ICE Masks Up in More Ways Than One
Source: Hacker News
[](https://substackcdn.com/image/fetch/$s_!DstW!,f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2F0490365d-60b5-4b38-9766-19b327a43832_1149x766.webp)
**Homeland security is increasing the use of undercover techniques to infiltrate and interact with social media users in order to collect intelligence and target individuals, documents leaked to me reveal.**
The new program, called **“masked engagement,”** allows Homeland Security officers to assume false identities and interact with users—friending them, joining closed groups, and gaining access to otherwise private postings, photographs, friend lists, and more.
A senior Department of Homeland Security (DHS) official tells me that **over 6,500 field agents and intelligence operatives** can use the new tool, a significant increase explicitly linked to more intense monitoring of American citizens.
---
### Background: Existing OSINT Practices
For years, DHS has been conducting what it calls **“Open Source Intelligence” (OSINT)** collection, using social media to enhance general *operational awareness* and to investigate targets in criminal, civil, or administrative contexts. Each DHS component defines the level of use, which were previously limited to the following practices (defined below):
- **“overt engagement”**
- **“overt research”**
- **“overt monitoring”**
- **“masked monitoring”**
- **“undercover engagement”**
**Masked monitoring** allows officers at agencies like ICE and Border Patrol to use alias accounts to *passively* observe public online activity. Crucially, this level of monitoring bars DHS representatives from interacting with other users directly. Under masked monitoring, officers are **not allowed** to:
- Ask an admin for entry into a private group, or
- “Friend” a target to see non‑public posts.
---
### The New “Masked Engagement” Policy
With **masked engagement** (separate from masked monitoring), that firewall has now been dismantled. The only restriction imposed on masked engagement is that DHS officers **not exceed the threshold of “substantive engagement”**—a term the rules leave conveniently ill‑defined.
The new practice allows a federal government employee or contractor to use **fake identities or credentials that conceal their official affiliation**. It is a step down from **“undercover engagement,”** a highly controlled status that is only allowed on a limited and intermittent basis.
You can compare the old vs. new DHS policies in the two screenshots below.
---
#### Old DHS Policy
[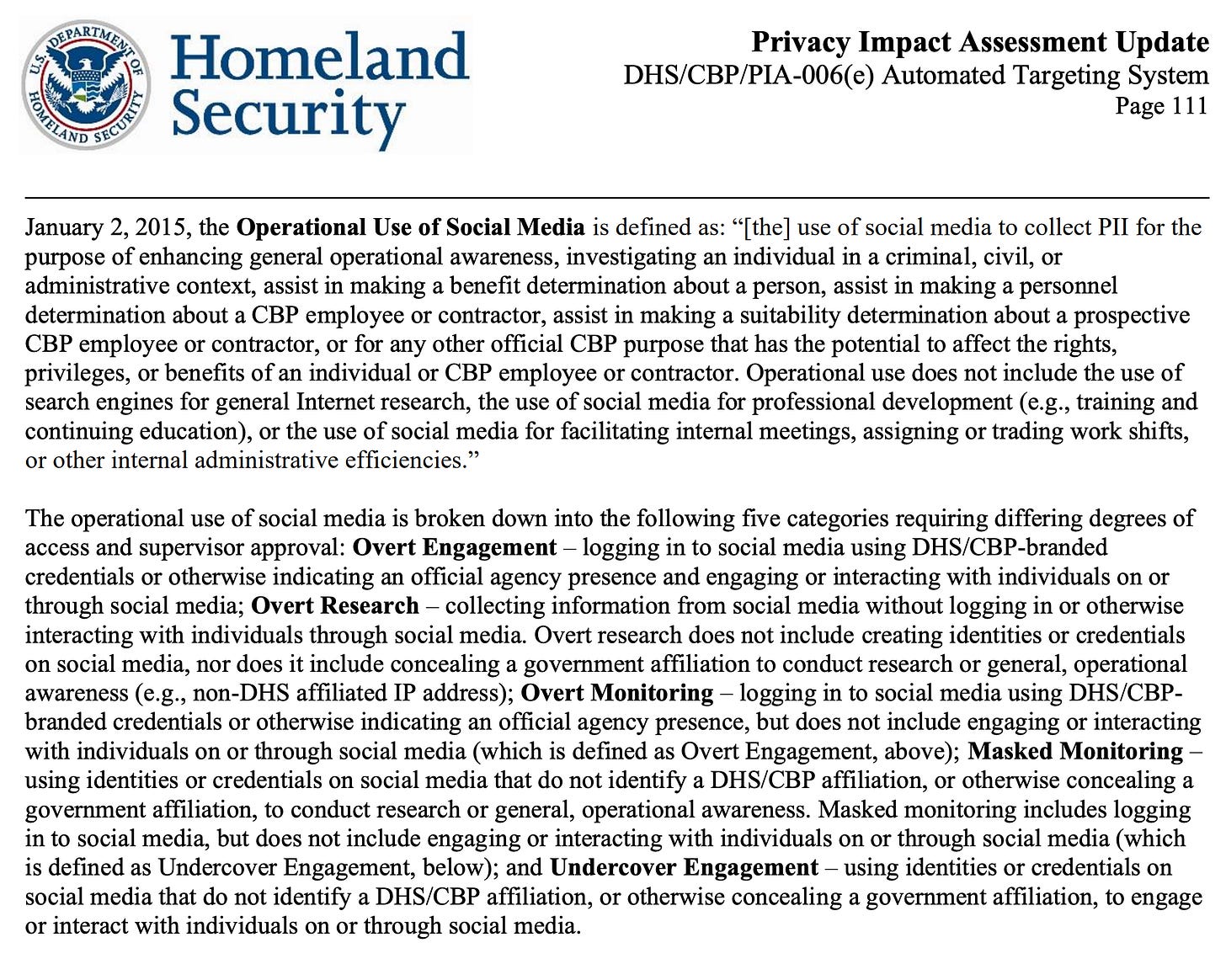](https://substackcdn.com/image/fetch/$s_!o2St!,f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2F1b1c5b4f-26c8-48c5-b656-bfc0cfaacb92_2164x1730.png)
*Screenshot of old DHS policy*
---
#### New DHS “Masked Engagement” Policy (Leaked)
[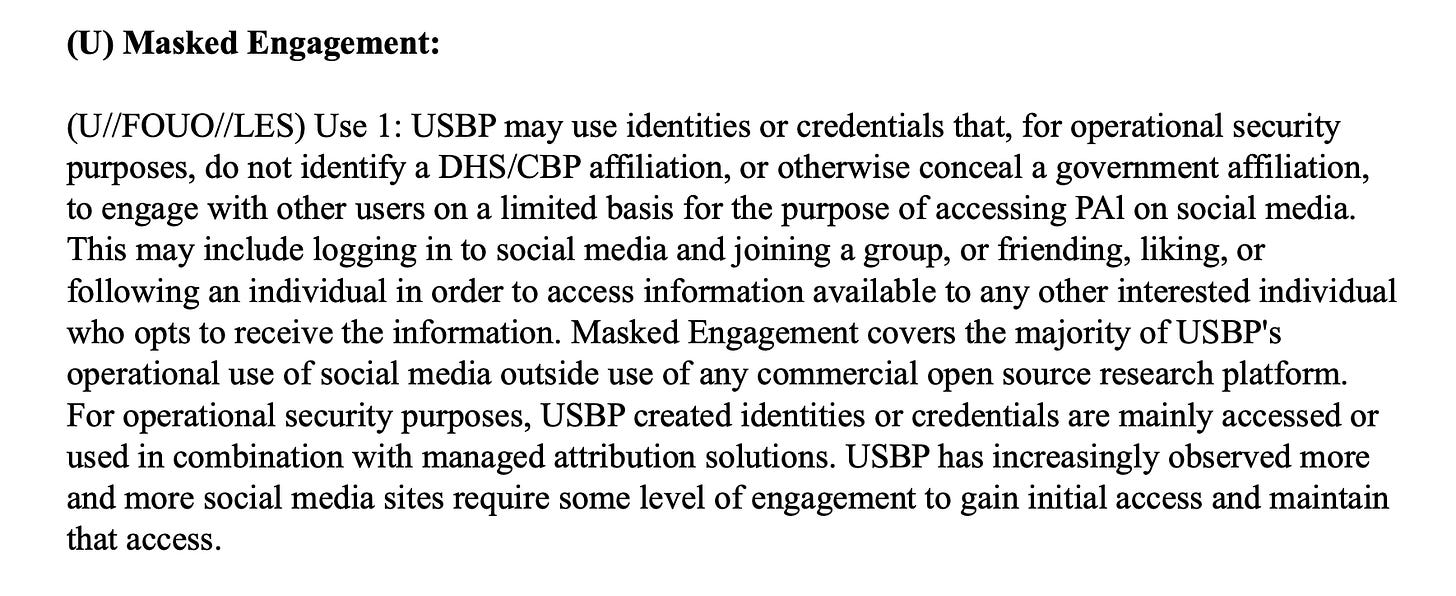](https://substackcdn.com/image/fetch/$s_!H5pk!,f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2Fbe7e7493-0e40-4b9a-a9d5-84f769fc2535_1770x724.png)
*Leaked copy of new DHS “Masked Engagement” policy*
---
### Official Language from CBP
A Customs and Border Protection (CBP) document I obtained, titled **“Component Plan for Operational Use of Social Media,”** defines the shift:
> “The Operational Use of Social Media using identities or credentials that… conceal a government affiliation, to engage with other users on a limited basis for the purpose of accessing **Publicly Available Information**… For example, Masked Engagement would include logging in to social media and joining a group, or friending, liking, or following an individual.”
By labeling this a **“middle ground”** between monitoring and full‑blown undercover work, DHS allows agents to infiltrate private digital spaces **without the rigorous internal approvals and legal checks required for a formal undercover “sting.”**
---
### Expert Commentary
> “CBP’s expansion into what they’re calling ‘masked engagement’ is cause for real concern,”
> — *Rachel Levinson‑Waldman, Director of the Brennan Center’s Liberty and National Security Program* (comment to me)
Levinson‑Waldman added:
> “This new capability is being shoehorned in one step below undercover engagement (which already allows for a lot of overreach). It appears CBP believes that friending someone, following them, or joining a group is not as invasive as directly engaging or interacting with individuals.”
She called the policy **“insidious”** because it might seem to the federal government that it is not particularly invasive, yet it could yield huge amounts of information about a person’s social network and preferences. All of this would happen **imperceptibly** to anyone in a group chat, unaware that the information is even being shared.
> “In addition, doing so through an alias account—an account that doesn’t reveal the user’s CBP affiliation, and pretends to be someone else—will weaken trust in government and weaken the trust that is critical to building community both online and off,” she added.
---
### DHS Response
When I pressed the DHS spokesperson for specifics—such as **when masked engagement was first adopted** and **how it defines the restriction on “substantive engagement”**—they retreated into the administration’s usual swaggering non‑response.
> “DHS has utilized its Congressionally directed undercover authorities to root out child molesters and predators for years,” the DHS spokesperson (no name included—fitting, I suppose, for a story about masking) told me in an email.
> “We will continue us…”“We’re using every tool at our disposal to protect the American people as our agents and officers. Make America Safe Again.”
The “tools” they’re referring to are increasingly sophisticated. The document that first flagged “masked engagement” for me was produced by Silo, a cloud‑based web isolation platform created by Authentic8.
Silo is like a digital mask for federal agents operating on social media. It allows them to browse the web from an “air‑gapped” remote server, masking their government IP addresses and spoofing their hardware profiles. To a Facebook admin or a Signal group moderator, the federal agent appears as a local user with a standard smartphone. This technical capability, called “managed attribution,” ensures that while the agent is “engaging” with you, the government’s digital footprint is completely invisible.
According to documents I’ve reviewed, Homeland Security is using other commercial and proprietary apps and software to conduct managed‑attribution monitoring, with codenames like GOST, Shadow Dragon, Gecko, Jemini, Axis, and Creepy—which has to be my favorite.
Creepy!
Sources tell me that DHS has already used masked engagement to infiltrate pro‑Palestinian groups in the U.S. and to build databases of potential transnational criminals among Mexican and Mexican‑American communities.
“Open‑source monitoring has become so ubiquitous that we even have databases of identities used by the department to track our own online engagements,” a senior DHS official told me.
“Yes, we have safeguards against violating people’s privacy, but masked engagement is just the first step in breaching people’s privacy settings in ways that they are not even aware of.”
— Edited by William M. Arkin
No posts