Apple account change alerts abused to send phishing emails
Source: Bleeping Computer

Overview
Apple account change notifications are being abused to send fake iPhone purchase phishing scams within legitimate emails sent from Apple’s servers. The added legitimacy helps the messages bypass spam filters and increases the likelihood that recipients will fall for the scam.
A reader shared an email that appeared to be a standard Apple security notification stating that their account information had been updated. Embedded within the message was a phishing lure claiming an $899 iPhone purchase had been made via PayPal, along with a phone number to call to cancel the transaction.
“Dear User 899 USD iPhone Purchase Via Pay‑Pal To Cancel 18023530761,” reads the phishing email.
“The following changes to your Apple Account, hxfedna24005@icloud.com, were made on April 14, 2026 at 7:01:40 PM GMT:”
“Shipping Information”
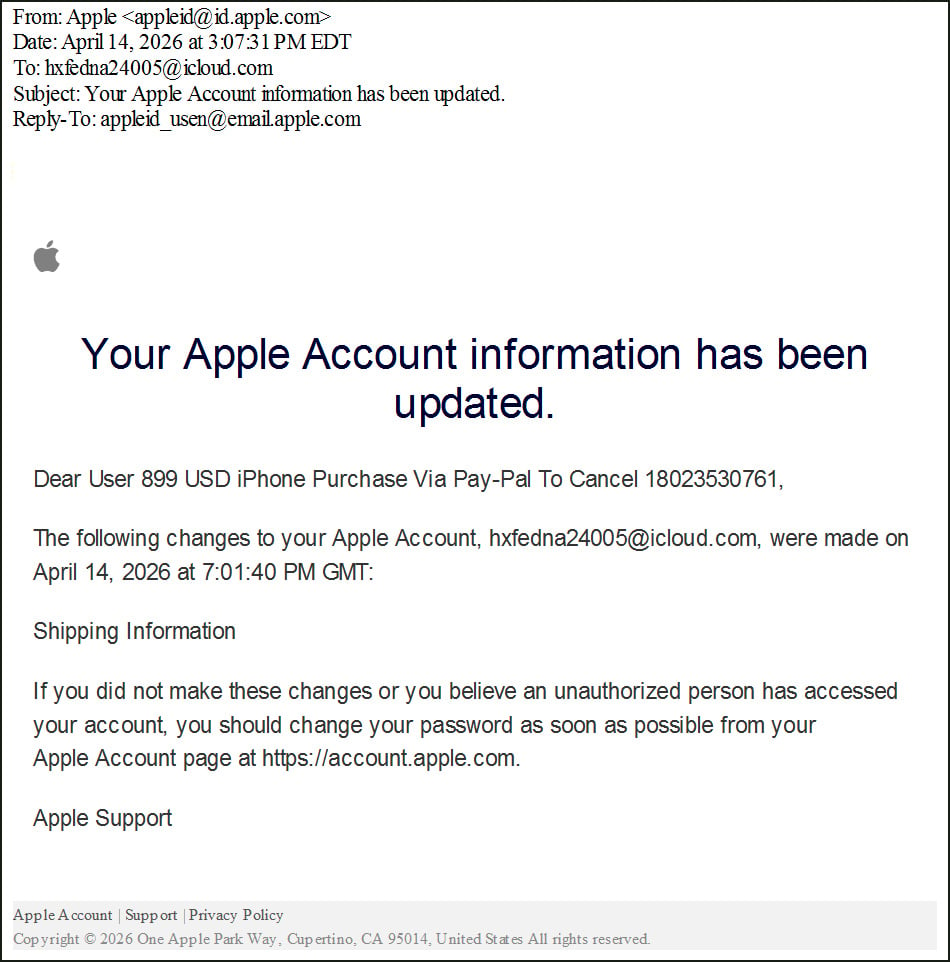
Callback phishing email abusing Apple Account change notifications
Source: BleepingComputer
These emails are designed to trick recipients into thinking their accounts were used for fraudulent purchases and to scare them into calling the scammer’s “support” number. When victims call, scammers often try to convince them that their accounts have been compromised and may instruct them to install remote‑access software or provide financial information. In previous callback‑phishing campaigns, such remote access has been used to steal funds, deploy malware, or exfiltrate data.
Abusing Apple account notifications
While the phishing lure itself is not new, the campaign shows how threat actors continue to evolve tactics by exploiting legitimate Apple services.
- The phishing email was sent from Apple’s infrastructure using the address appleid@id.apple.com.
- It passed SPF, DKIM, and DMARC checks, indicating it was a legitimate Apple‑signed message.
dkim=pass header.d=id.apple.com header.i=@id.apple.com header.b=o3ICBLWN
spf=pass (spf.icloud.com: domain of uatdsasadmin@email.apple.com designates 17.111.110.47 as permitted sender) smtp.mailfrom=uatdsasadmin@email.apple.comHeader analysis confirms the message originated from Apple mail servers and was not spoofed:
Initial server: rn2-txn-msbadger01107.apple.com
Outbound relay: outbound.mr.icloud.com
IP address: 17.111.110.47 (Apple‑owned)Attack workflow
- Create an Apple ID – The attacker registers a new Apple account.
- Inject phishing text – The scam message is split across the first name and last name fields of the account profile, because each field cannot hold the entire text.
- Modify shipping information – Changing the shipping details triggers Apple’s “account profile change” notification.
- Deliver the malicious alert – Apple includes the user‑supplied first and last name fields in the notification email, embedding the phishing lure directly into a legitimate‑looking alert.
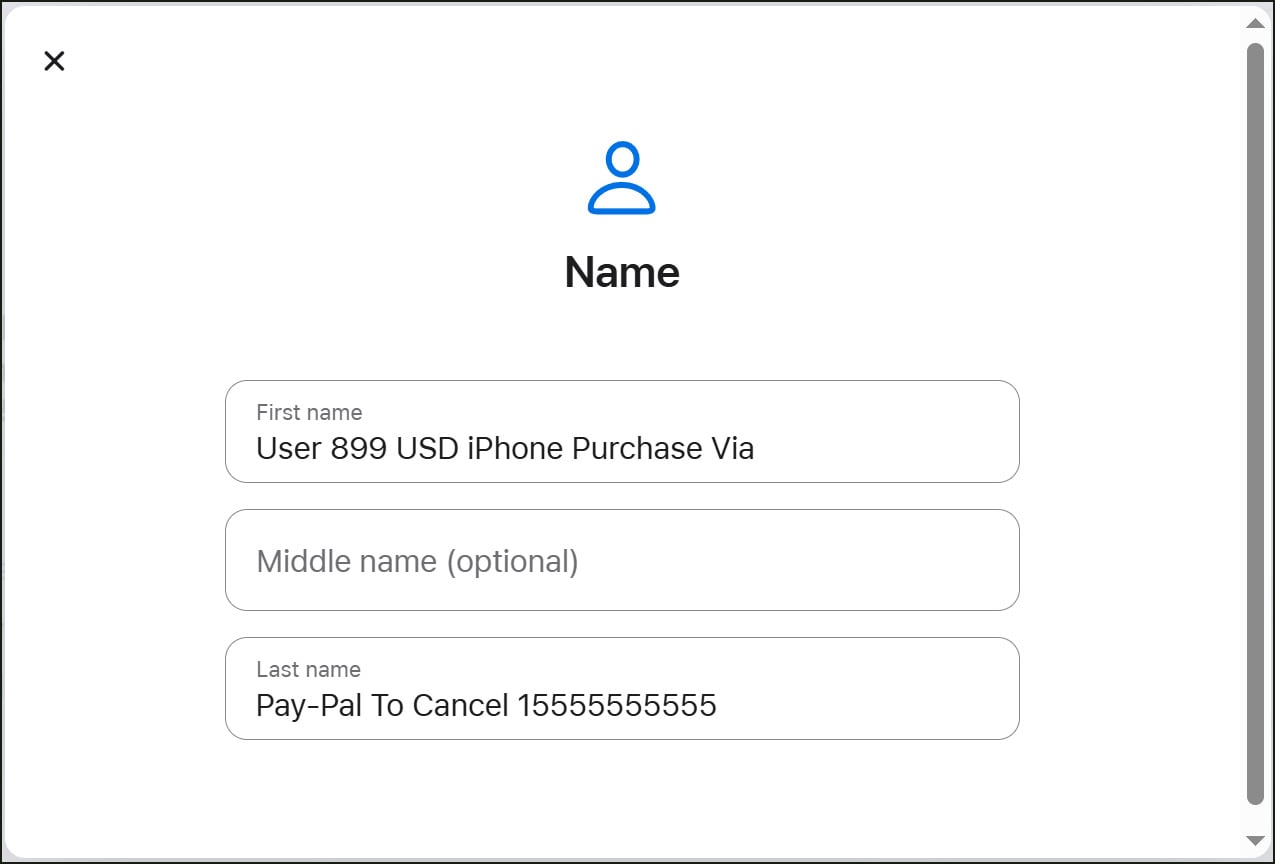
Replication attack by changing Apple account name fields
Source: BleepingComputer
The attacker can then send the notification to multiple targets, often using a mailing list. The original recipient differs from the final delivery address, indicating a distribution mechanism beyond a single victim.
Related abuse
A similar campaign previously abused iCloud Calendar invites to send fake purchase notifications through Apple’s servers. See the earlier report for details: iCloud Calendar abused to send phishing emails from Apple’s servers.
Mitigation recommendations
- Treat unexpected account alerts—especially those claiming purchases or urging a call to a support number—with skepticism.
- Verify any alleged transaction directly in your Apple account or with the merchant before taking action.
- Do not click links or call numbers provided in unsolicited security alerts.
- Report suspicious Apple emails to Apple’s abuse team.
BleepingComputer contacted Apple about this campaign but has not yet received a response. The abuse remains possible until mitigations are implemented.