Google says 90 zero-days were exploited in attacks last year
Source: Bleeping Computer
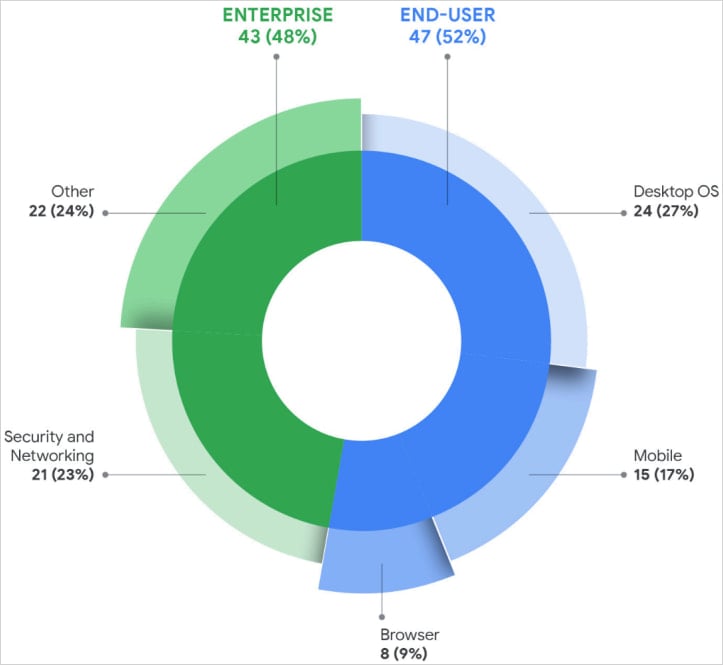
Google Threat Intelligence Group (GTIG) tracked 90 zero‑day vulnerabilities actively exploited throughout 2025, almost half of them in enterprise software and appliances.
The figure is a 15 % increase compared to 2024, when 78 zero‑days were exploited in the wild, but lower than the record 100 zero‑days tracked in 2023.
Zero‑day vulnerabilities are security issues in software products that attackers exploit, usually before the vendor learns about them and develops a patch. They are highly valued by threat actors because they often enable initial access, remote code execution, or privilege escalation.

Exploitation Statistics for 2025
- Total exploited zero‑days: 90
- Target breakdown: 47 targeted end‑user platforms, 43 targeted enterprise products
- Common flaw types: remote code execution, privilege escalation, injection and deserialization, authorization bypasses, memory‑corruption (use‑after‑free) bugs
- Memory‑safety issues: 35 % of all exploited zero‑days
The most targeted enterprise systems were security appliances, networking infrastructure, VPNs, and virtualization platforms, as these provide privileged network access and often lack EDR monitoring.
Operating System Exploits
- Desktop OSs: 24 zero‑days
- Mobile platforms: 15 zero‑days
Web Browser Exploits
- Zero‑day exploits in browsers dropped to eight, a sharp decline compared to previous years.
Source: Google
Most Targeted Vendors
- Microsoft: 25 zero‑days
- Google: 11 zero‑days
- Apple: 8 zero‑days
- Cisco: 4 zero‑days
- Fortinet: 4 zero‑days
- Ivanti: 3 zero‑days
- VMware: 3 zero‑days
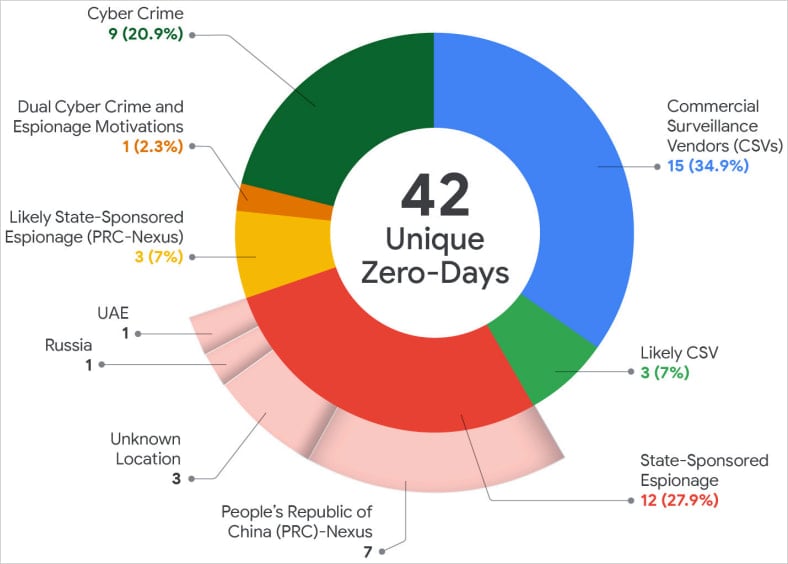
For the first time since Google began tracking zero‑day exploitation, commercial spyware vendors (CSVs) were the largest users of undocumented flaws, surpassing state‑sponsored espionage groups.
“This continues to reflect a trend we began to observe over the last several years—a growing proportion of zero‑day exploitation is conducted by CSVs and/or their customers, demonstrating a slow but sure movement in the landscape.” – GTIG report
Source: Google
Threat Actors
- State‑sponsored actors: China‑linked espionage groups remained the most active, exploiting 10 zero‑days in 2025, primarily against edge devices, security appliances, and networking equipment.
- Financially motivated actors: Ransomware and data‑extortion groups accounted for nine exploited zero‑days.
Outlook for 2026
GTIG believes that AI tools will help automate vulnerability discovery and accelerate exploit development, so exploitation of zero‑day flaws in 2026 is expected to remain high.
The report highlights the Brickstorm campaign as an example of hackers shifting focus from source‑code theft to discovering flaws in future software products.
Brickstorm campaign details
Recommendations
Google advises organizations to:
- Reduce attack surface and privilege exposure – limit unnecessary services and administrative rights.
- Continuously monitor for anomalous behavior – employ behavioral analytics and threat‑detection tools.
- Maintain rapid patching and incident‑response processes – prioritize zero‑day patches and have a clear response plan.