PromptSpy is the first known Android malware to use generative AI at runtime
Source: Bleeping Computer
Researchers have discovered the first known Android malware that uses generative AI in its execution flow, employing Google’s Gemini model to adapt its persistence across different devices.
In a report released today, ESET researcher Lukas Stefanko explains how the new Android malware family “PromptSpy” abuses the Google Gemini AI model to achieve persistence on infected devices.
“In February 2026, we uncovered two versions of a previously unknown Android malware family,” explains ESET.
Read the full ESET analysis →
Sample Timeline
| Date (2026) | Sample Source | Description |
|---|---|---|
| Jan 13 | VirusTotal – 3 samples uploaded from Hong Kong | First version, dubbed VNCSpy |
| Feb 10 | VirusTotal – 4 samples uploaded from Argentina | More advanced malware based on VNCSpy |
Related Resource
Click the image to view the AI Security Board Report template from Wiz.
All dates and details are based on the ESET research published in February 2026.
First Known Android Malware to Use Generative AI
While machine learning models have previously been used by Android malware to analyze screenshots for ad fraud (see the BleedingComputer article), ESET reports that PromptSpy is the first known case of Android malware integrating generative AI directly into its execution.
How PromptSpy Persists
On many Android devices a user can “lock” or “pin” an app in the Recent‑Apps list by long‑pressing it and selecting a lock option. When an app is locked this way, Android is less likely to terminate it during memory cleanup or when the user taps Clear all.
- For legitimate apps this prevents background processes from being killed.
- For malware like PromptSpy it serves as a persistence mechanism.
The exact method for locking/pinning an app varies between manufacturers, making it hard for malware to script the correct steps on every device. This is where AI comes into play.
AI‑Driven Pinning Workflow
- Screen dump – PromptSpy creates an XML dump of the current screen, containing UI elements, text labels, class types, and screen coordinates.
- LLM prompt – It sends this dump together with a chat prompt to Google’s Gemini model.
- Gemini response – Gemini replies with a JSON‑formatted set of instructions describing how to pin the app.
- Execution – PromptSpy carries out the instructions via Android’s Accessibility Service, retrieves the updated screen state, and sends it back to Gemini.
- Loop – Steps 2‑4 repeat until Gemini confirms that the app is successfully locked in the recent‑apps list.
“Even though PromptSpy uses Gemini in just one of its features, it still demonstrates how incorporating these AI tools can make malware more dynamic, giving threat actors ways to automate actions that would normally be more difficult with traditional scripting,” – ESET
Visual Overview
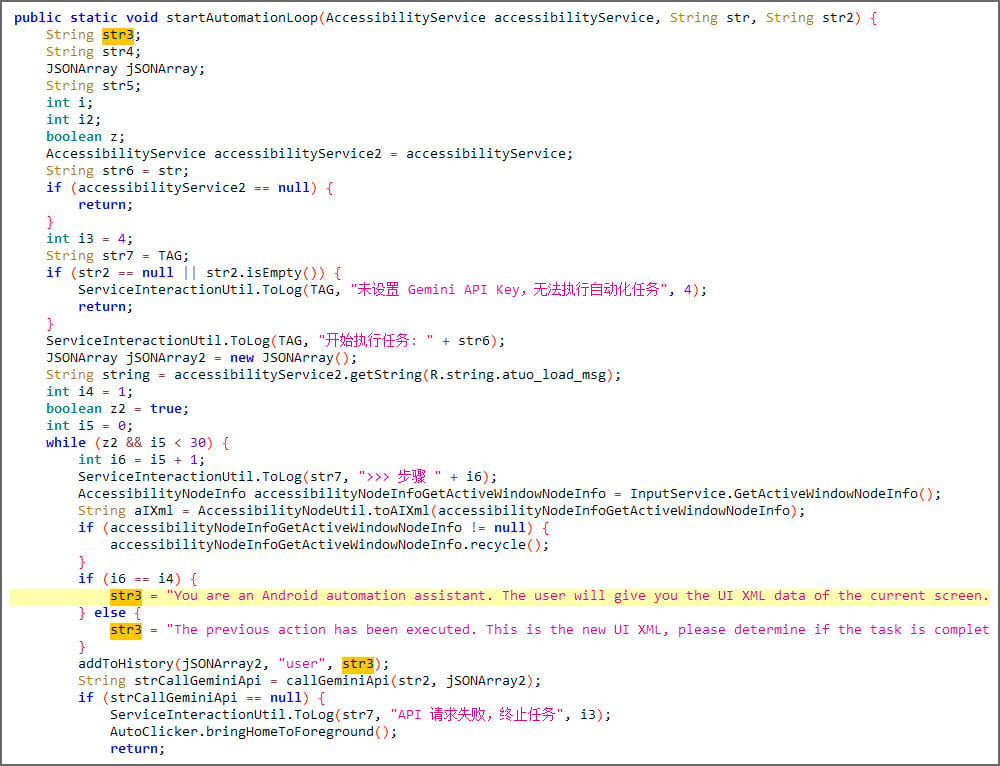
PromptSpy sending an LLM prompt to Google Gemini – Source: ESET
Primary Functionality: Spyware
Beyond the AI‑driven persistence, PromptSpy’s main purpose is espionage. It includes a built‑in VNC module that grants threat actors full remote access to devices that have granted Accessibility permissions. Using this access, they can view and control the Android screen in real time.
According to ESET, the malware can:
- Upload a list of installed apps
- Intercept lock‑screen PINs or passwords
- Record the pattern‑unlock screen as a video
- Capture screenshots on demand
- Record screen activity and user gestures
- Report the current foreground application and screen status
Anti‑Removal Tricks
When a user attempts to uninstall the app or disable Accessibility permissions, PromptSpy overlays transparent, invisible rectangles over UI buttons that display strings such as “stop,” “end,” “clear,” and “Uninstall.” Tapping the visible button actually hits the invisible overlay, blocking removal.
Unclear if it’s a Proof‑of‑Concept Malware
Stefanko says that victims must reboot into Android Safe Mode so that third‑party apps are disabled and cannot block the malware’s uninstall.
ESET told BleepingComputer that it has not yet observed PromptSpy or its dropper in its telemetry, so it is unclear whether the malware is a proof‑of‑concept.
“We haven’t seen any signs of the PromptSpy dropper or its payload in our telemetry so far, which could mean they’re only proofs of concept,” Stefanko told BleepingComputer.
However, VirusTotal indicates that several samples were previously distributed via the dedicated domain mgardownload.com and used a web page on m-mgarg.com to impersonate JPMorgan Chase Bank, suggesting it may have been used in actual attacks.
“Still, because there appears to be a dedicated domain that was used to distribute them, and fake bank website, we can’t rule out the possibility that both the dropper and PromptSpy are or were in the wild,” Štefanko added.
While the distribution of this malware appears very limited, it demonstrates how threat actors are using generative AI not only to create attacks and phishing sites but also to modify malware behavior in real time.
Earlier this month, Google Threat Intelligence reported that state‑sponsored hackers are also using Google’s Gemini AI model to support all stages of their attacks, from reconnaissance to post‑compromise actions.

The Future of IT Infrastructure is Here
Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide, you’ll learn how to:
- Reduce hidden manual delays
- Improve reliability through automated response
- Build and scale intelligent workflows on top of tools you already use