Kyber ransomware gang toys with post-quantum encryption on Windows
Source: Bleeping Computer

Campaign overview
A new Kyber ransomware operation is targeting Windows systems and VMware ESXi endpoints. Rapid7 retrieved and analyzed two distinct Kyber variants in March 2026 during an incident response. Both variants were deployed on the same network, sharing a campaign ID and Tor‑based ransom infrastructure, indicating they were used by the same ransomware affiliate to maximize impact by encrypting all servers simultaneously.
“The ESXi variant is specifically built for VMware environments, with capabilities for datastore encryption, optional virtual machine termination, and defacement of management interfaces.” – Rapid7, blog post
BleepingComputer identified a single victim listed on the Kyber data‑extortion portal: a multi‑billion‑dollar American defense contractor and IT services provider.
 Kyber ransomware victim extortion portal
Kyber ransomware victim extortion portal
Source: BleepingComputer.com
ESXi variant
The ESXi variant is built for VMware environments. It enumerates all virtual machines (VMs) on the infrastructure, encrypts datastore files, and defaces the ESXi management interfaces with ransom notes that guide victims through payment and recovery.
Although the ransomware advertises “post‑quantum” encryption based on Kyber1024 key encapsulation, Rapid7 found that the Linux ESXi encryptor actually uses:
- ChaCha8 for file encryption
- RSA‑4096 for key wrapping
Encryption behavior:
| File size | Encryption method |
|---|---|
| 4 MB | Intermittent encryption based on operator configuration |
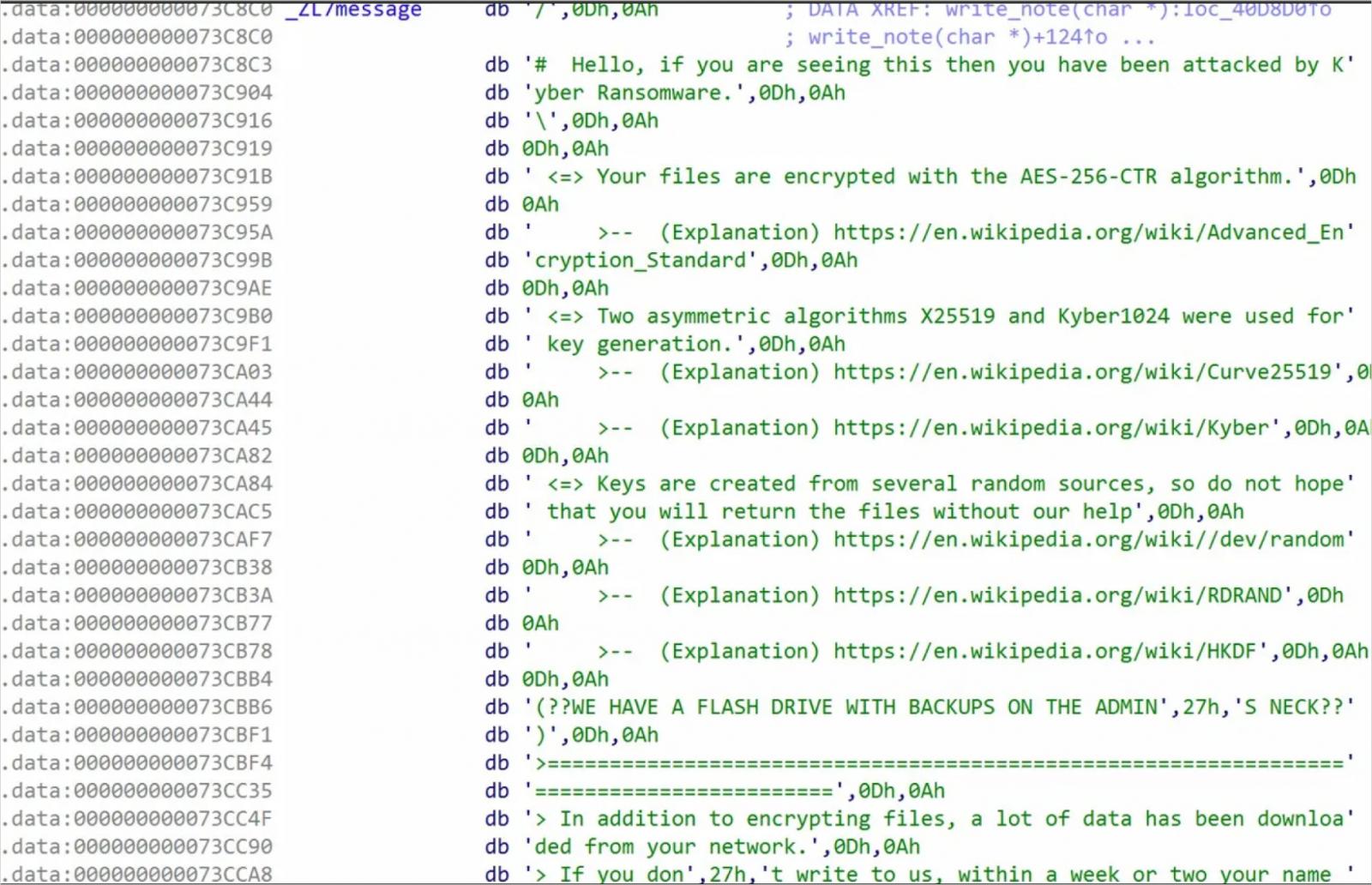 Ransom note embedded in the ELF binary
Ransom note embedded in the ELF binary
Source: Rapid7
Windows variant
The Windows variant is written in Rust and includes an “experimental” feature for targeting Hyper‑V. It appends the . #~~~ extension to encrypted files, terminates services, deletes backups, and can shut down Hyper‑V virtual machines.
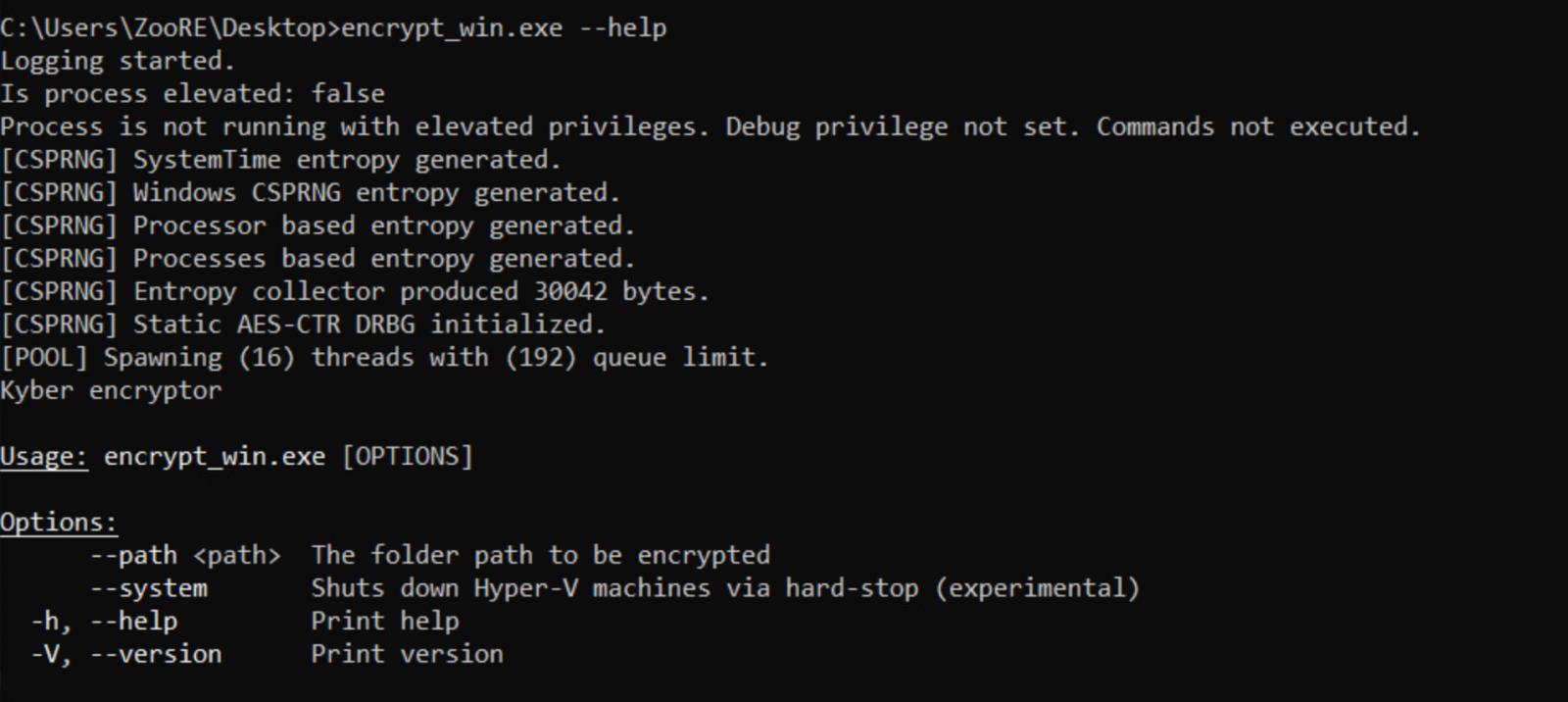 Kyber for Windows CLI
Kyber for Windows CLI
Source: Rapid7
Additional behaviors:
- Deleting shadow copies and the Windows Recycle Bin
- Disabling boot repair, clearing event logs, and wiping SQL, Exchange, and backup services
- Using a mutex that references a song on the Boomplay music platform (an unusual artifact)
Encryption mechanisms
ESXi encryption
- Symmetric cipher: ChaCha8
- Key protection: RSA‑4096
Windows encryption
- Key encapsulation: Kyber1024 (post‑quantum) and X25519 for key protection
- Bulk data encryption: AES‑CTR
“This confirms that Kyber is not used for direct file encryption. Instead, Kyber1024 protects the symmetric key material, while AES‑CTR handles bulk data encryption.” – Rapid7
Impact and mitigation
Both variants are designed to eliminate common data‑recovery paths, making files unrecoverable without the attacker’s private key. Whether the encryptor uses RSA or Kyber1024, victims must obtain the decryption key to restore data. Organizations should:
- Maintain offline, immutable backups.
- Monitor for unusual VM enumeration or datastore modifications in VMware environments.
- Apply strict network segmentation to limit ransomware spread.
- Keep systems patched and employ endpoint detection and response (EDR) solutions.
The Windows variant appears more technically mature, while the ESXi variant lacks some of its features. Rapid7’s analysis highlights the importance of understanding ransomware capabilities beyond headline‑grabbing claims such as “post‑quantum encryption.”