that ZeroDayRAT not only steals data but also enables real‑time surveillance and financial theft.
Dashboard overview
The dashboard shows compromised devices and information about the model, operating system version, battery status, SIM details, country, and lock state.
.jpg)
Source: iVerify
The malware can log app usage, activity timelines, SMS message exchanges, and provides an overview to the operator. Other tabs display all received notifications and registered accounts on the infected device, showing email/user ID and potentially enabling brute‑forcing and credential stuffing.
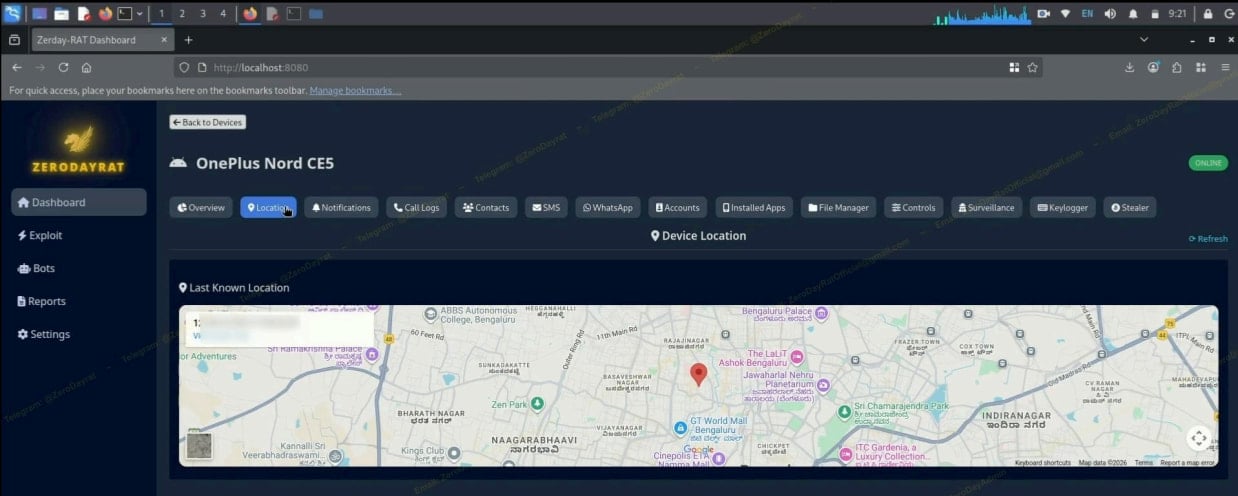
Real‑time location tracking
If GPS access is secured, the malware can track the victim in real time and draw their current position on a Google Maps view, with full location history.
Source: iVerify
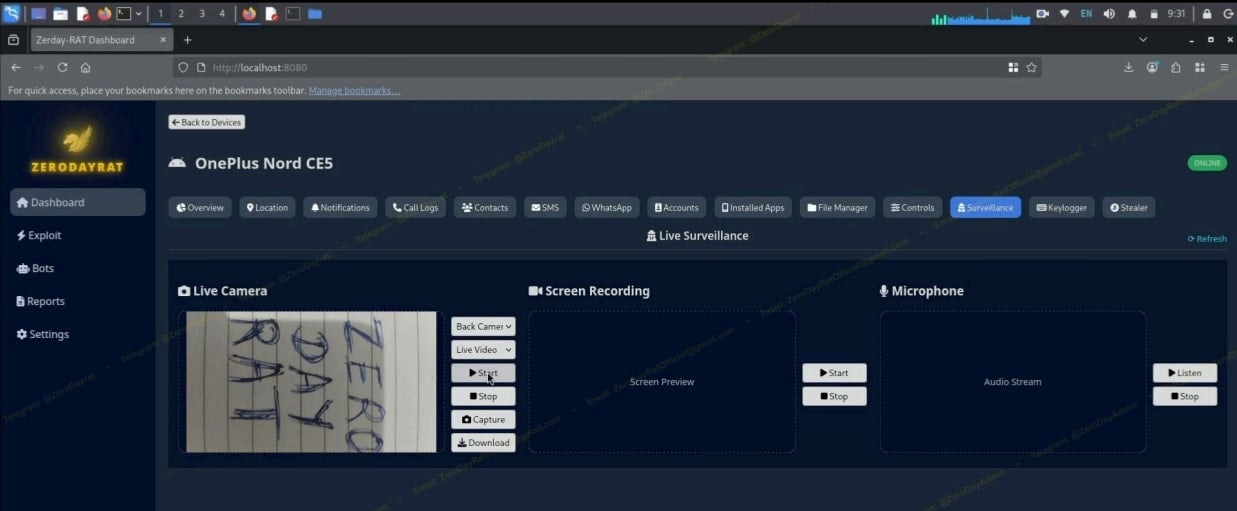
Camera, microphone, and screen capture
ZeroDayRAT supports active operations such as activating the device’s front and rear cameras and microphone to gain a live media feed, or recording the victim’s screen to expose other secrets.
Source: iVerify
Credential interception and OTP theft
When SMS permissions are obtained, the malware can capture incoming one‑time passwords (OTPs), enabling 2FA bypass, and can also send SMS from the victim’s device. A built‑in keylogging module captures user input, including passwords, gestures, and screen‑unlock patterns.
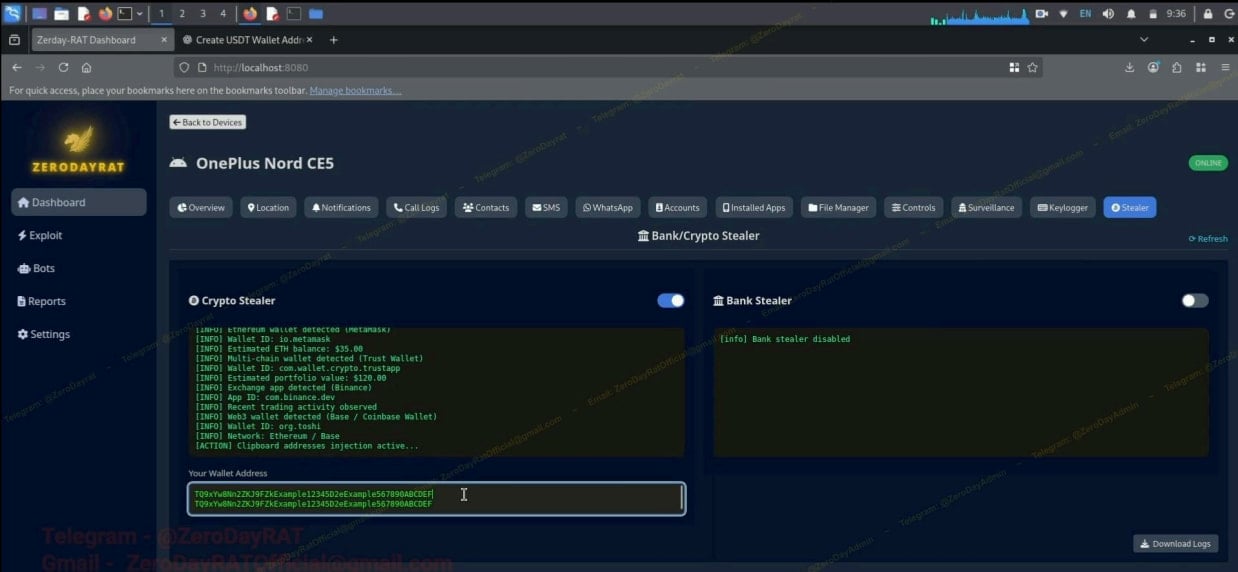
Crypto and bank stealer modules
A cryptocurrency stealer scans wallet apps such as MetaMask, Trust Wallet, Binance, and Coinbase, logs wallet IDs and balances, and attempts clipboard address injection, replacing copied wallet addresses with attacker‑controlled ones. The bank stealer targets online banking apps, UPI platforms (Google Pay, PhonePe), and payment services (Apple Pay, PayPal), stealing credentials by overlaying fake screens.
Source: iVerify
Mitigation recommendations
- Install apps only from official stores (Google Play on Android, Apple App Store on iOS).
- Use reputable publishers and keep the operating system and apps up to date.
- High‑risk users should enable Lockdown Mode on iOS and Advanced Protection on Android.
- Monitor device permissions and revoke unnecessary access (e.g., camera, microphone, SMS).
- Employ mobile‑device‑management (MDM) solutions in enterprise environments to detect and block unauthorized remote‑control tools.
Compromise of a single device can expose personal privacy and lead to significant financial losses, while a compromised employee device could result in broader enterprise breaches.
