Chinese cyberspies breached dozens of telecom firms, govt agencies
Source: Bleeping Computer
Overview
Google’s Threat Intelligence Group (GTIG), Mandiant, and partners disrupted a global espionage campaign attributed to a suspected Chinese threat actor that used SaaS API calls to hide malicious traffic in attacks targeting telecom and government networks.
The campaign has been active since at least 2023 and has impacted 53 organizations in 42 countries, with suspected infections in at least 20 additional countries.
The initial access vector is unknown, but researchers note that the threat actor—tracked internally by Google as UNC2814—has previously gained access by exploiting flaws in web servers and edge systems.
Impact
.jpg)
Source: Google
GRIDTIDE backdoor
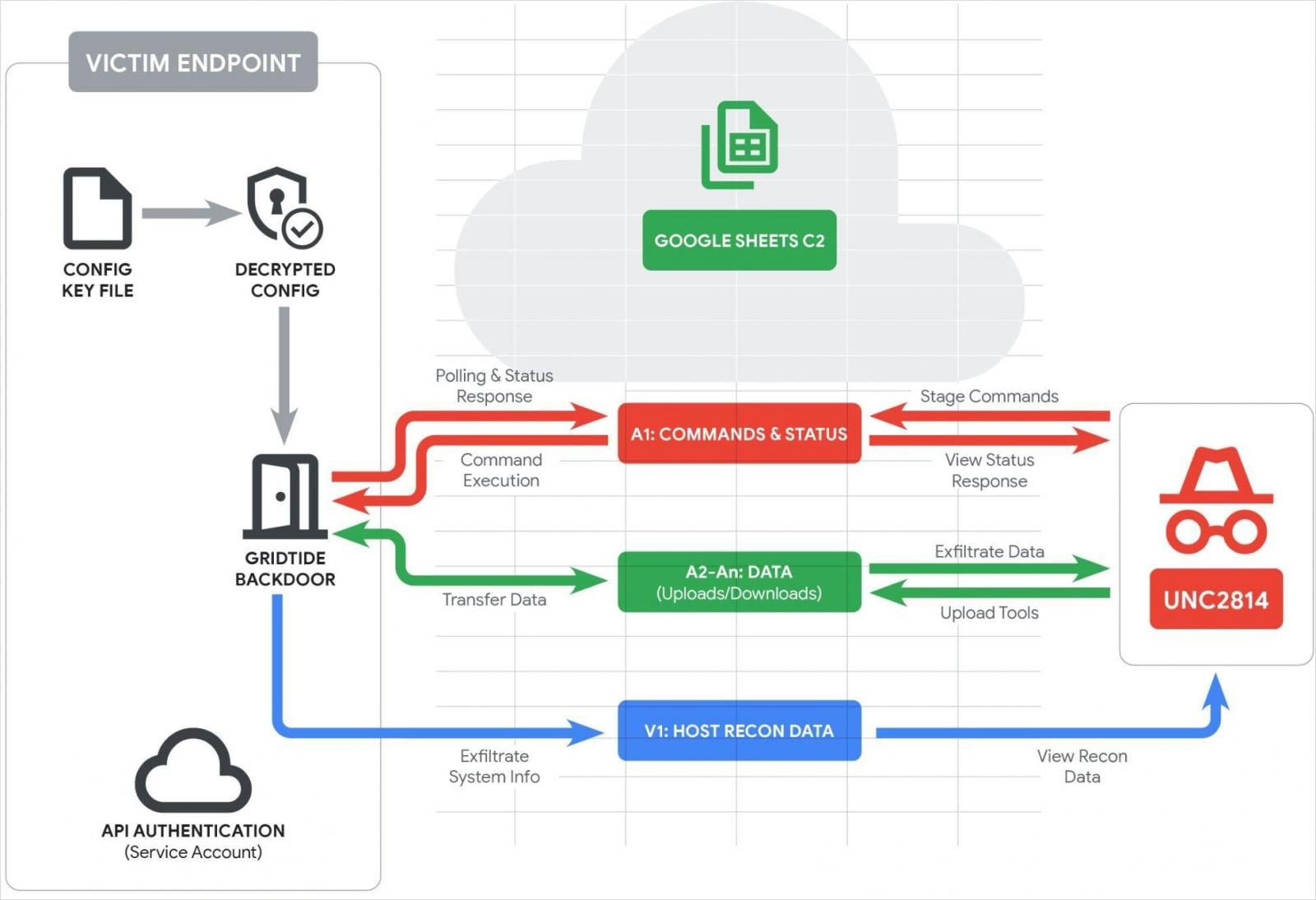
In the recently disrupted campaign, the actor deployed a new C‑based backdoor named GRIDTIDE, which abuses the Google Sheets API for evasive command‑and‑control (C2) operations.
- GRIDTIDE authenticates to a Google Service Account using a hard‑coded private key.
- Upon launch, it sanitizes the spreadsheet by deleting rows 1‑1000 and columns A‑Z.
- It then performs host reconnaissance, collecting the username, hostname, OS details, local IP, locale, and timezone, and logs the data in cell V1.
- Cell A1 serves as the command/status cell; GRIDTIDE polls it constantly for instructions.
If a command exists, the malware overwrites the cell with a status string. If empty, it retries every second for 120 times, then switches to random 5‑10‑minute checks to reduce noise.
Command set
| Command | Description |
|---|---|
| C | Execute Base64‑encoded Bash commands; write output to the sheet. |
| U | Upload: take data in A2:A and reconstruct/write a file at the encoded filepath “. |
| D | Download: read local file “ on the endpoint and send contents in ~45 KB fragments into A2:An. |
The A2‑An cells are used for writing command output, exfiltrated files, and uploading tools.
GRIDTIDE’s exchanges with the C2 rely on a URL‑safe Base64 encoding scheme that evades detection by web‑monitoring tools and blends with normal traffic.
Operational overview
Source: Google
In at least one case, Google confirmed that GRIDTIDE was deployed on a system containing sensitive personally identifiable information (PII). However, researchers did not directly observe data exfiltration.
Disruption and mitigation
Google, Mandiant, and partners took coordinated action to disrupt the campaign by:
- Terminating all Google Cloud projects controlled by UNC2814.
- Disabling known infrastructure and revoking Google Sheets API access.
- Sinkholing current and historical domains.
Organizations impacted by GRIDTIDE were notified directly, and support was offered to clean the infections.
Detection
Google has published detection rules and indicators of compromise (IoCs) at the bottom of their report.
Even though the disruption was comprehensive, Google expects UNC2814 to resume activity using new infrastructure in the near future.
Reference: Google blog post on disrupting GRIDTIDE