UK warns of Chinese hackers using proxy networks to evade detection
Source: Bleeping Computer

Joint Advisory Summary
The United Kingdom’s National Cyber Security Centre (NCSC‑UK) and international partners warned that China‑nexus hackers are increasingly using large‑scale proxy networks of hijacked consumer devices to evade detection and disguise their malicious activity.
The advisory, co‑signed by agencies from the United States, Australia, Canada, Germany, Japan, the Netherlands, New Zealand, Spain, and Sweden, states that the majority of Chinese hacking groups have shifted from individually procured infrastructure to vast botnets of compromised devices—primarily small office and home office (SOHO) routers, internet‑connected cameras, video recorders, and network‑attached storage (NAS) equipment.
These massive botnets allow threat actors to route traffic through chains of compromised devices, entering a network at one point, passing through multiple intermediate nodes, and exiting near the intended target to avoid geographic detection.
“The NCSC believes that the majority of China‑nexus threat actors are using these networks … multiple covert networks have been created and are being constantly updated, and that a single covert network could be being used by multiple actors,” the joint advisory reads.
“These networks are mainly made up of compromised Small Office Home Office (SOHO) routers, as well as Internet of Things (IoT) and smart devices.”
— Joint advisory (NCSC)
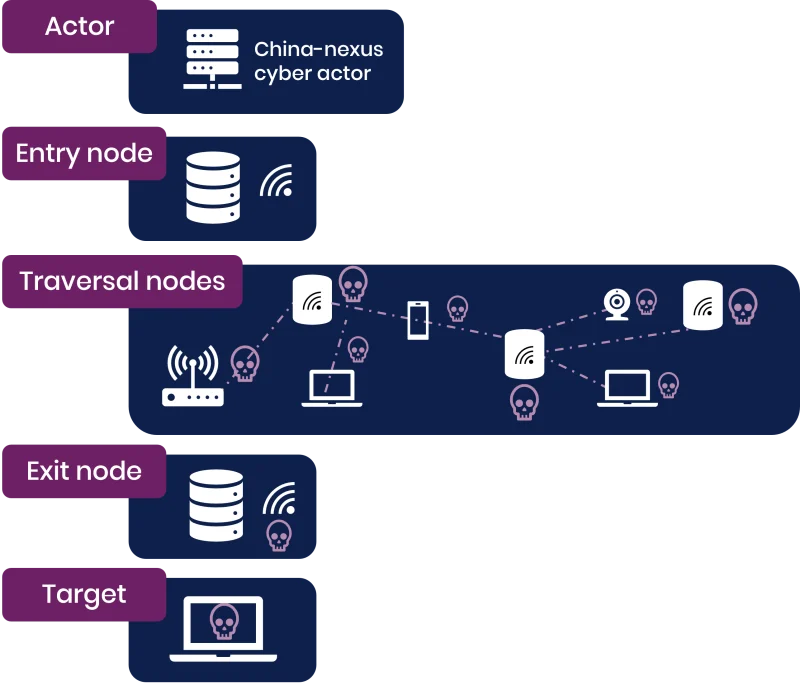
Covert network basic setup (NCSC‑UK)
Notable Botnets
Raptor Train
- Scope: Infected more than 260,000 devices worldwide in 2024.
- Attribution: Linked by the FBI to the Chinese state‑sponsored Flax Typhoon hacking group and the Chinese company Integrity Technology Group (sanctioned in January 2025).
- Disruption: The FBI disrupted Raptor Train in September 2024 with assistance from Black Lotus Labs after linking it to campaigns targeting military, government, higher‑education, telecommunications, defense‑industrial‑base (DIB), and IT sectors, primarily in the U.S. and Taiwan.
- References:
KV‑Botnet
- Operator: Chinese state‑backed Volt Typhoon threat group.
- Composition: Primarily vulnerable Cisco and Netgear routers that were out‑of‑date and no longer receiving security patches.
- Disruption & Revival:
- The FBI disrupted KV‑Botnet by wiping malware from infected routers in January 2024.
- Volt Typhoon began reviving the botnet in November 2024 after an initial failed rebuild attempt in February 2024.
- References:
Impact and Recommendations
“Botnet operations represent a significant threat to the UK by exploiting vulnerabilities in everyday internet‑connected devices with the potential to carry out large‑scale cyber attacks,” said Paul Chichester, NCSC‑UK’s Director of Operations.
Western intelligence agencies warned that traditional defenses based on static blacklists of malicious IP addresses are becoming less effective as these botnets continuously add new compromised nodes.
Recommended defensive measures
- Implement multifactor authentication (MFA) across all accounts.
- Map and inventory edge devices (routers, IoT, cameras, NAS).
- Leverage dynamic threat feeds that include known covert‑network indicators.
- Apply IP allowlists, zero‑trust controls, and machine‑certificate verification where possible.
- Regularly patch and update firmware on SOHO routers and IoT devices.
These steps help organizations of any size mitigate the risk posed by rapidly evolving proxy‑network botnets used by China‑nexus threat actors.