Bitwarden CLI npm package compromised to steal developer credentials
Source: Bleeping Computer

*Updated with further information from Bitwarden.*
## What happened?
The Bitwarden CLI was briefly compromised when attackers published a malicious `@bitwarden/cli` package to npm. The package contained a credential‑stealing payload that could spread to other projects.
- **Malicious version:** `2026.4.0`
- **Availability window:** 5:57 PM – 7:30 PM ET on **April 22, 2026**
- **Removal:** The package was taken down after the compromise was detected.
## Sources
- **Socket:** [Bitwarden CLI compromised](https://socket.dev/blog/bitwarden-cli-compromised)
- **JFrog:** [Bitwarden CLI hijack analysis](https://research.jfrog.com/post/bitwarden-cli-hijack/)
- **OX Security:** [Shai Hulud – Bitwarden CLI supply‑chain attack](https://www.ox.security/blog/shai-hulud-bitwarden-cli-supply-chain-attack/)
## Bitwarden’s response
> “The investigation found no evidence that end‑user vault data was accessed or at risk, or that production data or production systems were compromised. Once the issue was detected, compromised access was revoked, the malicious npm release was deprecated, and remediation steps were initiated immediately.”
> — *Bitwarden statement* ([source](https://community.bitwarden.com/t/bitwarden-statement-on-checkmarx-supply-chain-incident/96127))
Key points from the statement:
- The breach affected **only the npm distribution channel** for the CLI package.
- Only users who downloaded the malicious version were impacted.
- No vault data or production systems were compromised.
- Compromised access was revoked and the malicious release was deprecated.
## Additional note
[](https://www.adaptivesecurity.com/demo/security-awareness-training?utm_source=display_network&utm_medium=paid_display&utm_campaign=2026_04_display_bleepingcomputer&utm_id=701Rd00000fE8REIA0&utm_content=970x250)
*Bitwarden has taken steps to prevent future supply‑chain attacks and is monitoring its distribution channels closely.*The Bitwarden Supply‑Chain Attack
Source: Socket, JFrog, OX Security, BleepingComputer
Overview
Threat actors compromised a GitHub Action in Bitwarden’s CI/CD pipeline and injected malicious code into the Bitwarden CLI npm package.
- Modified package: The
preinstallscript and the CLI entry point were altered to use a custom loader namedbw_setup.js. - Loader behavior:
- Checks for the Bun runtime; if absent, it downloads Bun.
- Uses Bun to launch an obfuscated JavaScript file
bw1.js, which is credential‑stealing malware.
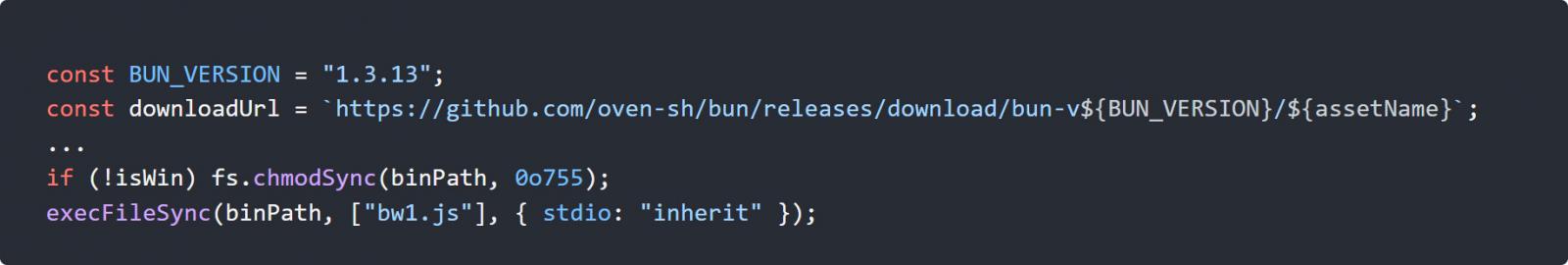
Figure 1 – Loader executing the malicious bw1.js file (JFrog)
Malware Capabilities
| Capability | Description |
|---|---|
| Credential theft | Harvests npm tokens, GitHub authentication tokens, SSH keys, and cloud credentials for AWS, Azure, and Google Cloud. |
| Encryption & exfiltration | Encrypts data with AES‑256‑GCM and exfiltrates it by creating public GitHub repositories under the victim’s account, storing the encrypted payload there. |
| Self‑propagation | Uses stolen npm credentials to locate packages the victim can modify and injects them with malicious code. |
| Targeted environment | Primarily CI/CD pipelines; the payload also attempts to harvest reusable secrets for further expansion. |
The exfiltrated repositories contain the string “Shai‑Hulud: The Third Coming”, a reference to earlier npm supply‑chain attacks.
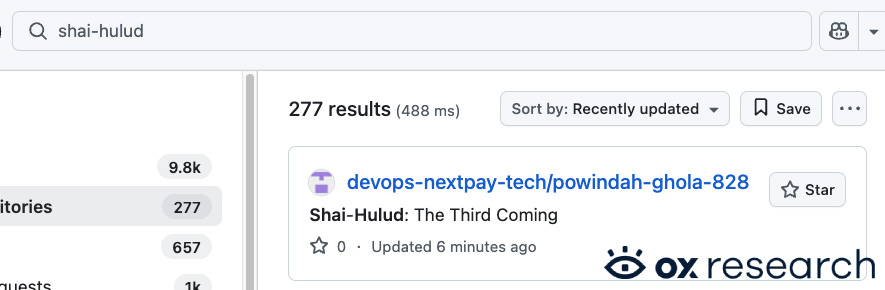
Figure 2 – Exfiltration repository (OX Security)
Connection to the Checkmarx Incident
- Bitwarden confirmed the breach was linked to the Checkmarx supply‑chain attack that affected its KICS Docker images, GitHub Actions, and developer extensions.
- Overlapping indicators include:
- Use of the same
audit.checkmarx[.]cx/v1/telemetryendpoint. - Identical
__decodeScrambledobfuscation routine with seed0x3039. - Similar gzip + base64‑encoded components for credential collection and downstream abuse.
- Use of the same
“The connection is at the malware and infrastructure level… The Bitwarden payload contains the same kind of embedded gzip+base64 components we saw in the earlier malware, including tooling for credential collection and downstream abuse.” – Socket
Both campaigns have been attributed to the threat actor TeamPCP, previously responsible for supply‑chain attacks on Trivy and LiteLLM.
Impact & Recommendations
- Compromise scope: Any system that installed the affected Bitwarden CLI version should be considered compromised.
- Immediate actions:
- Rotate all credentials – especially npm tokens, GitHub tokens, SSH keys, and cloud provider keys.
- Revoke and re‑issue any secrets that may have been exposed.
- Audit CI/CD pipelines for unauthorized changes or unknown GitHub repositories.
- Update to the patched Bitwarden CLI version as soon as it is released.
Updates
- 4/23/26 – Bitwarden confirmed the incident was directly linked to the Checkmarx supply‑chain attack.
References
- Socket – Bitwarden supply‑chain attack analysis
- JFrog – Malware analysis of
bw1.js - OX Security – Data exfiltration details
- BleepingComputer – Full story and timeline
- Checkmarx breach details
- TeamPCP’s previous attacks on Trivy and LiteLLM
The promotional content that appeared at the end of the original article has been removed for clarity.