Threat actor uses Microsoft Teams to deploy new “Snow” malware
Source: Bleeping Computer

Overview
A threat group tracked as UNC6692 uses social engineering to deploy a custom malware suite named “Snow.” The suite includes a browser extension, a tunneler, and a backdoor. Their goal is to steal sensitive data after deep network compromise through credential theft and domain takeover.
According to Google’s Mandiant researchers, the attacker employs “email bombing” tactics to create urgency, then contacts targets via Microsoft Teams, posing as IT helpdesk agents.
A recent Microsoft report highlighted the growing popularity of this tactic, tricking users into granting attackers remote access via Quick Assist or other remote‑access tools.
Attack Methodology
- Initial Contact – Victims receive an urgent email prompting them to click a link to install a “patch” that supposedly blocks email spam.
- Dropper Execution – The link delivers a dropper that runs AutoHotkey scripts, installing SnowBelt, a malicious Chrome extension.
- Extension Execution – SnowBelt runs on a headless Microsoft Edge instance, remaining invisible to the user.
- Persistence – Scheduled tasks and a startup‑folder shortcut are created.
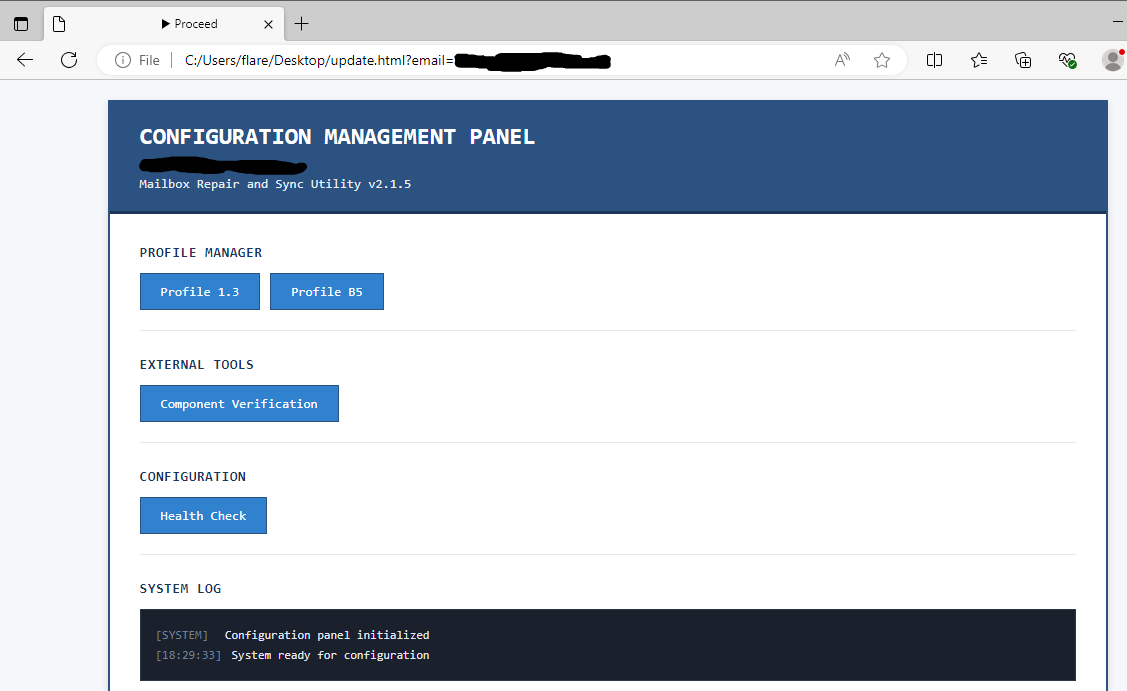 Malicious page used in the attacks
Malicious page used in the attacks
Source: Google
Malware Components
SnowBelt (Chrome Extension)
- Acts as a persistence mechanism.
- Relays commands to the backdoor.
SnowGlaze (Tunneler)
- Establishes a WebSocket tunnel to mask communications between the host and the C2 infrastructure.
- Provides SOCKS proxy capabilities for arbitrary TCP traffic.
SnowBasin (Python‑based Backdoor)
- Runs a local HTTP server.
- Executes attacker‑supplied CMD or PowerShell commands.
- Returns results through the same tunnel.
- Supports remote shell access, data exfiltration, file download, screenshot capture, and basic file management.
- Allows the operator to issue a self‑termination command.
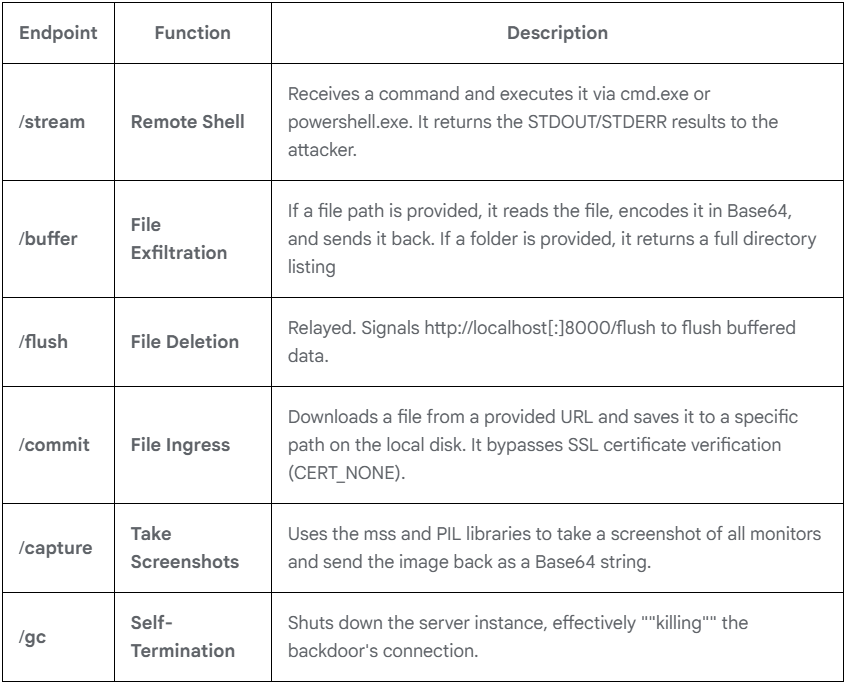 SnowBasin capabilities
SnowBasin capabilities
Source: Google
Post‑Compromise Activities
- Internal reconnaissance: Scanning for services such as SMB and RDP to identify additional targets.
- Lateral movement: Dumping LSASS memory to extract credentials, then using pass‑the‑hash to authenticate to other hosts, eventually reaching domain controllers.
- Data extraction: Deploying FTK Imager to copy the Active Directory database and the SYSTEM, SAM, and SECURITY registry hives.
- Exfiltration: Using LimeWire to transfer the harvested files out of the network, granting attackers domain‑wide credential access.
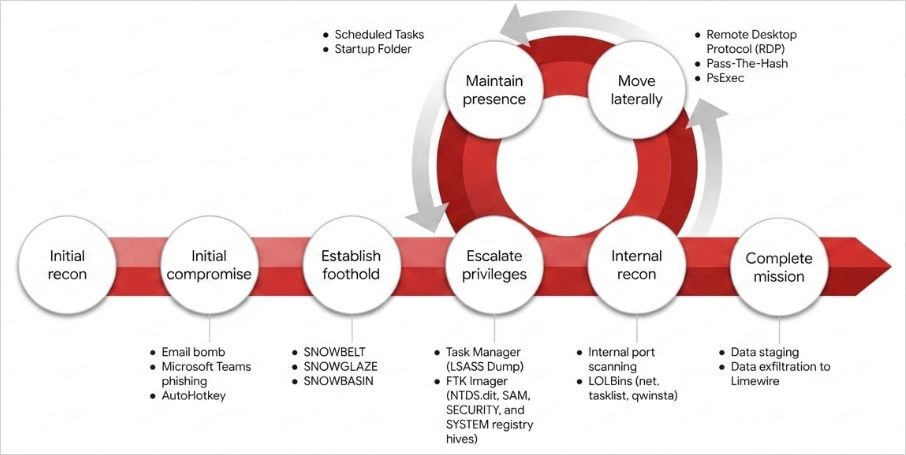 Attack lifecycle
Attack lifecycle
Source: Google
Indicators of Compromise (IoCs)
The report provides extensive IoCs and YARA rules to help detect the “Snow” toolset. (Refer to the original Mandiant report for the full list.)