Critical SolarWinds Serv-U flaws offer root access to servers
Source: Bleeping Computer

SolarWinds has released security updates to patch four critical Serv‑U remote code execution vulnerabilities that could grant attackers root access to unpatched servers.
Serv‑U is the company’s self‑hosted Windows and Linux file‑transfer software that includes Managed File Transfer (MFT) and FTP server capabilities, enabling organizations to securely exchange files via FTP, FTPS, SFTP, and HTTP/S.
Patched vulnerabilities
- CVE‑2025‑40538 – The most severe flaw. It allows attackers with high privileges to gain root or admin permissions on vulnerable servers. SolarWinds described it as a broken access‑control issue that lets an attacker create a system admin user and execute arbitrary code as root via domain admin or group admin privileges.
- Two type‑confusion flaws.
- One Insecure Direct Object Reference (IDOR) vulnerability that can be exploited to gain code execution with root privileges.
All four flaws require the attacker to already have high privileges on the targeted server, limiting exploitation to scenarios where privilege‑escalation chains or previously stolen admin credentials are available.
Exposure and prevalence
- Shodan currently tracks over 12,000 Internet‑exposed Serv‑U servers.
- Shadowserver estimates the number to be less than 1,200.
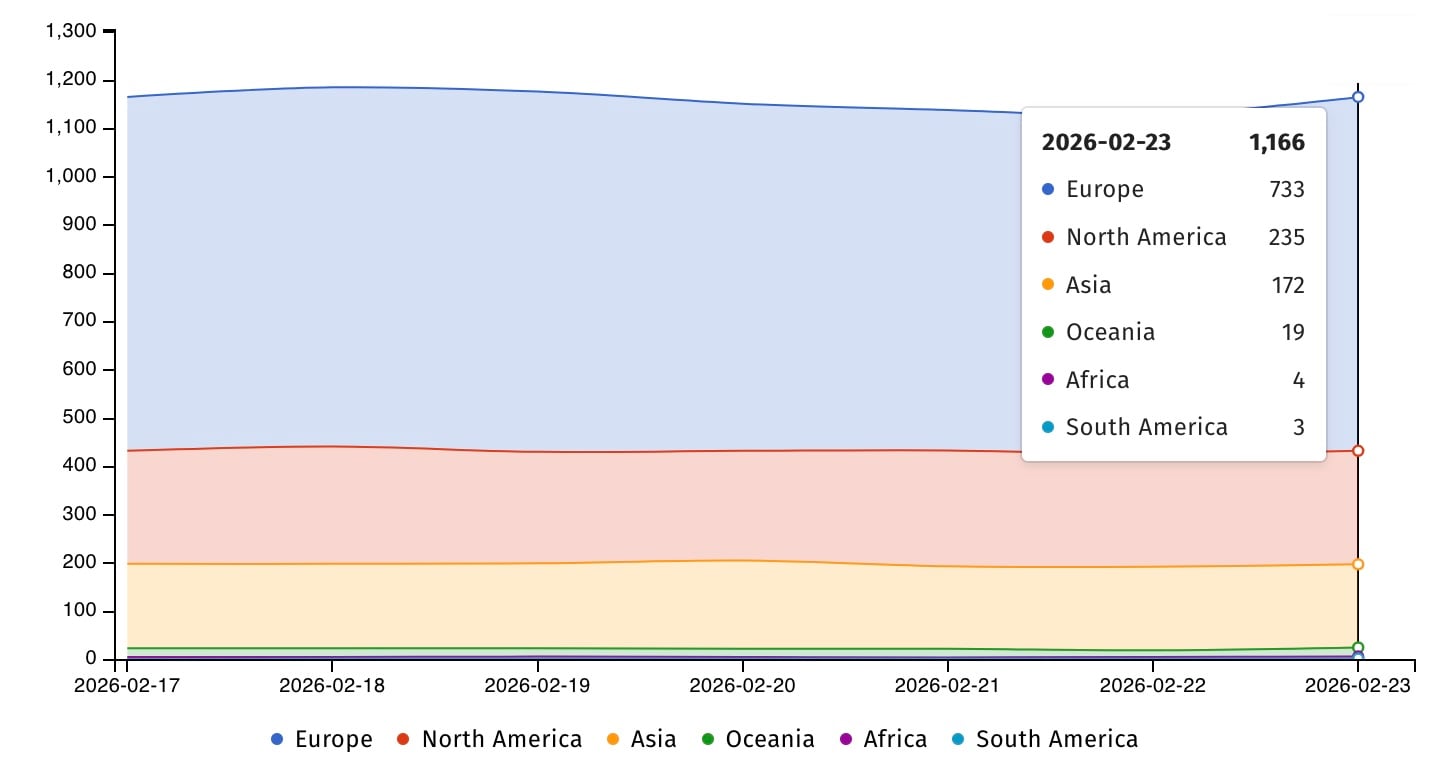 Serv‑U servers exposed online (Shadowserver)
Serv‑U servers exposed online (Shadowserver)
File‑transfer software like SolarWinds Serv‑U is often targeted because it provides easy access to documents that may contain sensitive corporate and customer data.
Historical exploitation
- CVE‑2021‑35211 – Exploited by the Clop gang in ransomware attacks, breaching corporate networks.
- CVE‑2021‑35211 – Also used by China‑based hackers (Microsoft’s DEV‑0322) in zero‑day attacks starting July 2021.
- CVE‑2024‑28995 – A path‑traversal vulnerability flagged in June 2024 as actively exploited, with publicly available proof‑of‑concept exploits.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) is tracking nine SolarWinds security flaws that have been or are still actively exploited in the wild.
References
- SolarWinds Serv‑U 15.5.4 release notes –
- Shodan search for “Serv‑U” –
- Shadowserver statistics –
- BleepingComputer article on Clop gang exploitation –
- Microsoft report on Chinese hackers using CVE‑2021‑35211 –
- BleepingComputer article on CVE‑2024‑28995 exploitation –
- CISA known‑exploited vulnerabilities catalog –