Checkmarx confirms LAPSUS$ hackers leaked its stolen GitHub data
Source: Bleeping Computer

Incident Overview
Application security company Checkmarx has confirmed that the LAPSUS$ threat group leaked data stolen from its private GitHub repository. The investigation is ongoing.
Attack Vector
Checkmarx believes the initial access vector was the Trivy supply‑chain attack attributed to the hacker group known as TeamPCP. The attack provided credentials from downstream users.
Using the stolen credentials obtained from the Trivy incident, the threat actor accessed Checkmarx’s GitHub repositories and published malicious code on March 23, 2026.
“As a result of that access, the attackers were able to interact with Checkmarx’s GitHub environment and subsequently publish malicious code to certain artifacts,” the company explains.
Source
Malicious Code Publication
On April 22, 2026, after a month of persistence, the attacker published malicious Docker images, VSCode, and Open VSX extensions for Checkmarx’s KICS security scanner. These artifacts were designed to steal credentials, keys, tokens, and configuration files.
Data Leak
In an update on April 26, 2026, Checkmarx confirmed that the data posted on the LAPSUS$ extortion portal originated from the March 23 compromise.
“Our investigation, conducted with support from a leading third‑party forensic firm, indicates that a cyber‑criminal group has published data related to Checkmarx to the dark web.”
Read the update
“Based on current evidence, we believe this data originated from Checkmarx’s GitHub repository, and that access to that repository was facilitated through the initial supply chain attack of March 23, 2026.”
While Checkmarx and other outlets reported the leak on the dark web, BleepingComputer found that LAPSUS$ also made the 96 GB data pack available through clearnet portals.
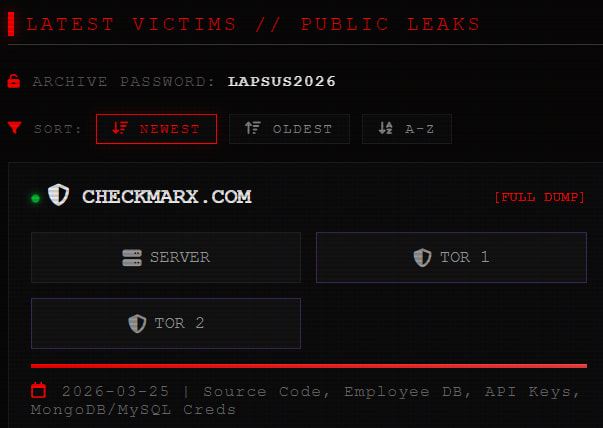 Checkmarx data leak on the LAPSUS$ site
Checkmarx data leak on the LAPSUS$ site
Source: BleepingComputer
BleepingComputer has not examined the content of the leaked data. Checkmarx assures that the repository does not contain customer information, as such data is not stored in its GitHub repository.
Response and Ongoing Investigation
- A forensic investigation is underway to determine the exact type of data exposed.
- If customer information is found, affected individuals will be notified immediately.
- Access to the compromised GitHub repository has been blocked pending the investigation.
- Checkmarx expects to share more details within the next 24 hours.