Kimwolf Botnet Swamps Anonymity Network I2P
Source: Krebs on Security
Overview
For the past week, the massive Internet of Things (IoT) botnet known as Kimwolf has been disrupting The Invisible Internet Project (I2P), a decentralized, encrypted communications network designed to anonymize and secure online communications. I2P users started reporting disruptions in the network around the same time the Kimwolf botmasters began relying on it to evade takedown attempts against the botnet’s control servers.
What is Kimwolf?
Kimwolf is a botnet that surfaced in late 2025 and quickly infected millions of systems, turning poorly secured IoT devices—such as TV streaming boxes, digital picture frames, and routers—into relays for malicious traffic and abnormally large distributed denial‑of‑service (DDoS) attacks.
Reference: Krebs on Security – “DDOS botnet Aisuru blankets US ISPs in record DDoS”
What is I2P?
I2P is a decentralized, privacy‑focused network that allows people to communicate and share information anonymously.
“It works by routing data through multiple encrypted layers across volunteer‑operated nodes, hiding both the sender’s and receiver’s locations,” the I2P website explains. “The result is a secure, censorship‑resistant network designed for private websites, messaging, and data sharing.”
Timeline of Disruptions
-
February 3 – I2P users began complaining on the organization’s GitHub page about tens of thousands of routers suddenly overwhelming the network, preventing existing users from communicating with legitimate nodes.
Source: GitHub issue comment
-
Users reported a rapidly increasing number of new routers joining the network that were unable to transmit data, overwhelming the network to the point where users could no longer connect.
-
One user asked whether the network was under attack; another replied, “Looks like it. My physical router freezes when the number of connections exceeds 60,000.”
-
Same day – The individuals controlling Kimwolf posted to their Discord channel that they had accidentally disrupted I2P after attempting to join 700,000 Kimwolf‑infected bots as nodes on the network.
Source: Krebs on Security – “Who benefited from the Aisuru and Kimwolf botnets?”
Evidence (Images)
| Description | Image |
|---|---|
| I2P users complaining about service disruptions from a rapidly increasing number of routers suddenly swamping the network. | 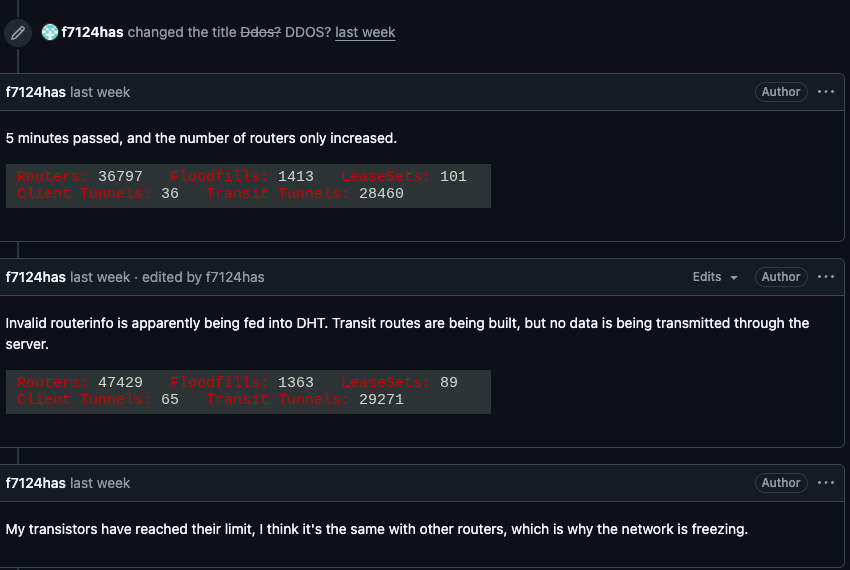 |
| A graph shared by I2P developers showing a marked drop in successful connections on the I2P network around the time the Kimwolf botnet started trying to use the network for fallback communications. | 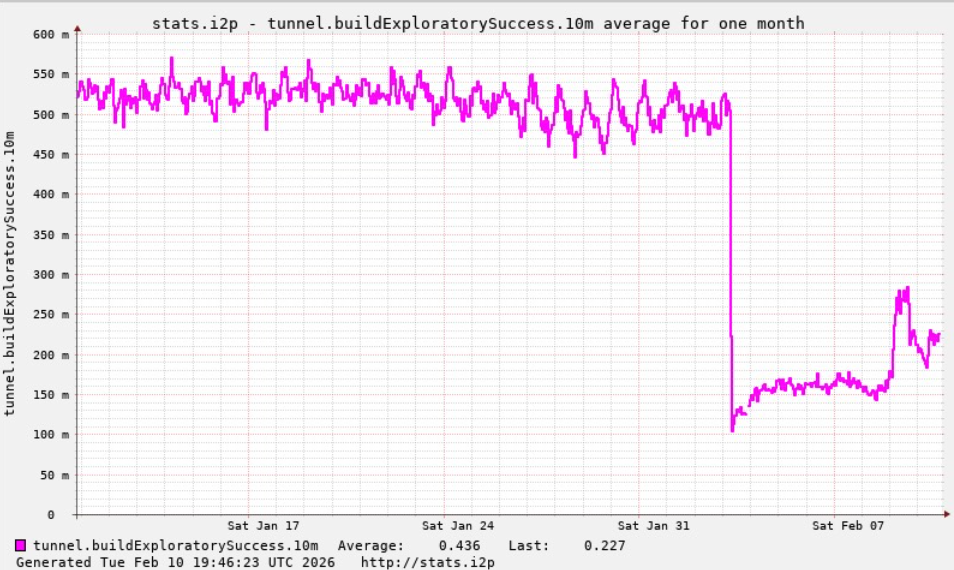 |
| The Kimwolf botmaster openly discusses what they are doing with the botnet in a Discord channel with my name on it. | 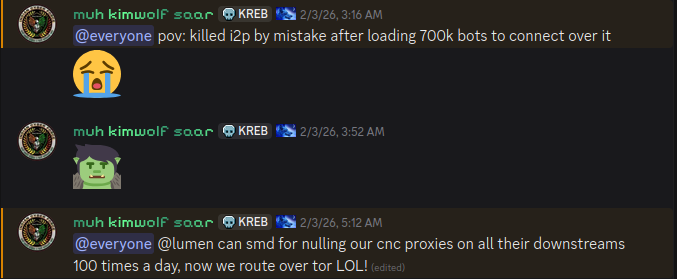 |
| An I2P user posted this graph on Feb. 10, showing tens of thousands of routers—mostly from the United States—suddenly attempting to join the network. | 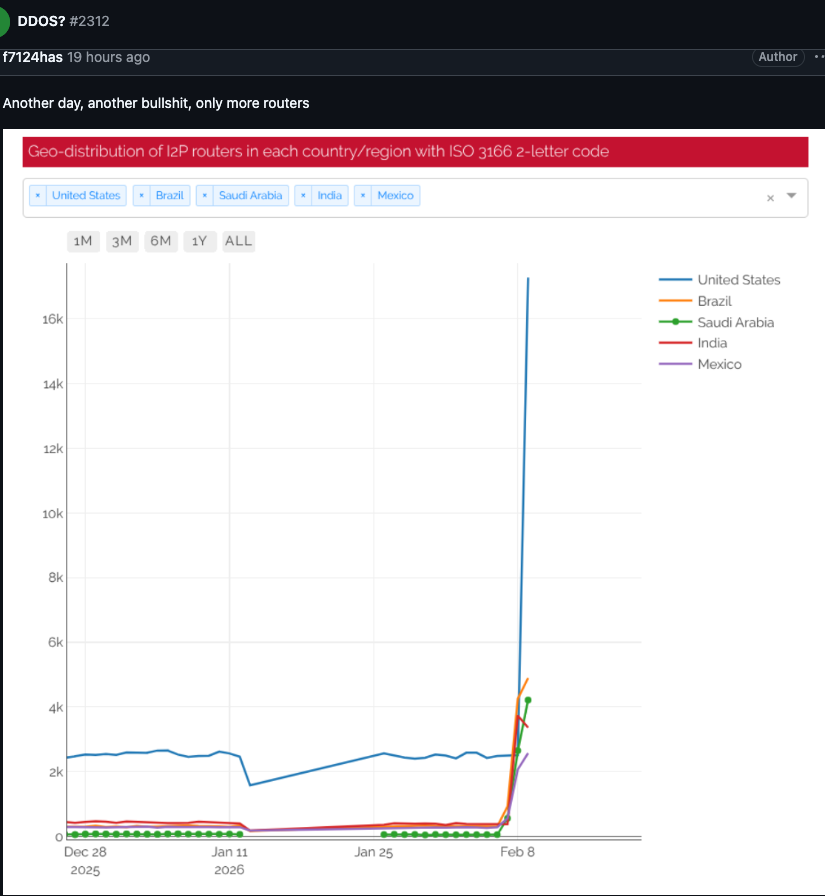 |
Expert Commentary
Lance James – Founder, Unit 221B & Original I2P Founder
-
Network size: While Wikipedia lists roughly 55,000 computers in the I2P network, James says the actual active count is 15,000–20,000 devices on any given day.
-
Current status: “The I2P network is still operating at about half of its normal capacity, and a new release is rolling out which should bring stability improvements over the next week for users.”
Source: Unit 221B website
Benjamin Brundage – Founder, Synthient
-
Botnet strategy: Kimwolf operators are trying to build a command‑and‑control (C2) network that can’t easily be taken down by coordinated security efforts.
-
Use of anonymity networks: They have been experimenting with I2P and a similar anonymity network—Tor—as a backup C2 channel, though there have been no recent widespread disruptions in Tor.
-
Goal: “I don’t think their goal is to take I2P down. It’s more they’re looking for an alternative to keep the botnet stable in the face of takedown attempts.”
Source: Synthient website
Impact on Other Services
-
Cloudflare: Late last year, Kimwolf instructed millions of infected devices to use Cloudflare’s DNS settings, causing Kimwolf‑associated control domains to repeatedly usurp Amazon, Apple, Google, and Microsoft in Cloudflare’s public ranking of the most frequently requested websites.
Reference: Krebs on Security – “Cloudflare scrubs Aisuru botnet from top domains list”
Future Outlook
-
I2P: A software update is expected to restore roughly 50 % of the network’s capacity within the next week.
-
Kimwolf: According to Brundage, recent internal conflicts have alienated some of the botnet’s more competent developers and operators, which may reduce the botnet’s effectiveness in the near term.
All links and images are sourced from publicly available reports, primarily KrebsOnSecurity.
Rookie mistake this past week caused the botnet’s overall numbers to drop by more than 600,000 infected systems.
“It seems like they’re just testing stuff, like running experiments in production,” he said.
“But the botnet’s numbers are dropping significantly now, and they don’t seem to know what they’re doing.”