From Confusion to Clarity: My Journey Learning Social Media APIs & OAuth
Source: Dev.to
Step 1 — Research Before Code
Before writing a single line of code, I researched which platforms allow posting via API. I studied:
- LinkedIn API
- Instagram Graph API
- Facebook Graph API
- Twitter (X) API
Very quickly, I realized something important: social media platforms don’t just give you an API key and let you post. They require:
- Developer app registration
- OAuth authentication
- Permission scopes
- Strict security checks
It wasn’t just “call an API and done.” It was a full authentication system.
Step 2 — Understanding OAuth 2.0 (The Turning Point)
OAuth was something I had heard about before, but never implemented fully. I had to understand it deeply. Here’s what I learned:
- User clicks “Login with LinkedIn.”
- User is redirected to LinkedIn.
- LinkedIn returns an authorization code.
- The code is exchanged for an access token.
- The access token is used to call APIs.
Step 3 — Automating the Process
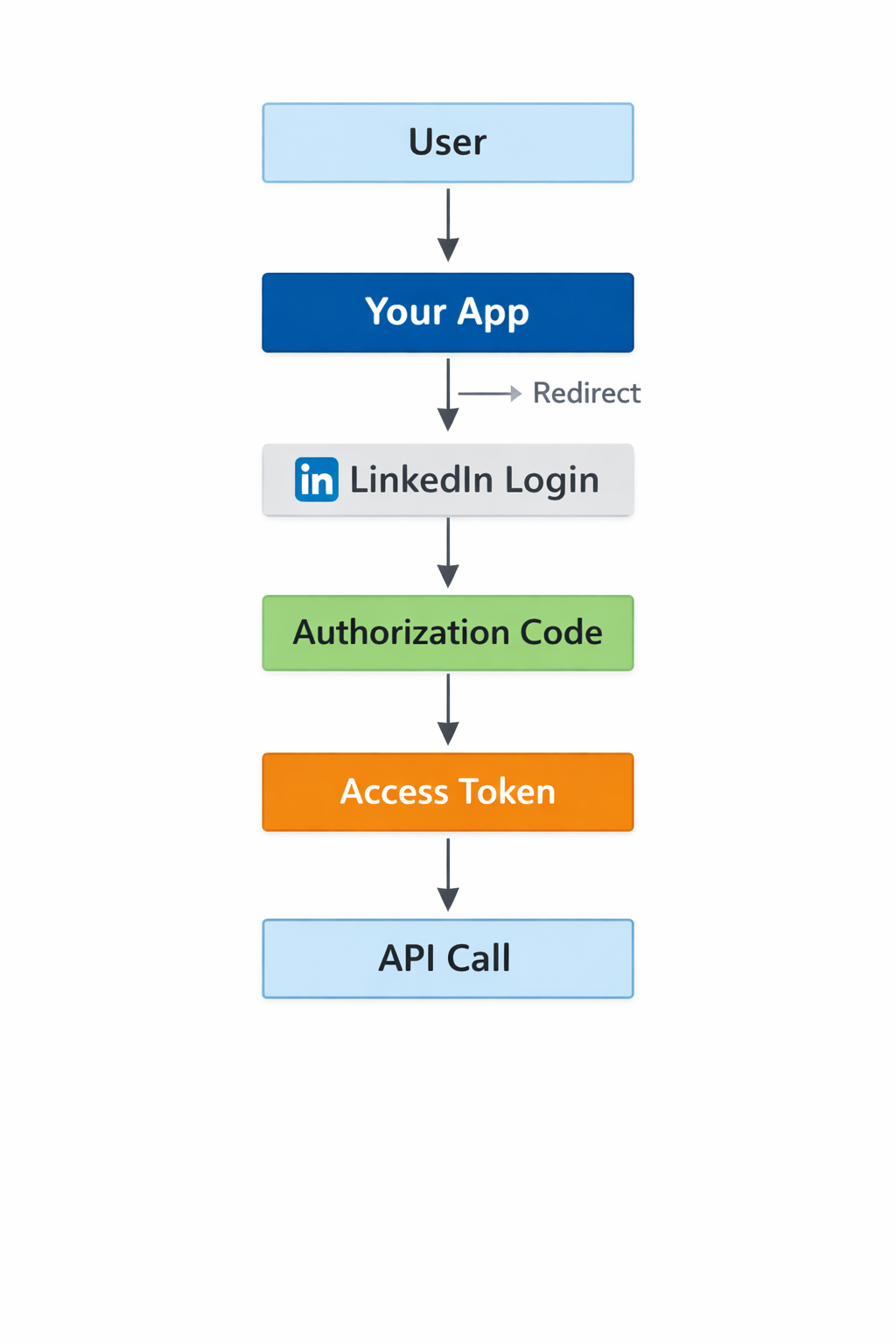
Understanding this flow changed everything. OAuth isn’t just login — it’s a secure permission exchange between systems.
Step 4 — Struggles During Learning
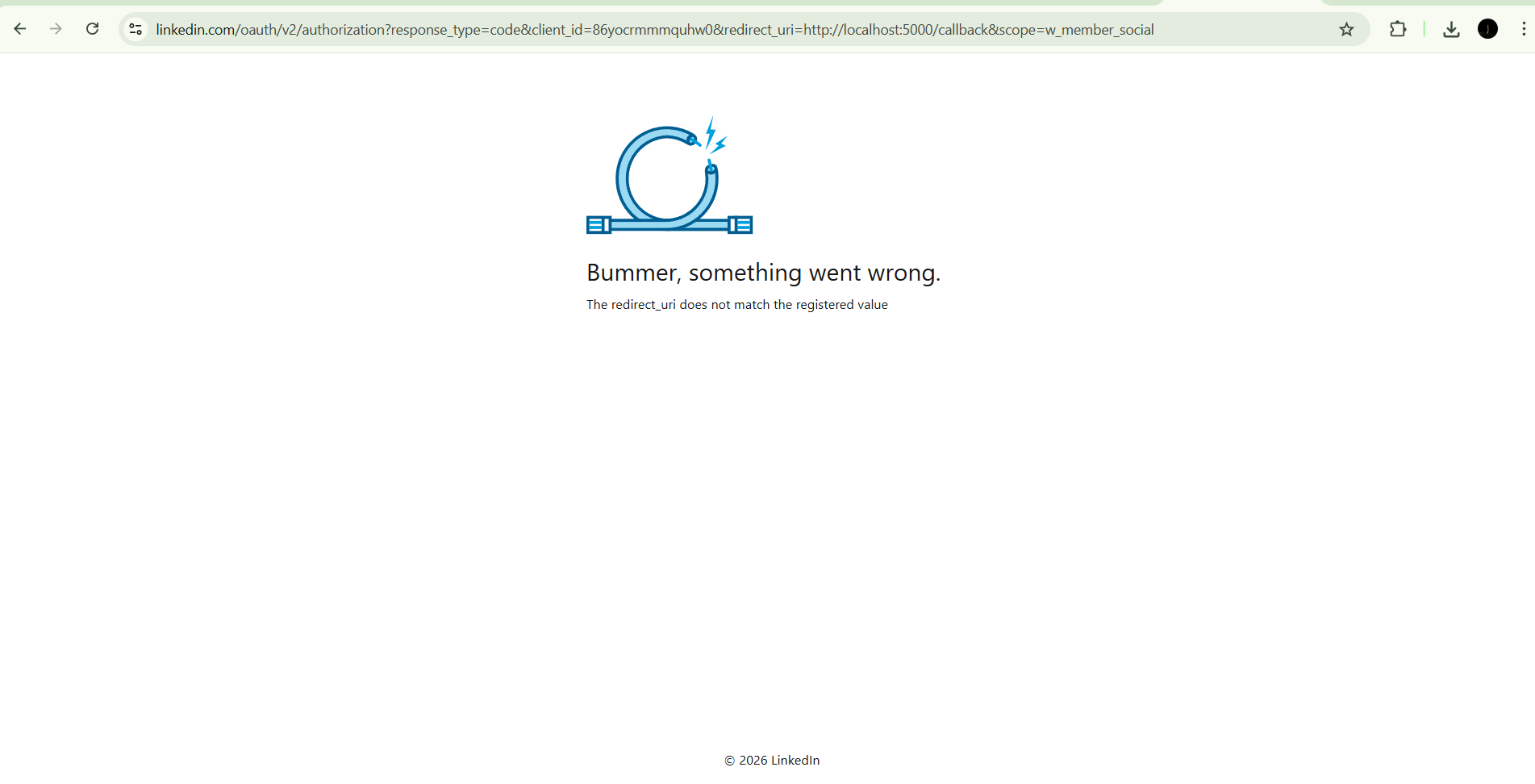
This phase was full of errors:
- Redirect URI mismatch
- Unauthorized scope errors
- 403 Access Denied
- Missing token
- Permission restrictions
At times it felt confusing, but each error forced me to:
- Read documentation carefully
- Understand HTTP requests
- Debug server logs
Learning how real APIs enforce security taught me that debugging often teaches more than tutorials.

Step 5 — Why I Chose LinkedIn
Among all platforms, LinkedIn felt structured and developer‑focused. It provides:
- UGC Post API
- Media upload support
- Clear OAuth documentation
So I decided to start my automation journey with LinkedIn, which led to the actual development phase.
Step 6 — What I Learned in This Phase
- How OAuth 2.0 works in real systems
- Why scopes and permissions matter
- How access tokens are generated and used
- How secure authentication differs from basic login
- How REST APIs communicate via JSON
This learning phase built my foundation. Only after understanding this clearly did I start building the actual application.