CISA: Recently patched RoundCube flaws now exploited in attacks
Source: Bleeping Computer
CISA flagged two Roundcube Webmail vulnerabilities as actively exploited in attacks and ordered U.S. federal agencies to patch them within three weeks.
Roundcube Webmail is a web‑based email client that has been the default mail interface for the widely used cPanel web hosting control panel since 2008.
The first vulnerability, actively abused by threat actors, is a critical remote code execution flaw tracked as CVE‑2025‑49113. It was first flagged as exploited days after it was patched in June 2025, when Internet security watchdog Shadowserver warned that over 84,000 vulnerable Roundcube installations were at risk.
Roundcube patched the second flaw (CVE‑2025‑68461) in December 2025. The vulnerability allows remote, unauthenticated attackers to exploit low‑complexity cross‑site scripting (XSS) attacks that abuse the animate tag in SVG documents.
“We strongly recommend updating all productive installations of Roundcube 1.6.x and 1.5.x with these new versions,” the Roundcube security team warned when releasing versions 1.6.12 and 1.5.12 that address the flaw.
Shodan currently tracks over 46,000 Roundcube instances accessible on the internet. However, there is no information on how many of them are vulnerable to CVE‑2025‑49113 or CVE‑2025‑68461 attacks.
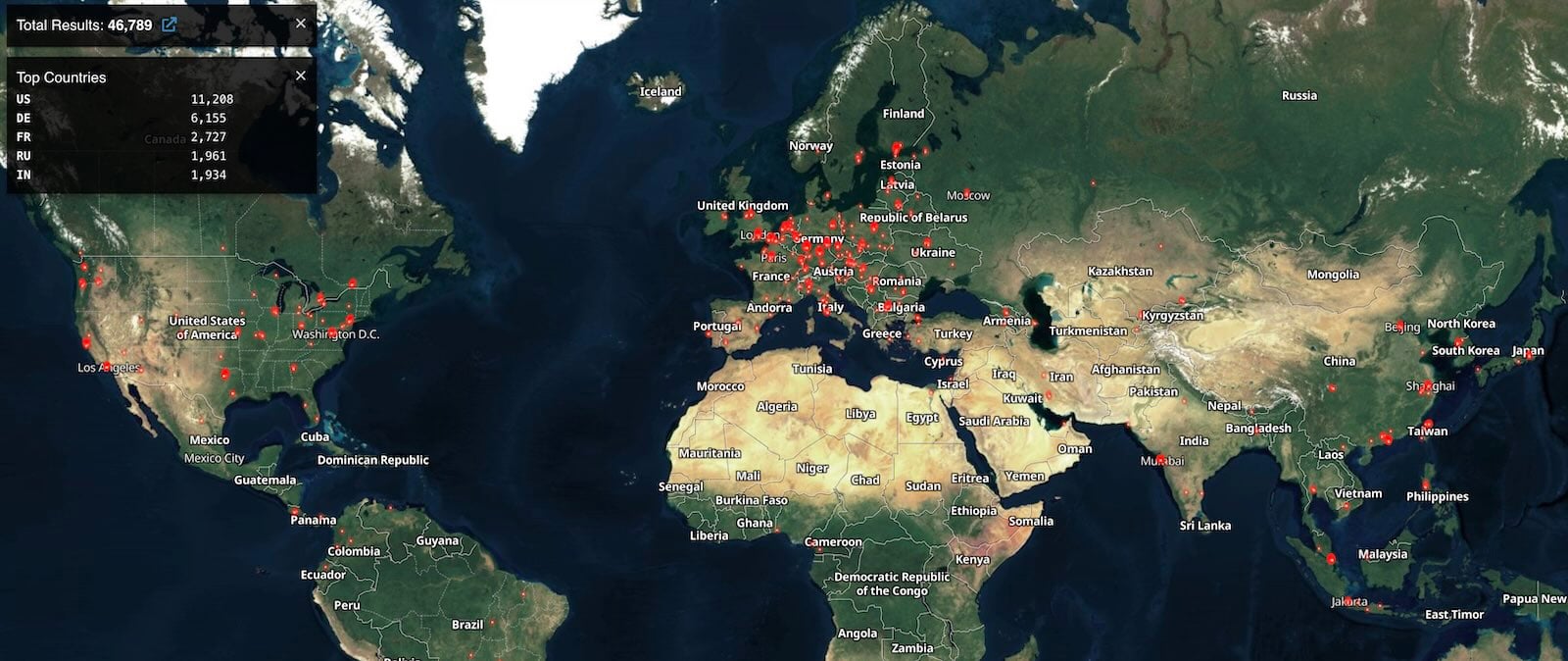 Roundcube instances online (Shodan)
Roundcube instances online (Shodan)
CISA added the two vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog on Friday, warning that they are “frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise.”
CISA also tracks ten other Roundcube Webmail vulnerabilities that are either actively exploited in attacks or have been abused in the past.
The U.S. cybersecurity agency has ordered Federal Civilian Executive Branch (FCEB) agencies to secure their systems against these bugs within three weeks, by March 13, as mandated by a binding operational directive (BOD 22‑01) issued in November 2021.
Roundcube vulnerabilities have been a popular target for cybercrime and state‑sponsored threat groups. The most recent example is a stored XSS vulnerability (CVE‑2023‑5631) exploited by the Winter Vivern (TA473) Russian hacking group in zero‑day attacks targeting European government entities and by the Russian APT28 cyber‑espionage group to breach Ukrainian government email systems.