Phishing campaign targets freight and logistics orgs in the US, Europe
Source: Bleeping Computer
Cleaned‑up Markdown

A financially motivated threat group dubbed **“Diesel Vortex”** is stealing credentials from freight and logistics operators in the U.S. and Europe through phishing attacks that use **52 domains**.
In a campaign that has been running since **September 2025**, the threat actor has stolen **1,649 unique credentials** from platforms and service providers critical to the freight industry.
**Victims include:**
- DAT Truckstop
- TIMOCOM
- Teleroute
- Penske Logistics
- Girteka
- Electronic Funds Source (EFS)
[](https://www.wiz.io/lp/ai-security-board-report-template?utm_source=bleepingcomputer&utm_medium=display&utm_campaign=FY26Q4_INB_FORM_AI-Security-Board-Report-Template&sfcid=701Vh00000Wn7E1IAJ&utm_term=FY27-bleepingcomputer-article-970x250&utm_content=AI-Board-Report)
Researchers at the typosquatting‑monitoring platform **Have I Been Squatted** uncovered the campaign after finding an exposed repository containing an SQL database from a phishing project the threat actor called **Global Profit** and marketed to other cybercriminals under the name **MC Profit Always**.
The repository also included a file with Telegram webhook logs that revealed communications between the phishing‑service operators. Based on the language used, the researchers believe that Diesel Vortex is an **Armenian‑speaking actor connected to Russian infrastructure**.
Have I Been Squatted’s analysis was joined by token‑generation infrastructure provider **Ctrl‑Alt‑Intel**, which connected the dots between operators, infrastructure, and various companies using open‑source intelligence.
In a lengthy technical report, the typosquatting‑protection provider states that it uncovered **nearly 3,500 stolen credential pairs**, with **1,649 of them being unique**.
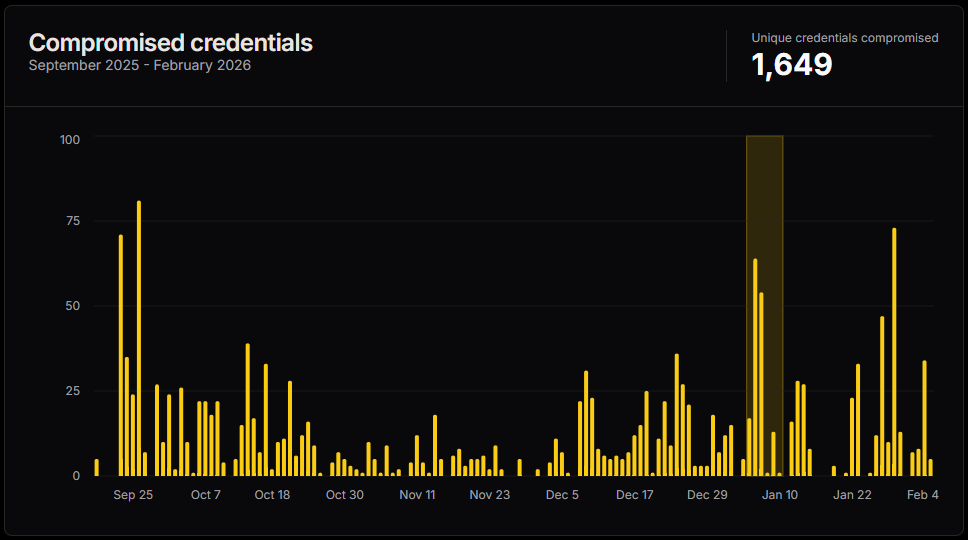
**Volume of Diesel Vortex credential theft**
*Source: Have I Been Squatted*
The researchers also found a **mind map** created by a group member that describes a “highly organised operation” complete with:
- a call‑centre
- mail support
- programmer **roles**
- staff responsible for finding drivers, carriers, and logistics contacts
The map details acquisition channels that include the **DAT One marketplace**, email campaigns, rate‑confirmation fraud, and revenue streams for various operational tiers.
> “The [Diesel Vortex] group built dedicated phishing infrastructure for platforms used daily by freight brokers, trucking companies, and supply‑chain operators. Load boards, fleet‑management portals, fuel‑card systems, and freight exchanges were all in scope,”
> — *Have I Been Squatted researchers*
> “These platforms sit at the intersection of high transaction volumes and the targeted workforce isn’t typically the primary focus of enterprise security programs, and the operators clearly knew it.”
### Attack Mechanics
- Phishing emails are sent via a kit’s mailer using **Zoho SMTP** and **Zeptomail**.
- Cyrillic homoglyph tricks are employed in the sender and subject fields to evade security filters.
- Voice phishing and infiltration of Telegram channels frequented by trucking and logistics personnel are also used.
When a victim clicks a phishing link, they land on a minimal HTML page on a **`.com`** domain that displays a full‑screen iframe loading the phishing content, followed by a **9‑stage cloaking process** on the system domain (**`.top` / `.icu`**).
The phishing pages are pixel‑level clones of the targeted logistics platforms and may capture:
- credentials (username/password)
- MC/DOT numbers, RMIS login details, PINs
- two‑factor authentication codes, security tokens
- payment amounts, payee names, check numbers
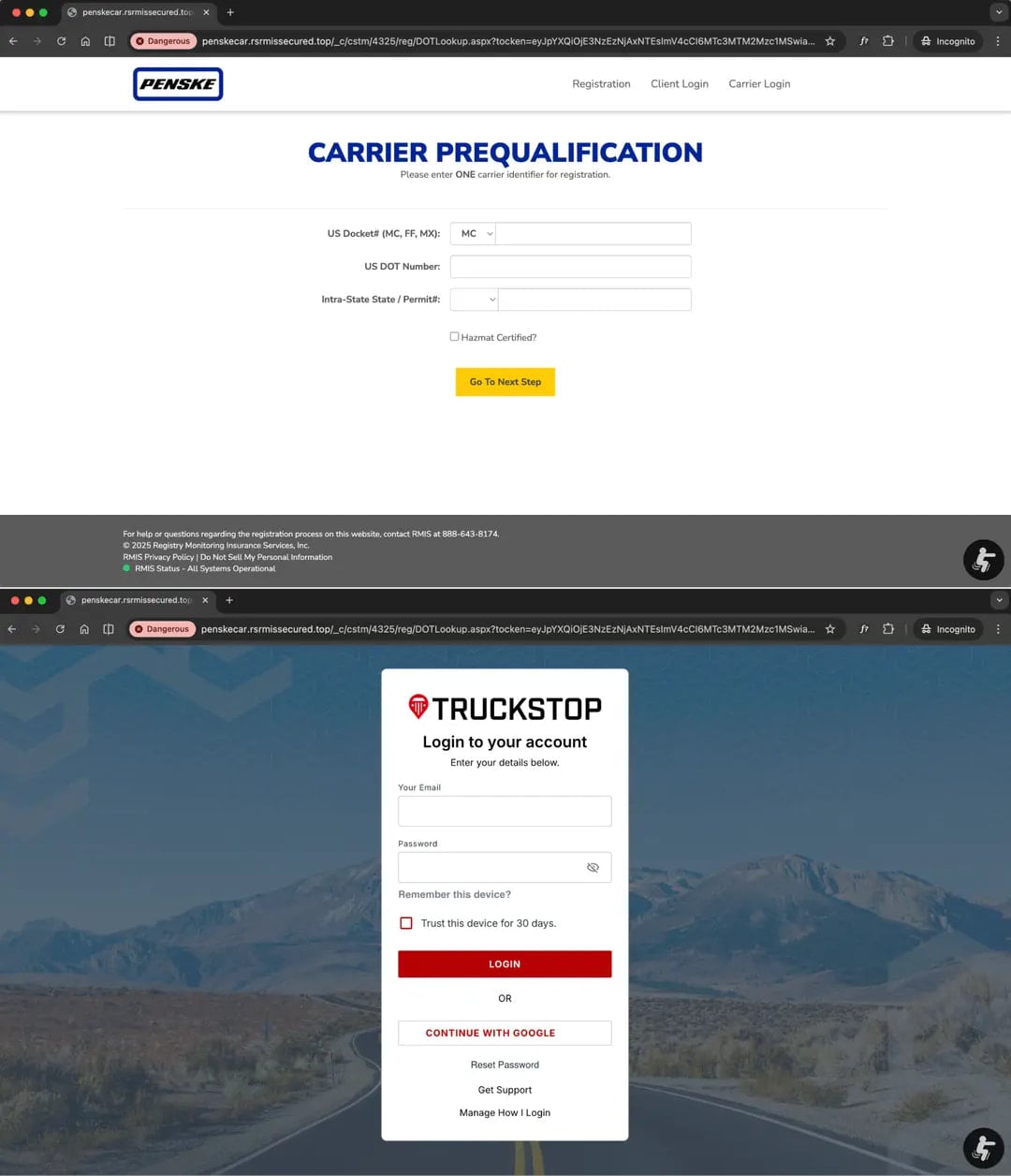
**Two phishing pages used in the same attack**
*Source: Have I Been Squatted*
The phishing process is under the operator’s direct control; they decide when to approve steps and activate the next phases via **Telegram bots**. Possible actions include:
- requesting passwords for Google, Microsoft Office 365, Yahoo, etc.
- prompting for 2FA methods
- redirecting the victim or blocking them mid‑session
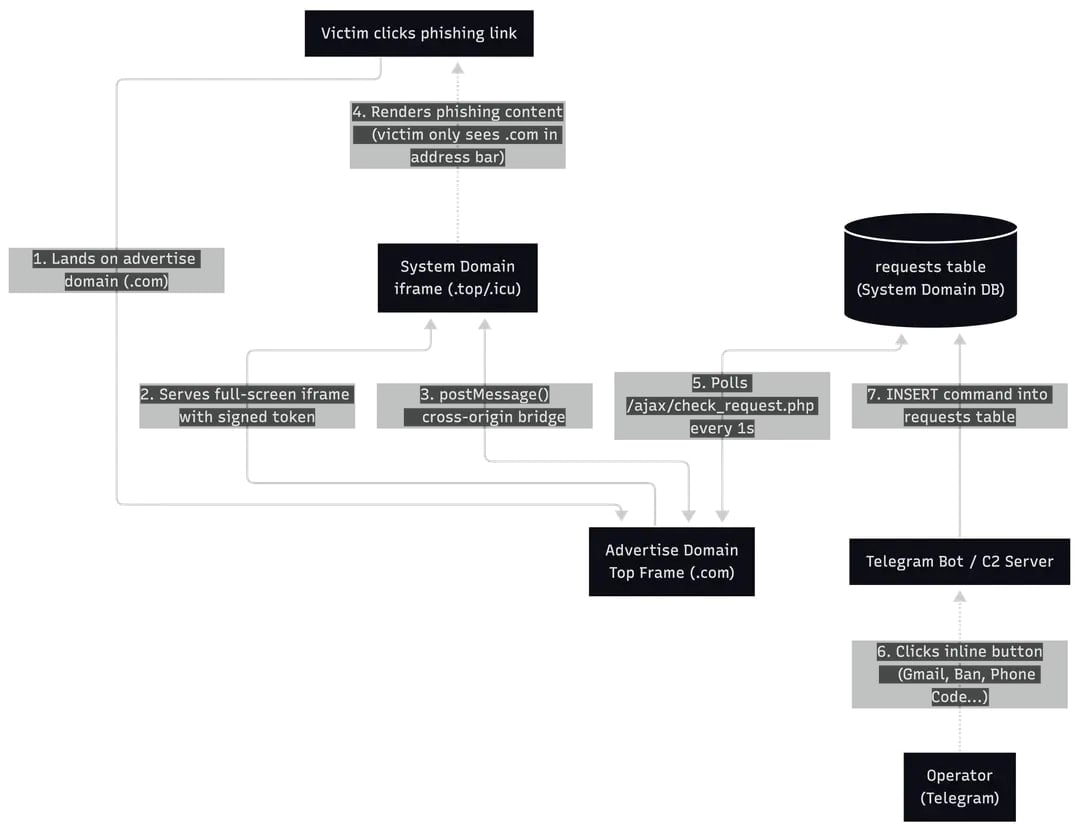
**Overview of the attack**
*Source: Have I Been Squatted*
### Disruption & Investigation
The Diesel Vortex operation—including panel and phishing domains and GitLab repositories—was disrupted after a coordinated action involving **GitLab, Cloudflare, Google Threat Intelligence, CrowdStrike, and Microsoft Threat Intelligence Center**.
Ctrl‑Alt‑Intel conducted an **OSINT investigation** starting from operators’ Telegram chats in Armenian about stealing cargo or funds, and an email address. A domain name found in the phishing panel’s source code linked to individuals and companies in Russia involved in wholesale trade, transportation, and warehousing.
> “The same email used to register phishing infrastructure appears in Russian corporate filings for logistics companies operating in the same vertical targeted by Diesel Vortex.”
Based on the evidence, researchers determined that Diesel Vortex not only stole credentials but also coordinated activities related to:
- freight impersonation
- mailbox compromise
- **double‑brokering** or cargo diversion
*Double brokering* refers to using stolen carrier identities to book loads and then reassign or divert freight cargo, allowing the goods to be sent to **fraudulent pickup points**.
---
*All images and data are reproduced from the original sources cited above.*
```markdown
[Hackers use RMM tools to breach freighters and steal cargo shipments](https://bleepingcomputer.com/news/security/hackers-use-rmm-tools-to-breach-freighters-and-steal-cargo-shipments/) so they can be stolen.
The full indicators of compromise (IoCs), including network, Telegram, infrastructure, email, and cryptocurrency addresses, are available at the bottom of the **Have I Been Squatted** report.
The future of IT infrastructure is here
Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide, you’ll learn how your team can:
- Reduce hidden manual delays
- Improve reliability through automated response
- Build and scale intelligent workflows on top of tools you already use