Europol-coordinated action disrupts Tycoon2FA phishing platform
Source: Bleeping Computer

Operation Overview
An international law‑enforcement operation coordinated by Europol disrupted Tycoon2FA, a major phishing‑as‑a‑service (PhaaS) platform linked to tens of millions of phishing messages each month. The technical disruption was led by Microsoft with support from a coalition of private partners, while seizure of infrastructure and other operational measures were carried out by law‑enforcement agencies in Latvia, Lithuania, Portugal, Poland, Spain, and the United Kingdom – all coordinated by Europol.
“The investigation began after intelligence was shared by Trend Micro. Europol disseminated this information through its EC3 Advisory Groups and operational networks, enabling a coordinated operational strategy to be developed.” – Europol
Impact
- 330 domains that formed the backbone of the criminal service (including control panels and phishing pages) were seized and taken offline.
- The operation was supported by Microsoft, Trend Micro, Cloudflare, Coinbase, Intel471, Proofpoint, Shadowserver Foundation, and SpyCloud.
Tycoon2FA had been active since at least August 2023 and was used by cybercriminals to bypass multi‑factor authentication (MFA) protections, compromising accounts belonging to nearly 100,000 organizations worldwide, including government institutions, schools, and healthcare organizations.
According to Microsoft, by mid‑2025 Tycoon2FA was generating tens of millions of phishing emails each month, accounting for more than 60 % of all blocked phishing attempts.
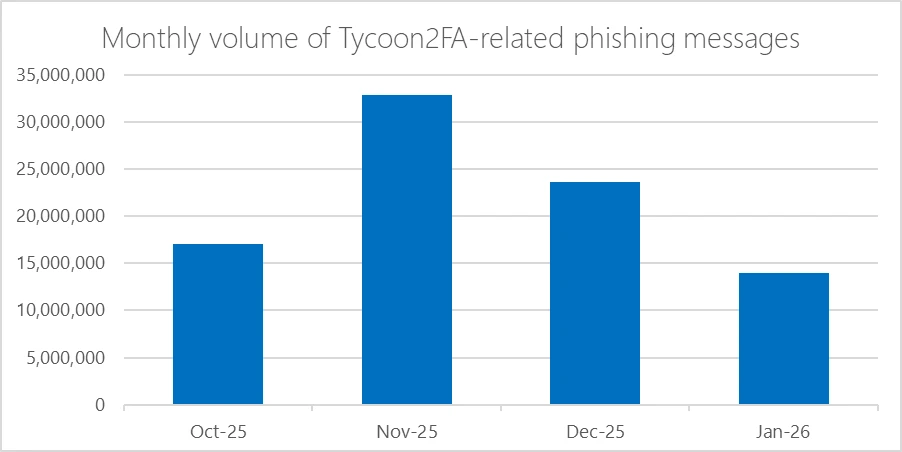 Tycoon2FA volume of phishing messages (Microsoft)
Tycoon2FA volume of phishing messages (Microsoft)
Platform Details
Tycoon2FA operated as an adversary‑in‑the‑middle (AiTM) platform, using a reverse‑proxy server to intercept victims’ login credentials and session cookies in real time. The service targeted Microsoft and Google customers, allowing attackers to:
- Hijack authenticated sessions and circumvent MFA protections while the login process appeared normal to the victim.
- Impersonate trusted brands by mimicking sign‑in pages for services such as Microsoft 365, OneDrive, Outlook, SharePoint, and Gmail.
- Establish persistence and access sensitive information even after passwords were reset, unless active sessions and tokens were explicitly revoked.
“Tycoon2FA’s platform enabled threat actors to impersonate trusted brands by mimicking sign‑in pages… It also allowed threat actors using its service to establish persistence and to access sensitive information even after passwords are reset, unless active sessions and tokens were explicitly revoked.” – Microsoft Security Blog
The attack flow worked by intercepting session cookies generated during authentication, simultaneously capturing user credentials, and relaying MFA codes through Tycoon2FA’s proxy servers to the legitimate service.
Pricing
Tycoon2FA was sold through Telegram for $120 for 10 days of access, lowering the barrier for low‑skilled criminals to launch sophisticated, MFA‑bypassing attacks at scale.