Making infrastructure access lighter, simpler, and smarter
Source: Tailscale Blog
Modern Infrastructure Access
“Teams are cloud‑native, workloads are ephemeral, and access is increasingly identity‑based.”
Yet one expectation remains unchanged: when something goes wrong, you need clear answers. You must be able to answer:
- Who accessed a system?
- What actions they performed?
- When did it happen?
- Can you prove it later?
The Legacy PAM Model
Historically, answering these questions required:
- Deploying heavyweight systems that sit alongside your connectivity layer.
- Using separate tools for:
- Access control
- Auditing
- Session recording
- Long‑term retention
Drawbacks
- Expensive to provision and maintain.
- Complex to integrate and operate.
- Misaligned with the way modern, cloud‑native teams actually work.
Tailscale’s Approach
Tailscale bridges the gap by extending identity‑aware auditing and visibility across:
- Kubernetes workloads
- Network traffic flows
- SSH sessions
All of this is built on the same lightweight connectivity model that teams already rely on, eliminating the need for bulky, separate PAM stacks.
Key Benefits
| Benefit | How Tailscale Delivers It |
|---|---|
| Unified visibility | Single pane of glass for K8s, network, and SSH |
| Identity‑first | Audits tied to user identities, not IPs or keys |
| Low overhead | No extra appliances or agents beyond the Tailscale client |
| Scalable | Works seamlessly as workloads scale up or down |
| Compliance‑ready | Immutable logs that can be retained for audit periods |
TL;DR
- Traditional PAM is costly and complex for modern, cloud‑native environments.
- Tailscale provides a lightweight, identity‑centric solution that gives you the same auditability and control without the baggage.
Your teams keep moving fast; your security and audit capabilities keep pace.
From “Can they connect?” to “What actually happened?”
Tailscale has always focused on “who can connect to what,” with identity, zero‑trust, and least‑privilege networking as its foundation. The Winter Update builds on that foundation by improving what you can see and prove after access is granted. Three new capabilities work together to do this:
- Kubernetes API proxy audit logging
- Actor identifiers in network flow logs
- Identity‑enriched SSH login logs on Linux
Individually, each improves visibility. Together, they create a much stronger access‑governance story—without introducing new infrastructure or workflows.
Clear, Queryable Records of Kubernetes Access
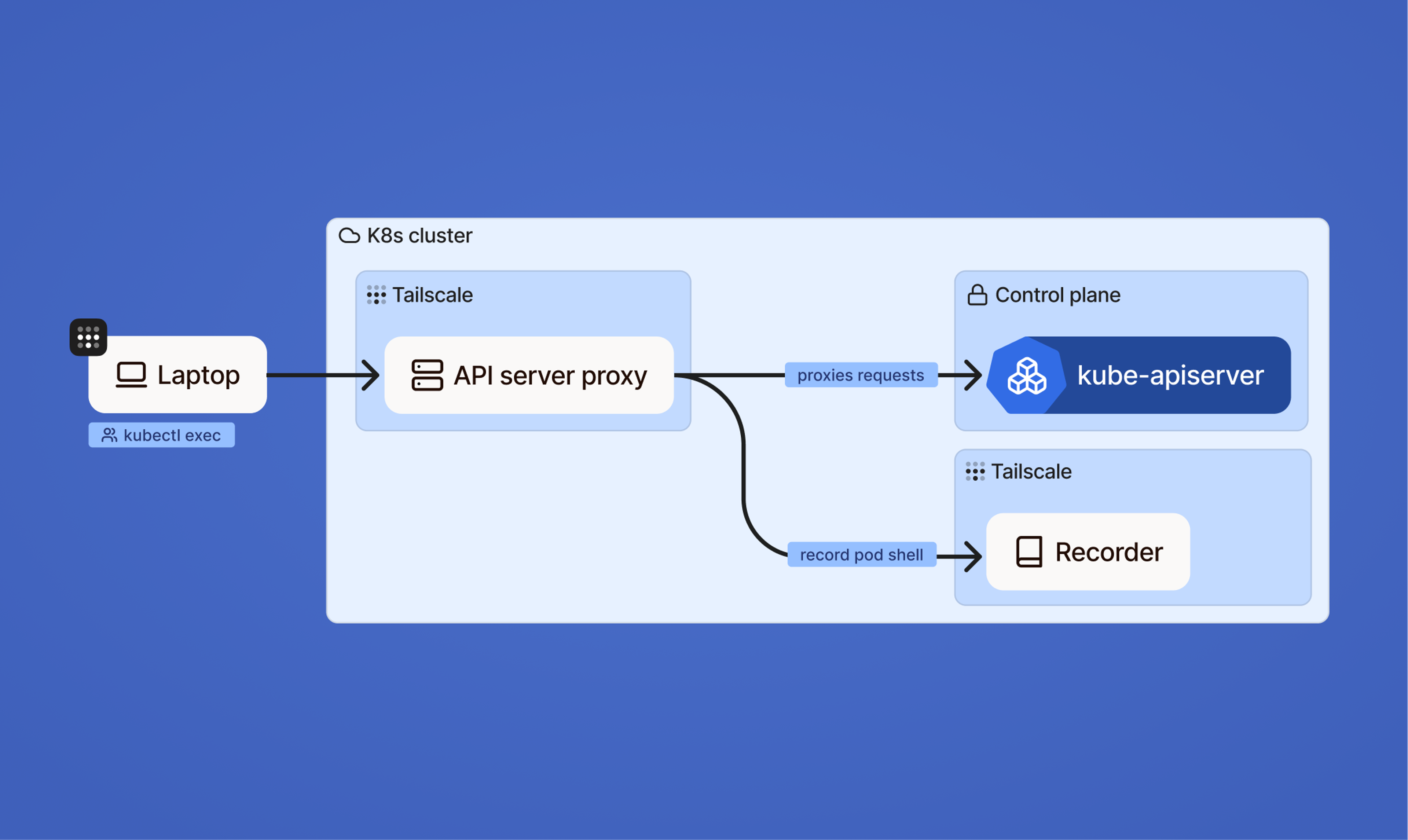
Tailscale’s Kubernetes API server proxy already lets teams record kubectl sessions via tsrecorder. While session recordings are useful, they don’t answer more granular questions such as:
- Who changed a specific resource?
- Which API call triggered an outage?
- What were the exact configuration values at a given moment?
Kubernetes API Proxy Audit Logging (beta)
With the new Kubernetes API Proxy Audit Logging (beta), Tailscale now:
- Captures every Kubernetes API request the moment it is received.
- Emits structured audit logs that are easy to query, search, and analyze.
- Extends existing PAM capabilities (e.g., Tailscale SSH recordings) by adding request‑by‑request visibility.
Why This Matters
- Fine‑grained visibility – Go beyond high‑level session recordings to see the exact HTTP requests made to the API server.
- Query‑ready format – Structured logs simplify forensic investigations and correlation of events.
- Long‑term retention – Logs can be exported to cold storage for compliance and archival needs.
- Reduced operational complexity – Connectivity, access control, and Kubernetes auditing are all handled within the same Tailscale platform, eliminating the need for multiple disparate tools.
Making Network Logs Human‑Readable {#making-network-logs-human-readable}
Network flow logs are essential for compliance, incident response, and troubleshooting, but they’re often painful to work with. IP addresses, ports, and opaque node IDs are hard to parse, making it difficult to pinpoint who was actually responsible for a given connection.
What’s new?
- Actor context enrichment – each log entry now includes:
- User identity
- Device identity
- Human‑readable device name
- Clear traffic origin – logs show who initiated traffic, not just where it came from.
Why it matters
- Security & compliance – teams can investigate incidents and perform audits without building separate enrichment pipelines.
- Actionable data – raw network data is transformed into meaningful access records, aligning network‑level visibility with modern access‑control thinking (users and devices instead of IP addresses and spreadsheets).
Visual overview
With this update, Tailscale turns opaque network logs into clear, identity‑driven records, simplifying investigations and improving overall security posture.
Marrying System Logs with Tailscale Identity
Linux already offers robust auditing frameworks—auditd, journald, and kauditd.
However, they can be noisy, costly to operate, and hard to interpret for access‑governance purposes.
Tailscale now integrates directly with these native Linux auditing systems, so SSH login events (both Tailscale SSH and traditional SSH) are logged with:
- Tailscale identity context (user, device, and ACL information)
- Local system user data (UID/GID, source IP, etc.)
Why this matters
- Clearer audit trails – Each login record shows who accessed what from which device.
- Reduced ambiguity – Identity information eliminates guesswork during investigations.
- Zero‑touch integration – Logs flow through the same pipelines (e.g.,
journalctl,auditdcollectors) that teams already use. - Lower operational overhead – No extra logging agents or proprietary collectors are required.
Result
By bridging identity‑based access with host‑level auditing, teams can maintain their existing logging workflows while gaining richer, more actionable SSH access records. This improves security visibility without adding complexity.
A simpler way to govern privileged access
Taken together, these capabilities address a familiar set of challenges:
- Auditing sensitive access across systems
- Tying actions back to real people and devices
- Retaining logs for compliance and forensic analysis
- Doing all of this without deploying complex, high‑friction infrastructure
Tailscale extends identity‑aware networking to include identity‑aware visibility. The same model that governs connectivity now provides the context required for auditing and governance.
Building towards a platform
The Winter Update reflects a broader direction: treating secure connectivity, access control, and audit observability as one cohesive system rather than separate concerns. By bringing these capabilities together, Tailscale is building toward a platform that:
- Reduces operational complexity
- Meets increasingly strict governance requirements
For teams looking to consolidate tooling without sacrificing visibility or control, this approach offers a practical alternative—designed to fit modern infrastructure instead of fighting it.

